Use Active Directory Administrative Center to Create PowerShell Commands in Windows Server 2012
How can I use Active Directory Administrative Center (ADAC) in Windows Server 2012 to create PowerShell commands?
The PowerShell History Viewer is a new feature in the Windows Server 2012 Active Directory Administrative Center (ADAC). If you have never had a reason to use ADAC before because other AD management tools get the job done, this feature alone makes it worth taking a look.
Many system administrators still haven’t taken their first steps in learning PowerShell, Microsoft’s command-line management system for Windows. Windows administrators tend to be less well versed in command-line management than their UNIX counterparts, as the GUI is often easier to use for one-off tasks – and, let’s face it, command line management hasn’t always been Microsoft’s strong point.
That all changed a few years ago with the introduction of PowerShell, a completely new command-line management system for managing every aspect of Windows configuration and third-party applications. PowerShell is much more sophisticated than previous command line tools on Windows, and as such it comes with a steep learning curve.
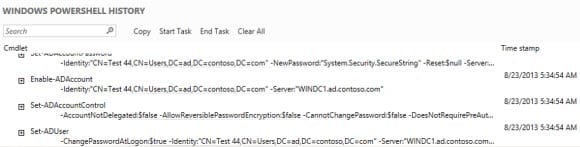
To help system administrators overcome some of the initial hurdles with PowerShell and encourage its use, Microsoft included the PowerShell History Viewer in ADAC. Much like Exchange 2013, ADAC is a GUI tool that runs PowerShell commands in the background to perform the actual tasks, so everything you do with ADAC already has an associated PowerShell command, which can now been seen with the help of the History Viewer.
Using the PowerShell History Viewer in ADAC
Let’s have a look at how you can access the PowerShell commands used to drive ADAC. Log in to Windows Server 2012 and follow the steps below:
- Switch to the Start screen and type Active Directory. At the top of the search results, you should see an icon for the Active Directory Administrative Center. Click the icon to start ADAC.
- In the left pane of ADAC, click ad (local).
- In the central pane, right-click the Users container and select New > User from the menu.
- In the Create User dialog, add the details for a new AD user and click OK.
- At the bottom of ADAC, click on the arrow at the far right of the WINDOWS POWERSHELL HISTORY bar to expand the history.
You’ll see the PowerShell commands used to create the new user above, plus any other commands used in previous ADAC sessions. You can copy these commands directly into the PowerShell console.