Understanding Azure’s New App Configuration Service
One challenge in building software for the cloud is managing all the configuration settings for the services and components in a distributed system. Azure’s new App Configuration service, currently in preview, helps you solve the configuration challenge.
Imagine you’ve built a new solution in Azure consisting of a web application deployed in App Services, an API deployed in Functions, and a background processing service in a virtual machine. You’ve followed best practices and separated your configuration from your code using configuration files, but now you’re looking at three sets of configuration files for the three main components of the system, and some of the settings overlap, so you have some duplication.
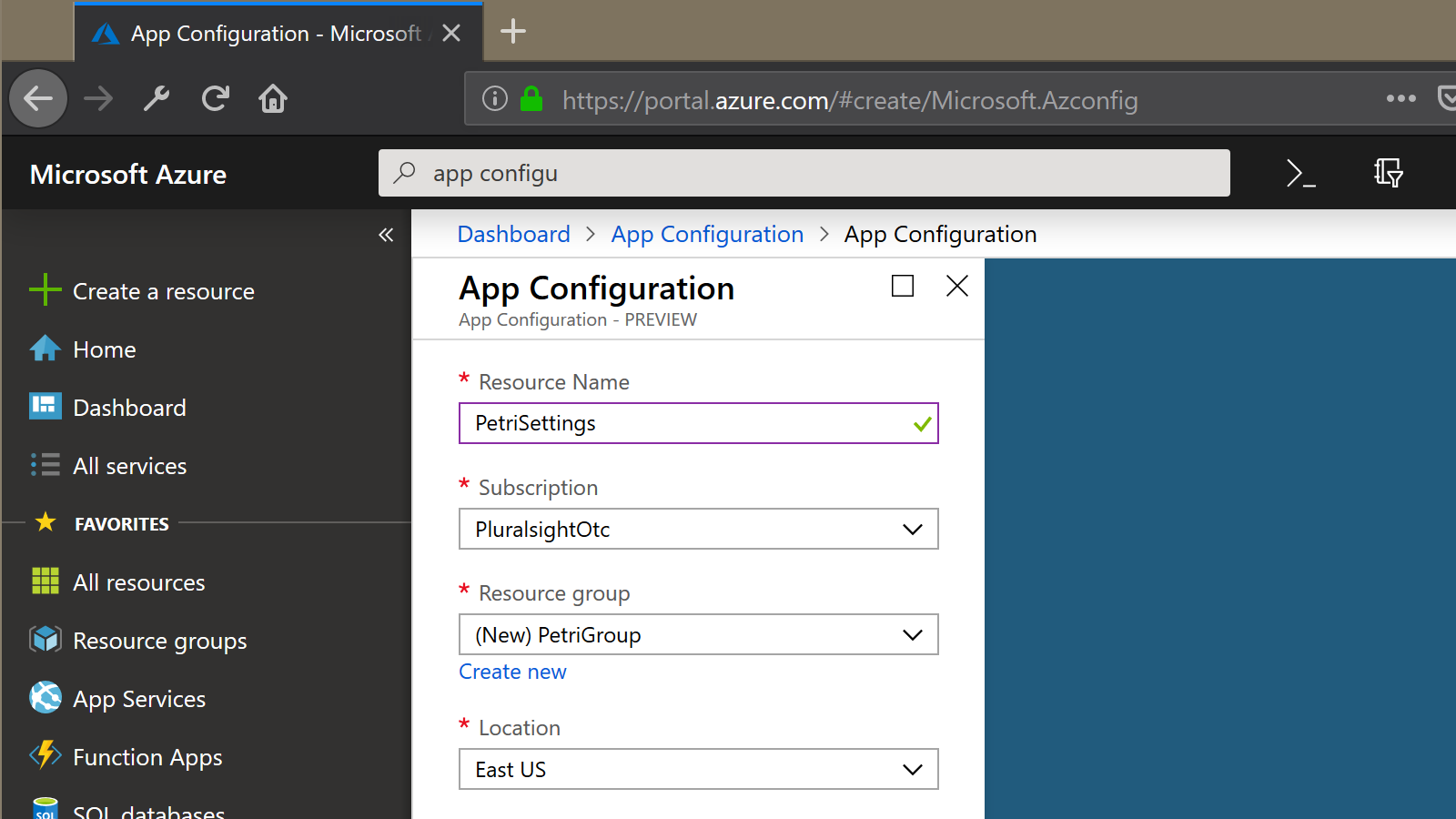
The App Configuration service gives you a central source to store configuration for all three components. Make a change to one key value in the service, and all three components will see the updated setting. App Configuration also gives you encryption in transit and at rest, and point-in-time snapshots so you can compare settings over time, or rollback settings after a failed deployment. The service itself is easy to use. To get started in the portal, search for “App Configuration”. You’ll go through the typical new resource setup in Azure.
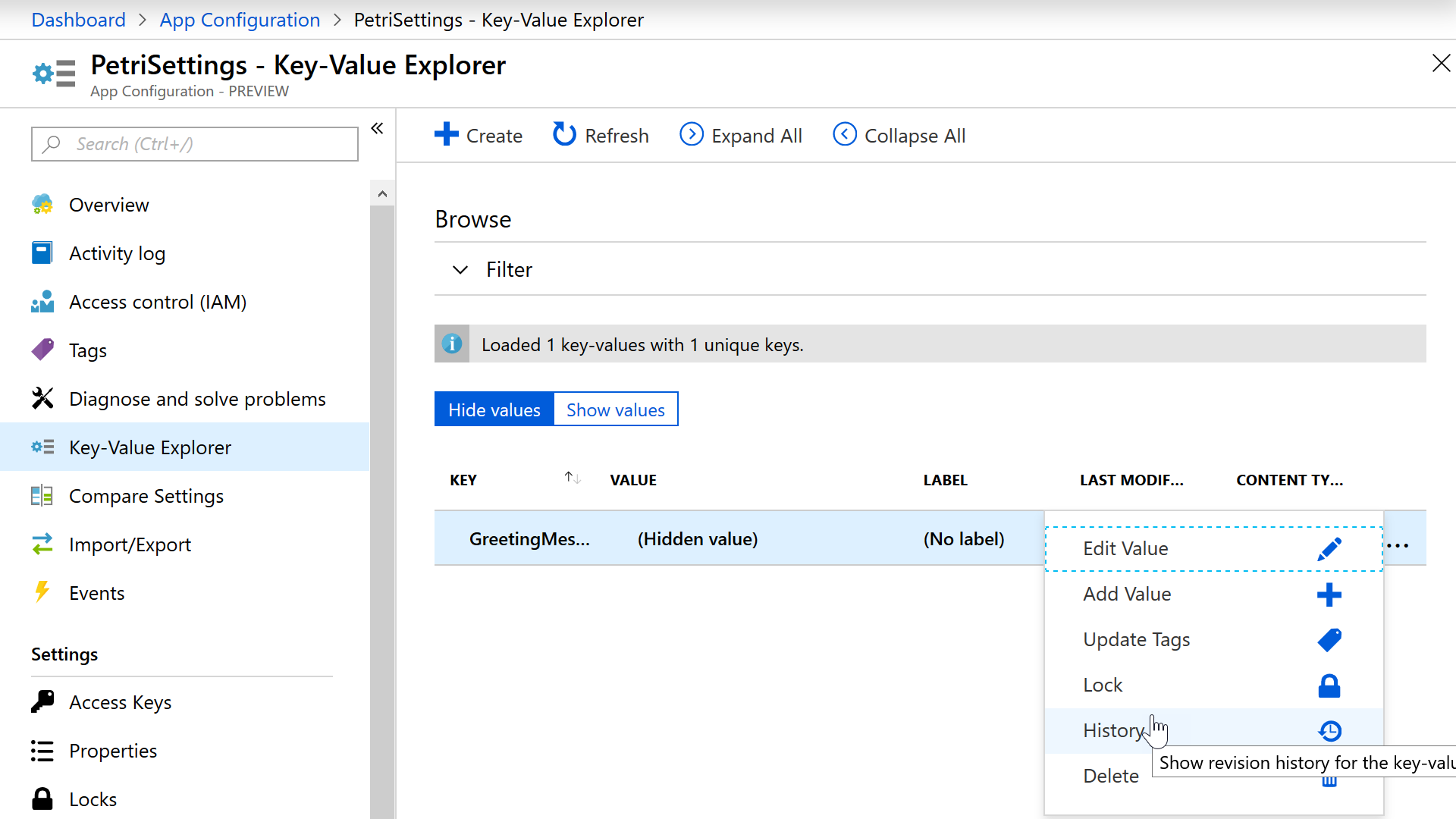
Once your configuration resource is ready, you’ll find primary and secondary connection strings, like you would in a storage account. You can also use the portal’s Key-Value Explorer to begin adding settings into the configuration store. Notice in the menu from the screenshot that you can also tag a setting, lock a setting, and look at the history of changes for a setting.
Microsoft builds NuGet packages with providers to work with the App Configuration service at runtime. Currently, these providers exist for the .NET framework, .NET Core, and Java Spring. As with all resources in Azure, there is also a REST API you can use to interact directly with the service over secure sockets from any programming language or environment.
Here’s how easy it is to work with App Configuration from an ASP.NET Core application. First, we’ll create a new application using the .NET Core command line interface (CLI).
Next, we’ll use the .NET Core User Secrets tool to store the connection string for our new App Configuration service into the local application’s configuration (in a production environment, this would be the setting we use to bootstrap all other configuration settings by placing the connection string into an environment variable).
We’ll also need to add a reference to the AzureAppConfiguration provider for .NET Core (as a preview, the version will change).
Now we can tell ASP.NET Core to include the AppConfiguration service as a source for key-value settings. We’ll do this by modifying the code inside Program.cs and customize our web host builder with a call to AddAzureAppConfiguration.
Throughout the rest of the application, we’ll now have key value settings from the App Configuration service available through the IConfiguration service of ASP.NET Core. Here’s an example of using a setting directly from a Razor page.
One obvious question about the new App Configuration service would be how App Configuration relates to Azure Key Vault. Key Vault can store secrets for application configuration, as well as certificates and encryption keys. Key Vault continues to be the ideal place for well-protected settings and crypto operations backed by a hardware security module. Applications and services can have the best of both worlds by using both Key Vault and App Configuration as configuration sources.