Microsoft said on Monday that it is aware of an unpatched vulnerability in the Windows Adobe Type Manager Library that is actively being exploited by hackers. As part of a new security advisory, Microsoft warns that there are two remote code execution (RCE) flaws rated Critical in the library that can be exploited in several ways.
A hacker could convince a user to open a specially crafted document or just view it in the File Explorer preview pane. The RCE flaws are in the way Windows handles a specially crafted multi-master font. The Adobe Type Manager library is built-in to Windows and it is used to render PostScript Type1 fonts. Microsoft says that all currently supported versions of Windows are affected and that it is currently working on a fix. Windows 7, which recently reached end-of-life, is also affected.
Windows 10 is better protected
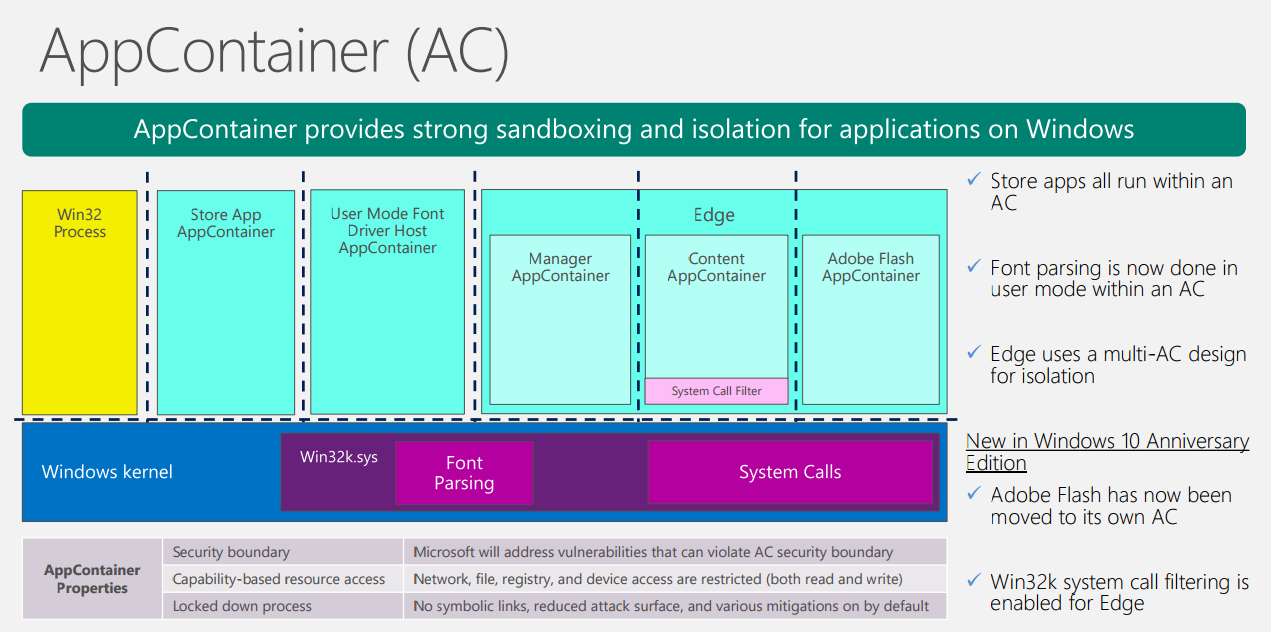
Because of the way fonts are processed in supported versions of Windows 10, a successful attack would result in the malicious code running in a user-mode AppContainer sandbox with limited privileges and capabilities. Starting in the Windows 10 Anniversary Update (version 1607), font parsing is carried out in AppContainer instead of the operating system kernel. The idea is to stop hackers gaining privileged access to Windows.
Mitigating the Adobe Type Manager Library vulnerability
While Microsoft is working on a patch, which will hopefully be available by April’s Patch Tuesday or before, there are several ways you can protect Windows. In versions of Windows 10 released before the Windows 10 Anniversary Update, renaming atmfd.dll and restarting Windows provides protection. Later versions of Windows 10 don’t have atmfd.dll but remain vulnerable. Windows 8.1 systems can be protected by disabling ATMFD using the registry. For more details on these mitigations, see Microsoft’s security advisory here.
Windows 10 version 1607 and later systems can be partially protected by disabling the preview pane in File Explorer and disabling the Web Distributed Authoring and Versioning (WebDAV) client service. Like the WebDAV mitigation, disabling File Explorer’s preview pane prevents Windows displaying OpenType (OTF) fonts but it doesn’t prevent a local user running a specially crafted program to exploit the vulnerability.
Microsoft says that disabling the WebClient service can protect Windows by blocking what it thinks is the most likely remote attack vector for the vulnerability. But disabling the WebClient service doesn’t stop attackers exploiting the type library flaw by running programs stored on the device or Local Area Network (LAN). If you decide to disable the WebClient service, any services that depend on it will not start. And WebDAV shares won’t be accessible from the local device.
No update for Windows 7 customers without ESU license
Microsoft has said that organizations with an extended security updates (ESU) license for Windows 7, Windows Server 2008, and Windows Server 2008 R2 will receive a fix when it’s ready for deployment.