Microsoft, Cloudflare Disrupt Global RaccoonO365 Phishing-as-a-Service Operation
Joint operation seizes hundreds of domains linked to RaccoonO365.

Key Takeaways:
- Microsoft and Cloudflare dismantled a major phishing-as-a-service operation.
- RaccoonO365 targeted Microsoft 365 users worldwide with fake brand emails.
- Court-backed action shut down hundreds of domains tied to the scheme.
Microsoft and Cloudflare have teamed up to disrupt RaccoonO365, a notorious phishing-as-a-service (PhaaS) operation. The phishing platform enabled cybercriminals to steal thousands of Microsoft 365 credentials across nearly 100 countries.
Microsoft explained that the RaccoonO365 hacking group (also known as Storm-2246) has been active since July 2024. Earlier this month, Microsoft’s Digital Crimes Unit (DCU) seized 338 websites linked to this service. The seizure was authorized by a court order from the Southern District of New York.
How do the RaccoonO365 phishing kits work?
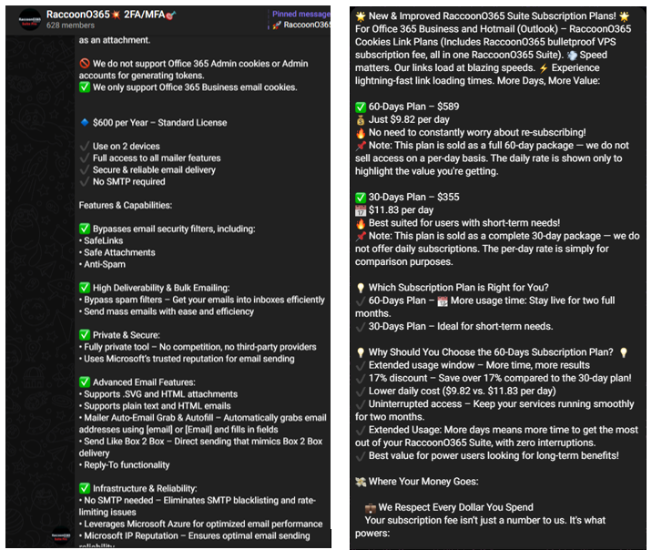
According to Microsoft, the RaccoonO365 phishing kits have been used to steal at least 5,000 Microsoft credentials from across 94 countries since July 2024. These kits have been used to target atleast 2,300 US based organizations in April 2025. RaccoonO365 had been using a private Telegram channel to advertise these subscription-based phishing kits.
The cybercriminals offered a pricing model that included a $600 annual subscription, along with cheaper short-term options for 30 and 60-day access. They used various phishing techniques to target the victims, including impersonating DocuSign, SharePoint, Adobe, and Maersk in emails.
“RaccoonO365 phishing emails were crafted to impersonate trusted brands or organizations within the targeted company, using familiar workplace themes to exploit trust and create urgency. File names were designed to mimic routine communications — such as finance or HR documents, policy agreements, contracts, and invoices,” Microsoft explained. “In some cases, the emails went further, incorporating the recipient’s name into links or attachments to enhance credibility. This social engineering tactic increases the likelihood that users will click, believing the message is legitimate.”
Microsoft’s security recommendations
Microsoft advises that organizations should enable multi-factor authentication (MFA) to make it harder for attackers to access accounts even if credentials are stolen. Moreover, IT administrators must educate employees about phishing tactics so they can recognize suspicious emails and avoid clicking on malicious links.
Lastly, security teams should monitor for unusual login activity, especially from unfamiliar locations or devices. It’s also recommended to use advanced email filtering and anti-phishing tools to block malicious messages.






