Microsoft Defender ATP Adds UEFI Scanner to Detect Firmware-Level Attacks
As the antimalware protections in Windows have become more robust over the years, hackers have increasingly turned their attention to firmware. Sometimes referred to as persistent BIOS attacks, firmware-level malware is difficult to detect, and it is also difficult to remove.
Once a hacker has a foothold in firmware, they can disable security protections like antimalware software. Reinstalling the operating system won’t help on a device infected with malicious firmware code. So, like in any other aspect of computer security, prevention is better than cure.
What is UEFI?
Unified Extensible Firmware Interface (UEFI) replaces the BIOS on modern computing devices. PCs manufactured in the last five years use UEFI instead of BIOS. UEFI is a specification for defining device firmware that interacts with the operating system. It has many advantages over BIOS, including features like Secure Boot, remote diagnostics and repair without an operating system installed, and it can use large disk partitions.
Secured-Core PCs
Windows 10 already has several defenses built-in to protect UEFI against attack. Windows Defender System Guard uses Dynamic Root of Trust (Secure Launch) and hypervisor-level runtime attestation to protect UEFI. But these features have specific hardware requirements that aren’t met by all PCs.
To make it easier for organizations to utilize advanced security protections like those included with Windows Defender System Guard, last year Microsoft announced that it was working with hardware partners on new device security requirements to protect against targeted firmware attacks.
In partnership with PC and chip makers, Secured-Core PCs require devices to meet new standards that follow isolation best practices and that have minimal trust of firmware. The devices are intended for industries whose workers handle intellectual property, customer or personal data, including Personally Identifiable Information (PII).
Secured-Core PCs aren’t intended for everyone because they require hardware, management infrastructure, and expertise that isn’t readily accessible to consumers and small businesses. But for organizations that have the resources to deploy Secured-Core PCs, they provide a more robust and secure computing experience.
Microsoft Defender ATP UEFI scanner
Microsoft Defender Advanced Threat Protection (ATP) is the enterprise version of Windows Defender, the antimalware suite of technologies built-in to Windows 10. The new UEFI scanner included in Microsoft Defender ATP performs a dynamic analysis on firmware at runtime. The inspection process uses three components to detect for anomalies:
- UEFI anti-rootkit
- Full filesystem scanner
- Detection engine
Microsoft Defender ATP accesses the firmware using the Serial Peripheral Interface (SPI). SPI flash memory is used to store firmware and it isn’t normally accessible from main memory. Once the device’s chipset has been identified, Microsoft Defender ATP selects the right hardware protocol to read the contents of SPI flash memory. Then the filesystem scanner can analyze content inside the firmware while the detection engine identifies exploits and suspicious activity.
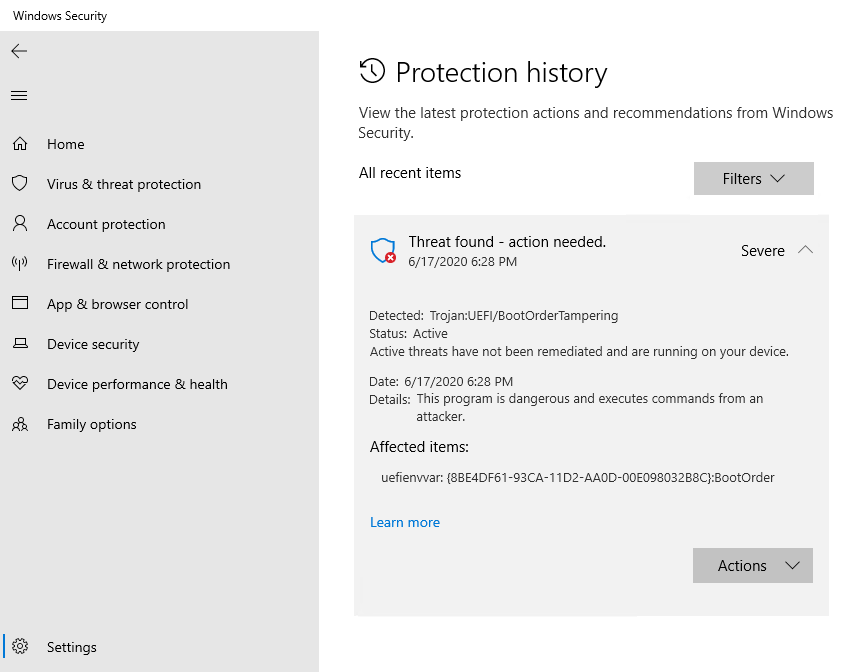
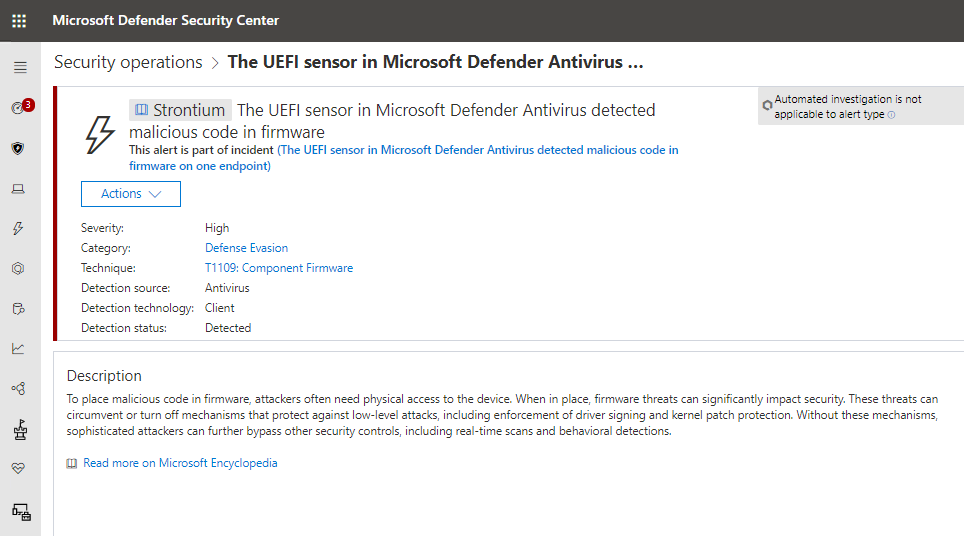
Microsoft Defender ATP might flag a problem because it detects runtime activity like a suspicious driver loading or because an anomaly was detected by a periodic firmware scan. Because Microsoft Defender ATP is built-in to Windows 10 Enterprise, any issues found can be seen under Protection History in Windows Security. Organizations with Microsoft Defender ATP licenses will see threats raised in the Microsoft Defender Security Center.
Extra protection in addition to hardware-backed security features
Microsoft Defender ATP’s UEFI scanner provides additional protection to hardware-backed security features like Secure Launch and hypervisor-level runtime attestation. Defense-in-depth security is always more effective than relying on one security technology. But the UEFI scanner is also a useful addition for customers using Microsoft Defender ATP on PCs without hardware-backed security capabilities.