Microsoft Releases Azure AD Authentication Support for Windows Admin Center in Azure

Microsoft has recently announced that Azure Active Directory authentication support is generally available for organizations using Windows Admin Center in the Azure management console. This feature is designed to make it easier for customers to manage their domain and non-domain joined server infrastructure.
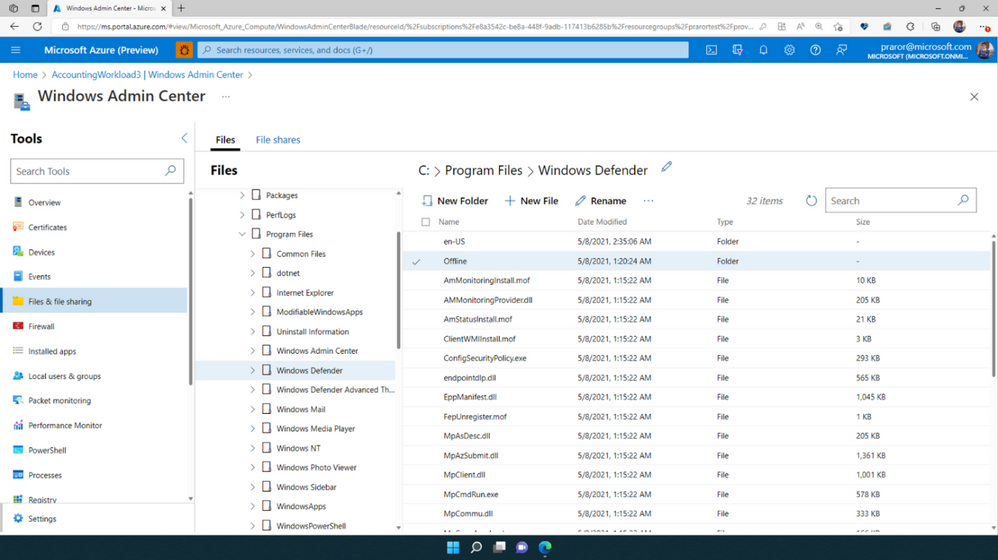
Last year, Microsoft announced that Windows Admin Center can now help IT admins manage their Azure Arc-enabled infrastructure directly from the Azure portal. The feature lets them manage Arc-enabled Windows Servers and virtual machines as well as Azure Stack HCI systems. It should enhance security and eliminates the need to remotely access servers or clusters via public IP address, VPN, and inbound connectivity.
Up until now, Windows Admin Center in Azure allowed IT Pros to use their local admin password to sign in and manage Windows virtual machines (VMs). With Azure Active Directory authentication support in Windows Admin Center, administrators can use Azure AD credentials to log into their Windows Server VMs.
“This enables single sign-on (SSO) and seamless management for your Windows Server instances using Azure AD authentication with Windows Admin Center in Azure. If your Azure AD identity is part of the “Windows Admin Center Administrator Login” Azure RBAC role, you get access to the full suite of management capabilities that Windows Admin Center provides in the Azure Portal,” explained Alex Weinert, Director of identity security at Microsoft.
Getting started with Azure AD authentication support for Windows Admin Center in Azure
Keep in mind that this capability is only available for managing VMs running Windows Server 2016 or higher and Azure Arc-enabled servers running in on-premises environments. Moreover, the servers should be workgroup, domain-joined, or Azure AD-joined.
Microsoft has detailed a couple of steps to configure Azure AD authentication capabilities in the Windows Admin Center in Azure. If you haven’t done it yet, you can follow the step-by-step guides to deploy Windows Admin Center on Windows Server Azure IaaS VMs or Arc-enabled infrastructure.



