Introduction to Azure Active Directory Auditing
In today’s Ask the Admin, I will provide a brief overview of Azure Active Directory (Azure AD) auditing in the new administration portal.
Microsoft has gradually been moving Azure features to the new admin portal. One of the latest is Azure AD, which until last year, had to be managed using the classical web management portal or PowerShell. In November 2016, Microsoft added detailed audit logs to the portal for those with Azure Premium AD or Enterprise Mobility Suite subscriptions. If you are not signed up for one of these plans, you can get a free 30-day trial of Azure Premium AD.
View Audit Logs in Azure AD
To view the log information for your tenant, you will need to log into Azure with an administrator account. Azure AD can be accessed by clicking the hamburger menu on the left of the portal and selecting Azure AD from the list of options. If you do not see it, click More services > at the bottom and search for Azure Active Directory.
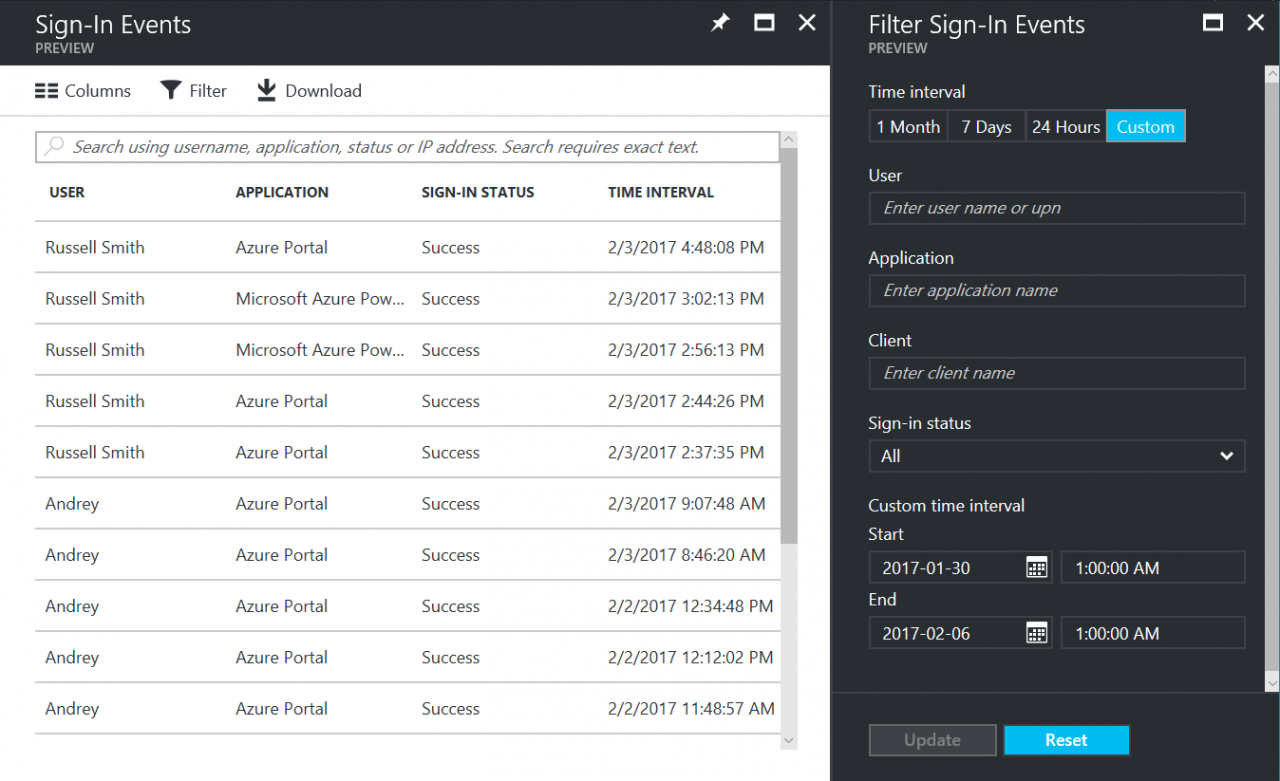
Once you have opened the Azure AD panel, scroll down to ACTIVITY. You will see two options, Sign-ins and Audit logs. Audit logs will show all available logs. If you are interested in user login information, then click Sign-ins. Audit logs and Sign-ins provide customized views of the available log data.
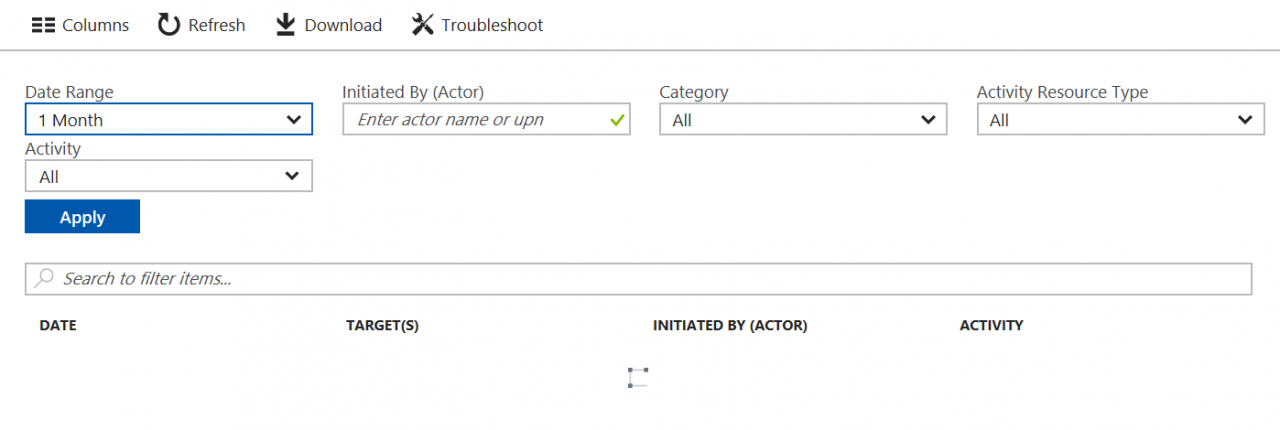
If you need more than sign-in data, Audit logs provide a rich search and filtering experience. Sign-in data is also included as part of audit logs. Both views allow you to search based on time period, user, event category, and other criteria. The search results can be filtered based on data, time, and the actor’s user principal name (UPN).
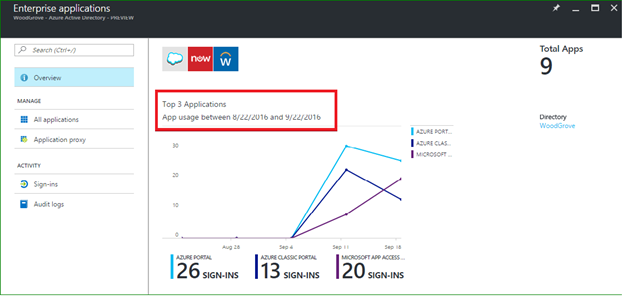
There are also contextual audit and sign-in logs built into the portal, so you do not necessarily need to come to Sign-ins and Audit logs. For example, the User Management blade provides access to pre-filtered sign-in data. This shows user sign-in trends for the past month. If you are in the Enterprise applications panel, you will see information about the top three apps in your organization.
In this article, I provided an overview of the auditing features available in Azure Active Directory.




