How to Join the Windows Insider for Business Program
Microsoft announced and launched the Windows Insider Program on September 30, 2014, along with the announcement for Windows 10. Soon after, they received a good deal of feedback from IT Pros in the Windows Insider Program (WIP) that were looking for specific and detailed assistance on how the WIP could work in their business environments.
Based on this feedback, Microsoft launched the Windows Insider for Business Program. Although the underlying WIP is the same for both parties, the difference with the Windows Insider for Business Program (WIBP) is catering to another audience, IT Pros in the business enterprise.
How to Join the Windows Insider for Business Program
This post will demonstrate how you can join the WIBP and start deploying Windows 10 and Windows 11 insider builds in your enterprise.
Step 1 – Register for the Windows Insider Program
Let’s browse the Windows Insider for Business Program website.
Microsoft recommends you register with your Azure Active Directory (AAD) work account. When you register with your work account, you, as an IT Pro, will be able to manage the feedback on behalf of your organization to help shape the future of Windows for your company’s needs. You must register with your AAD account to manage Insider builds centrally across your organization.
However, you also have the option to register with your personal Microsoft account. This is essentially the Windows Insider Program for consumers. If you are not blocking users from joining the WIP, they can do so with their personal Microsoft account.
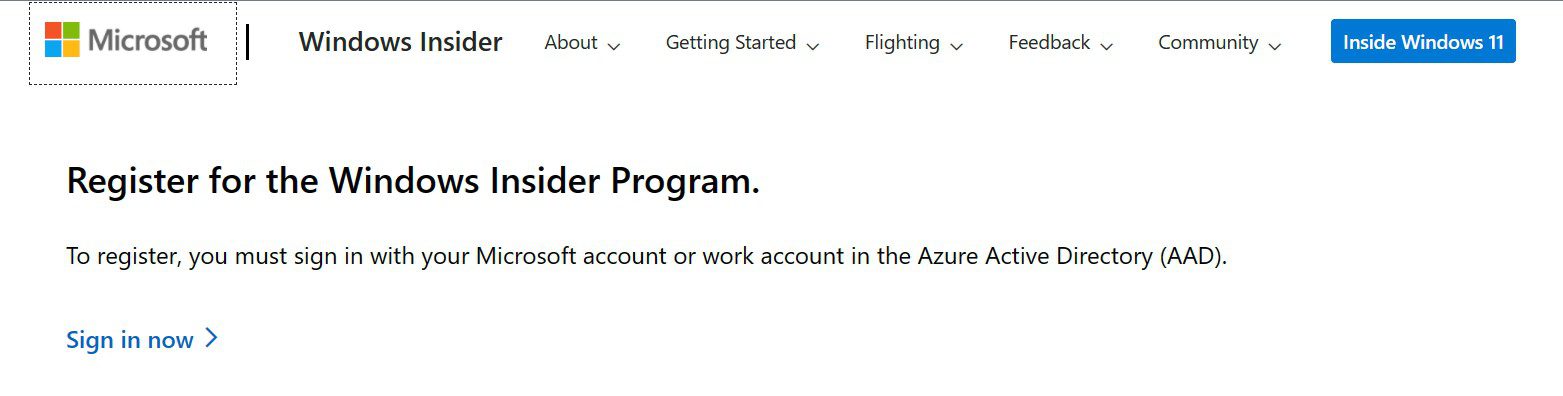
Click Registration details. This will take you to the Registration page.
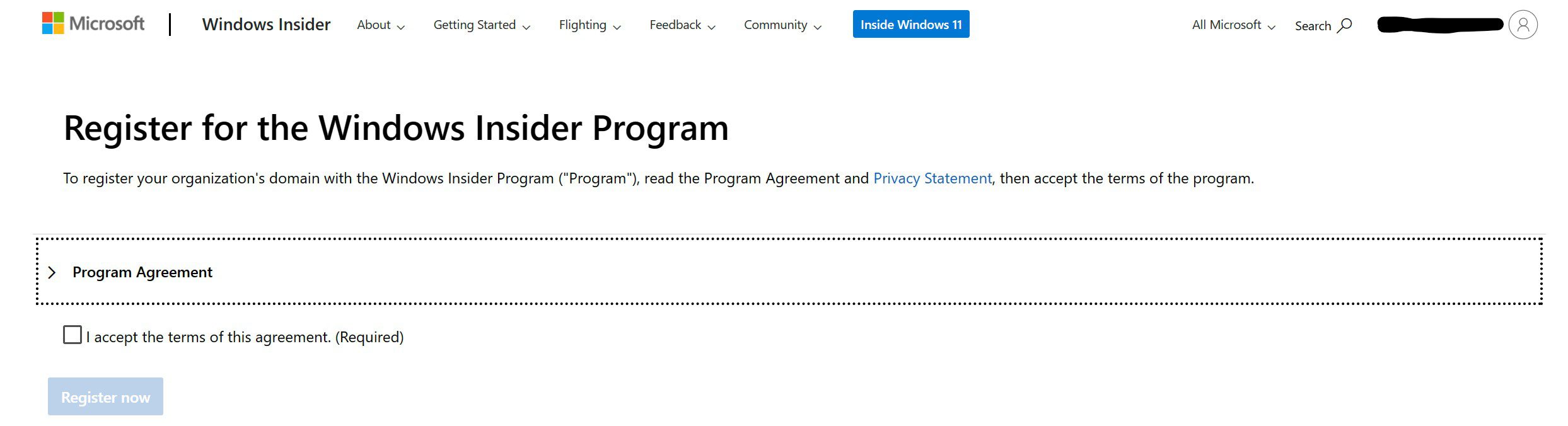
Then, click Sign in now and enter your AAD credentials. You will then be presented with the Program Agreement.
Step 2 – Start Flighting
Register your AAD domain with Microsoft
To register a domain, you must have registered for the program with your work account in Azure Active Directory (AAD), and you must be assigned a Global Administrator role on that AAD domain. As the only available AAD domain to me is already registered, let’s move on to joining devices. But don’t worry, it’s very straightforward.
Join your devices to your AAD domain
As part of normal operations and design with a more native AAD infrastructure, many of your devices will likely already be joined. But you can always log into a device and go to Settings > Accounts > Access work or school and select Join this device to Azure Active Directory and log in with your AAD account. You can get more assistance with these steps via these Microsoft Azure Docs.
Create Policies for your device groups
There are many ways, at this point, to proceed to create policies to start a test group of devices. You can use Group Policy in your on-premises environment or use cloud tools like Intune (Azure Portal) or the Microsoft Endpoint Manager. I will go through the basics of using the latter to create a policy for the purpose of previewing the next feature update for Windows 10.
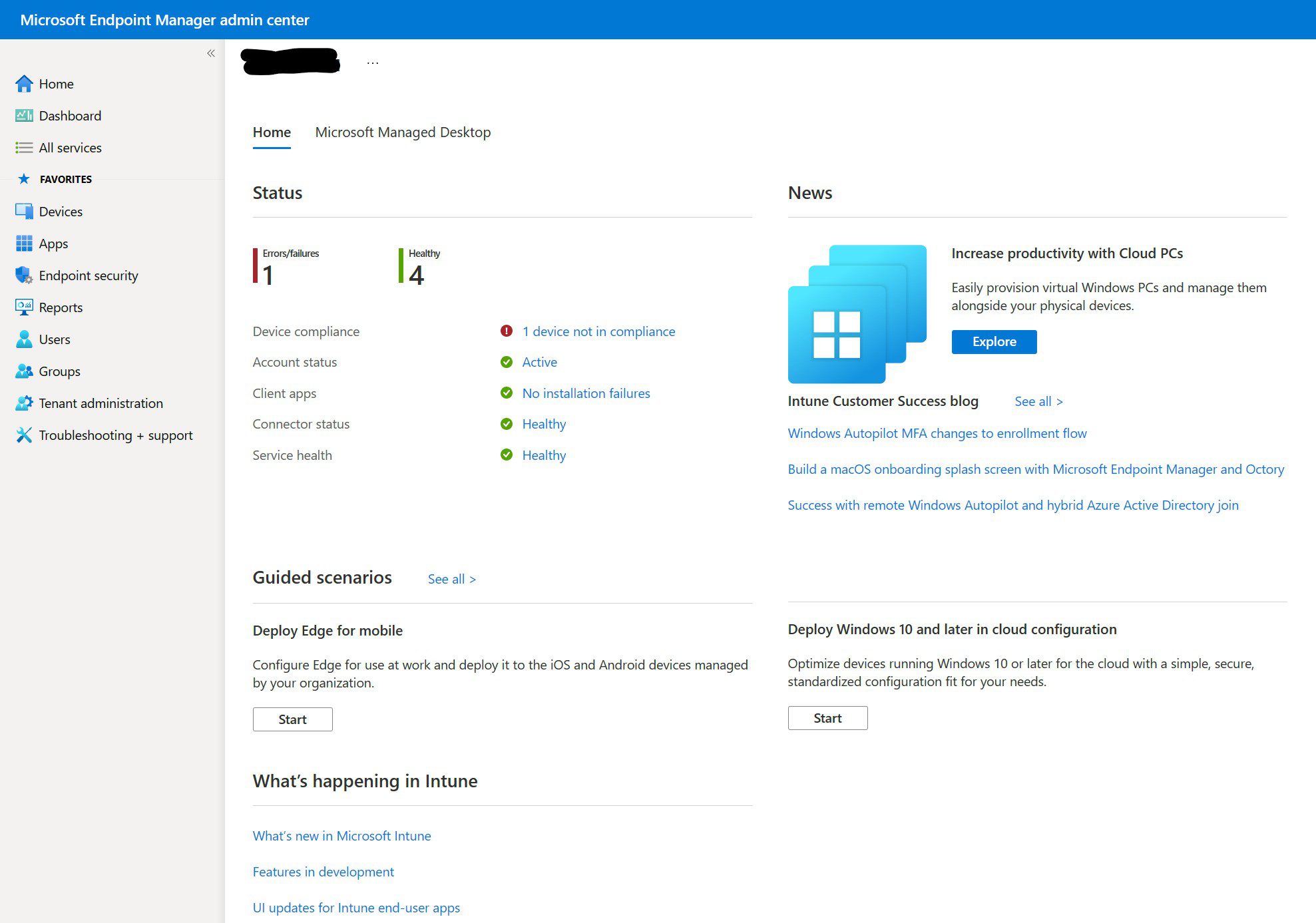
First, log in to the portal at https://endpoint.microsoft.com/
From here, click the Devices category on the left.
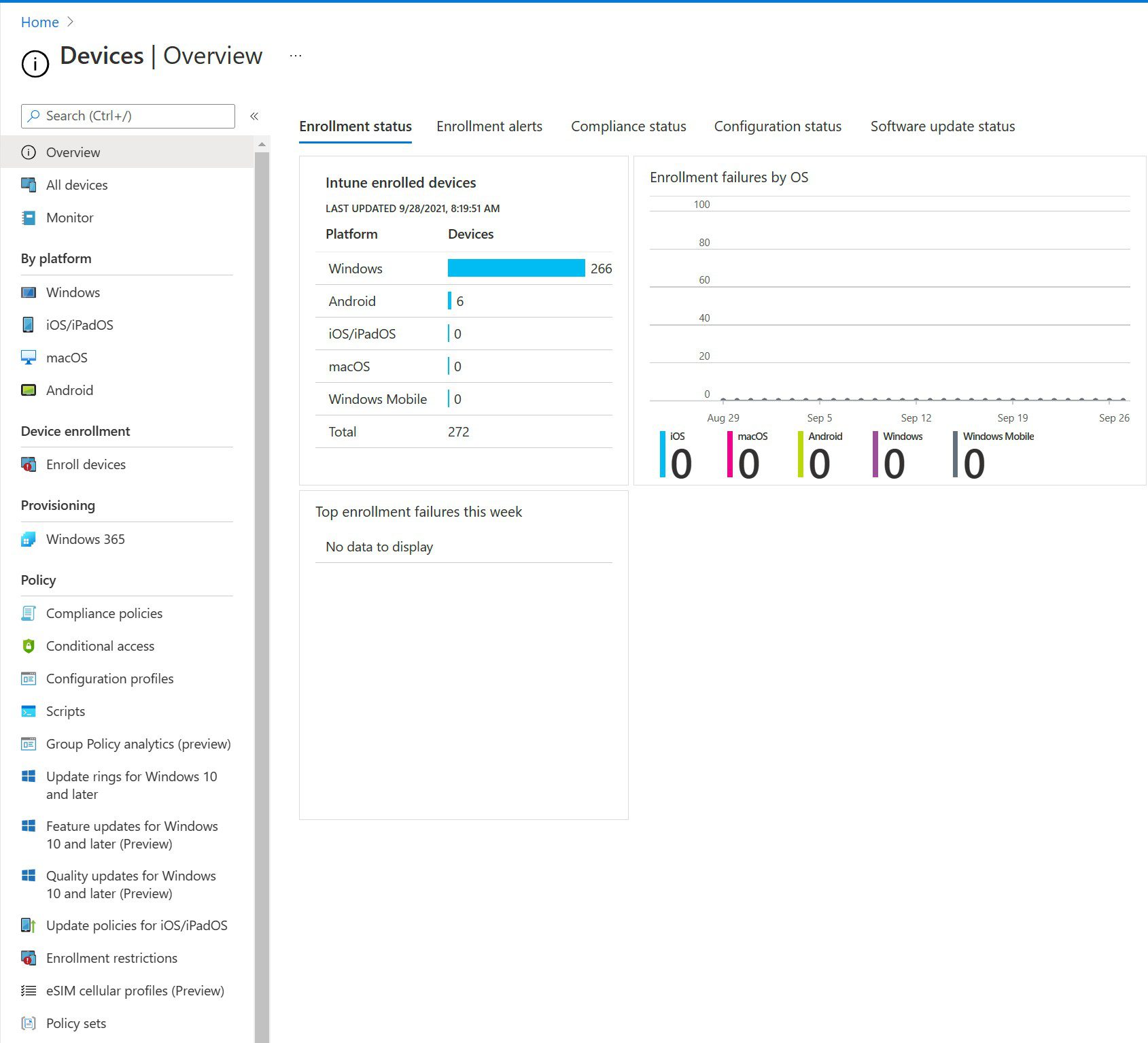
The next step is to click the ‘Update rings for Windows 10 and later’ item under the Policy category heading and click Create profile.
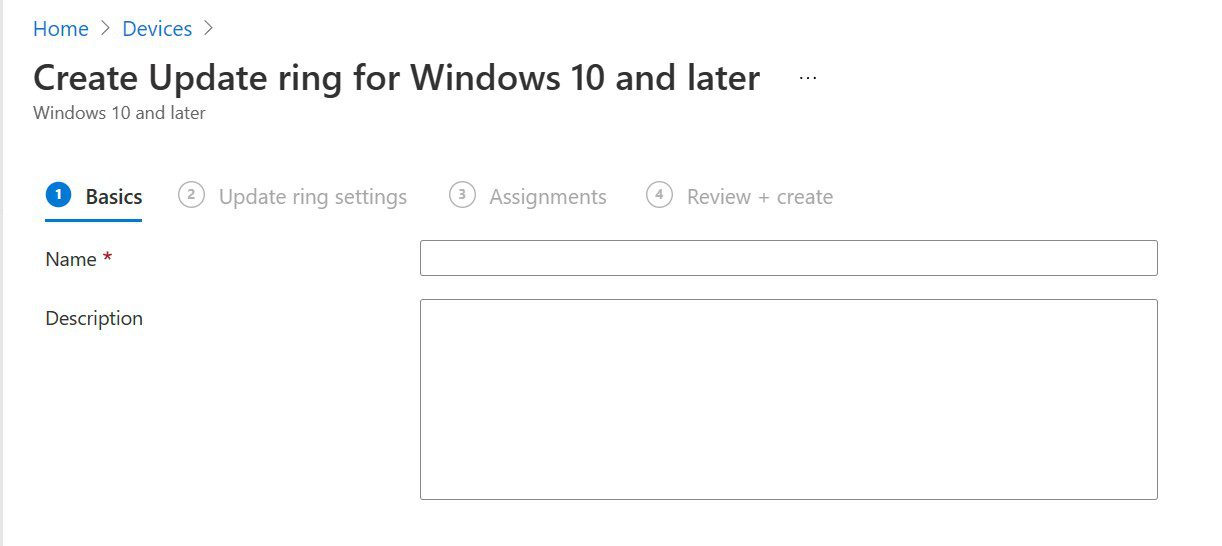
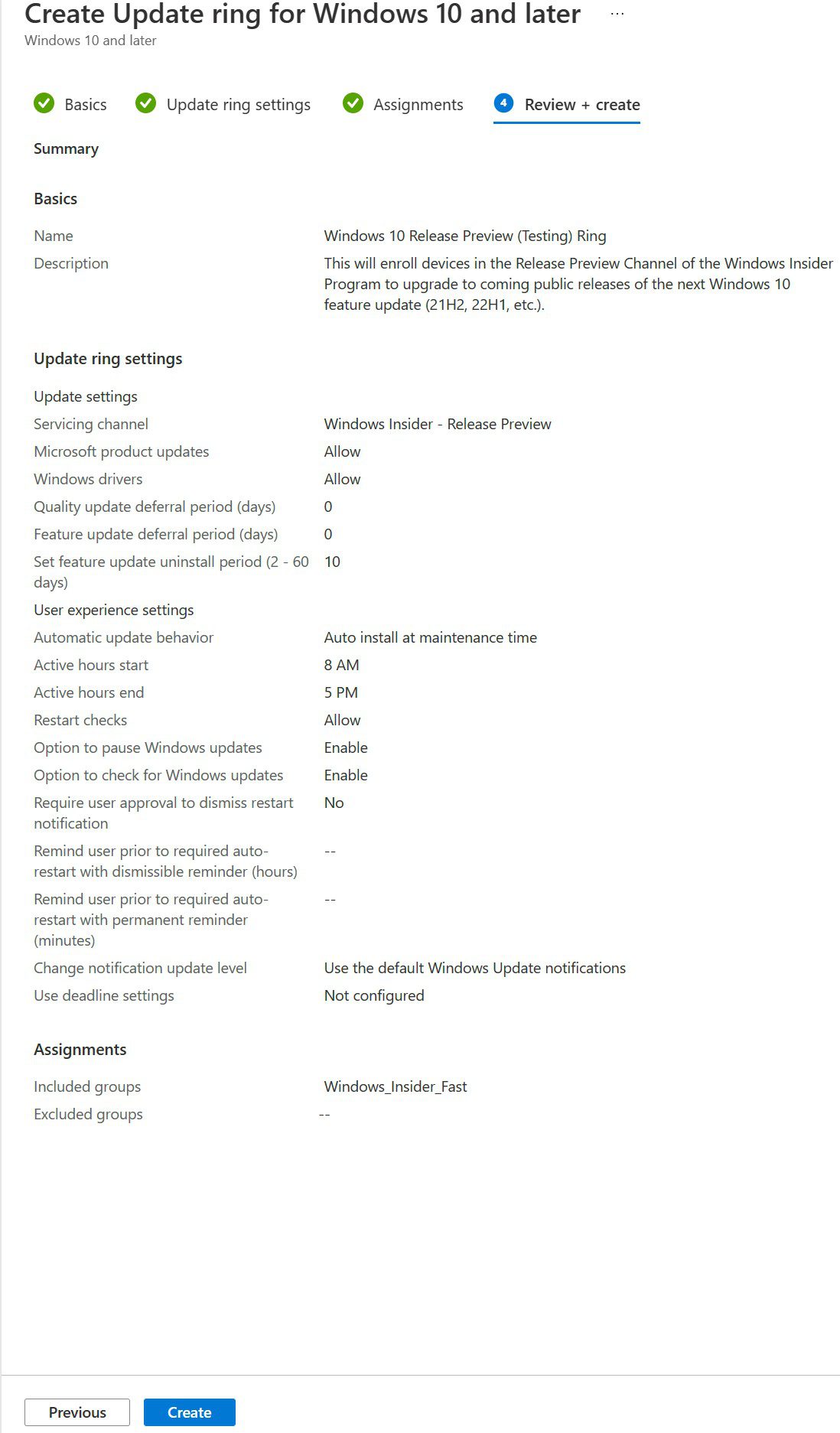
We’ll give it a descriptive Name and Description and click Next.
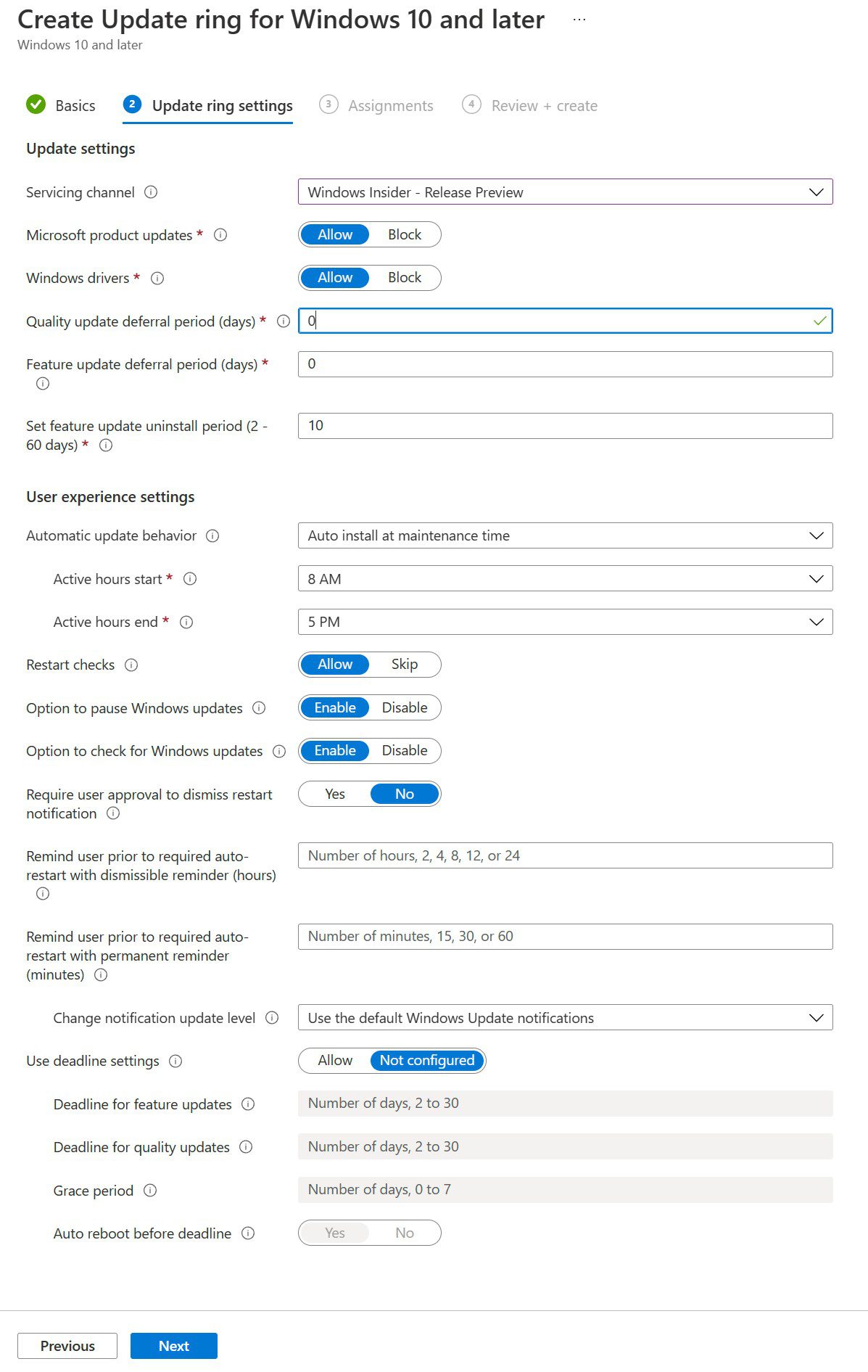
As you can see, there is a multitude of customization options to suit your environment and your users’ needs.
The key setting is the first item, the Servicing channel. This is where you can specify the current channel options in the Windows Insider Program, namely the Dev (Fast), Beta (Slow), and Release Preview channels. We are choosing Windows Insider – Release Preview. Click Next.
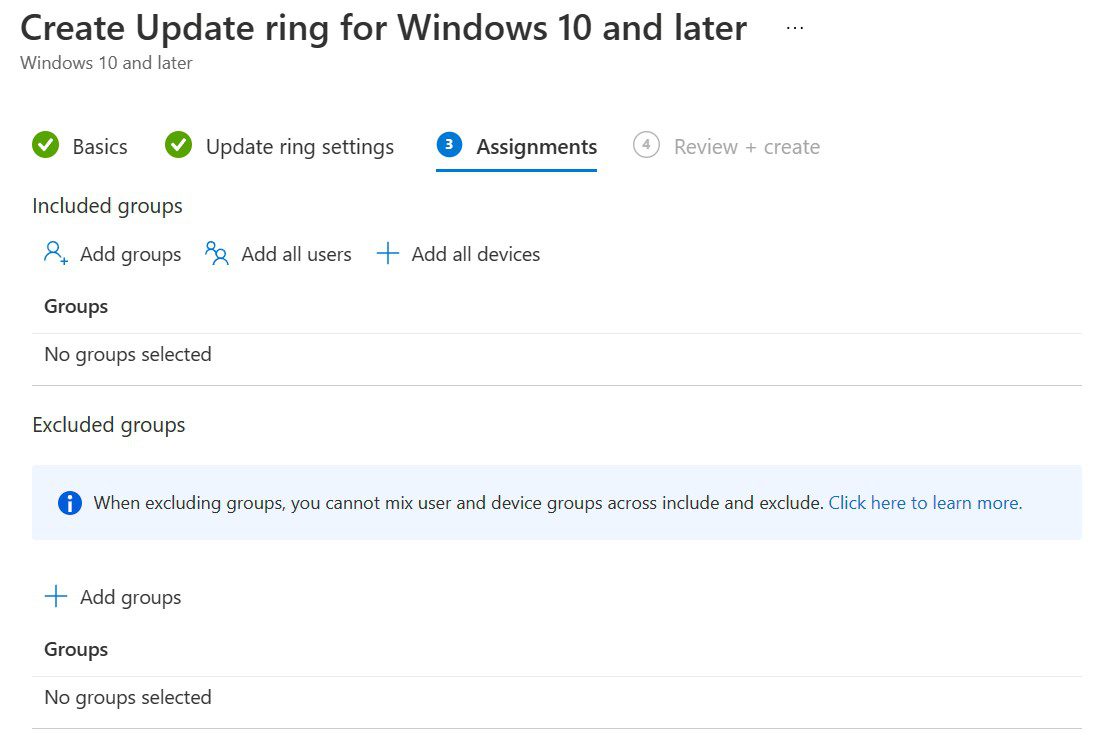
Here, on the Assignments step, you can assign this policy to all users (not necessarily recommended) or to groups (recommended).
You simply click Add groups, select the group(s) you want to assign this policy to, and click Select at the bottom. Then, review the details and click Create at the bottom.
Assign your pilot devices to Groups
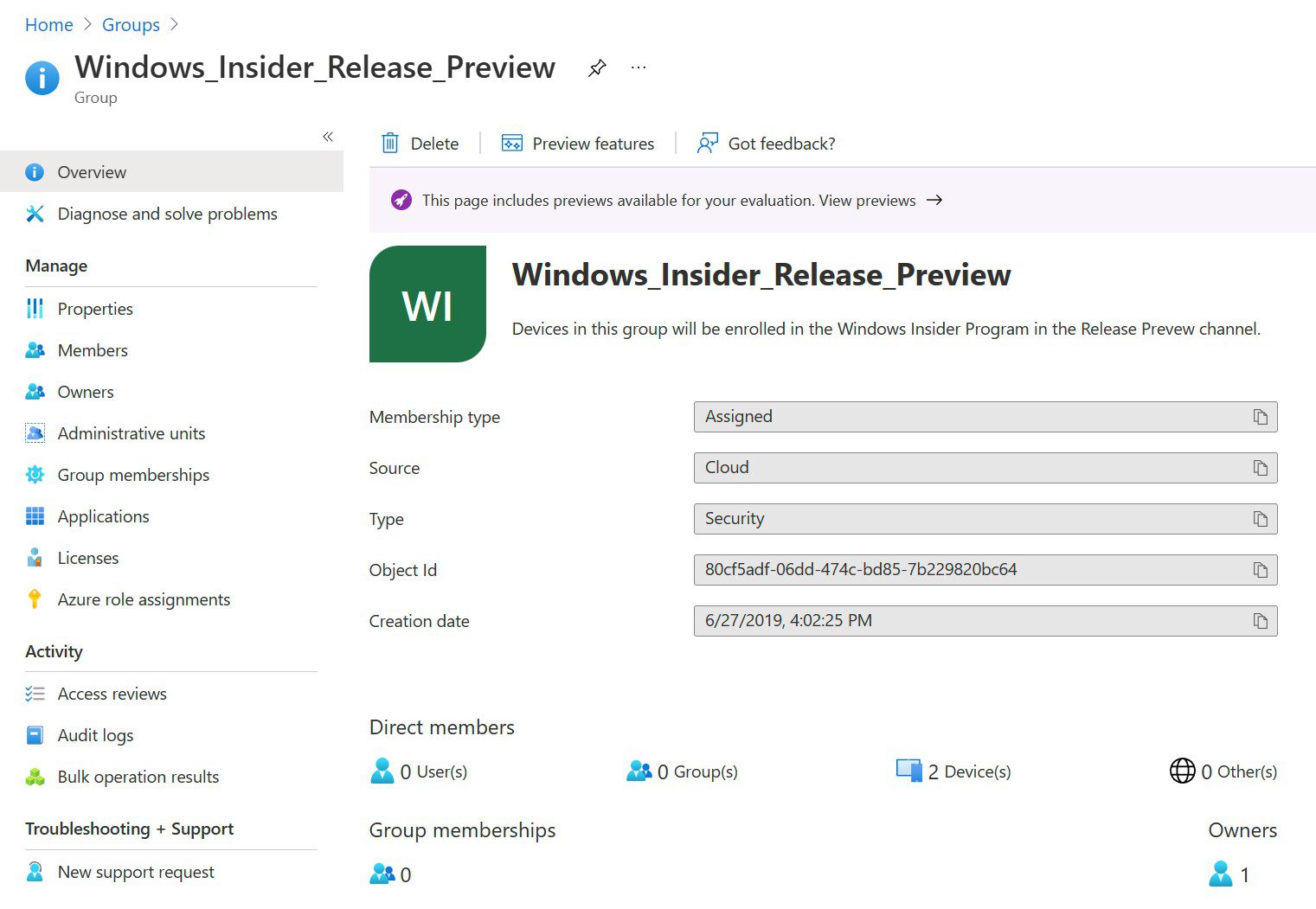
Now, we can add an AAD-joined device to the group. I will click on Groups along the left side and locate the group by searching.
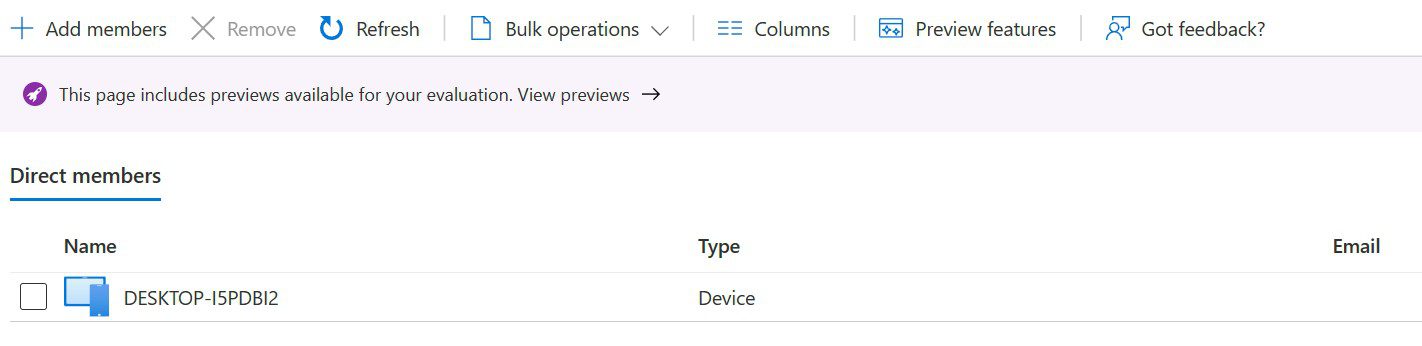
Click Members on the left and click Add members. I obtained my test device name and added it to the group.
Verify and test on your Devices
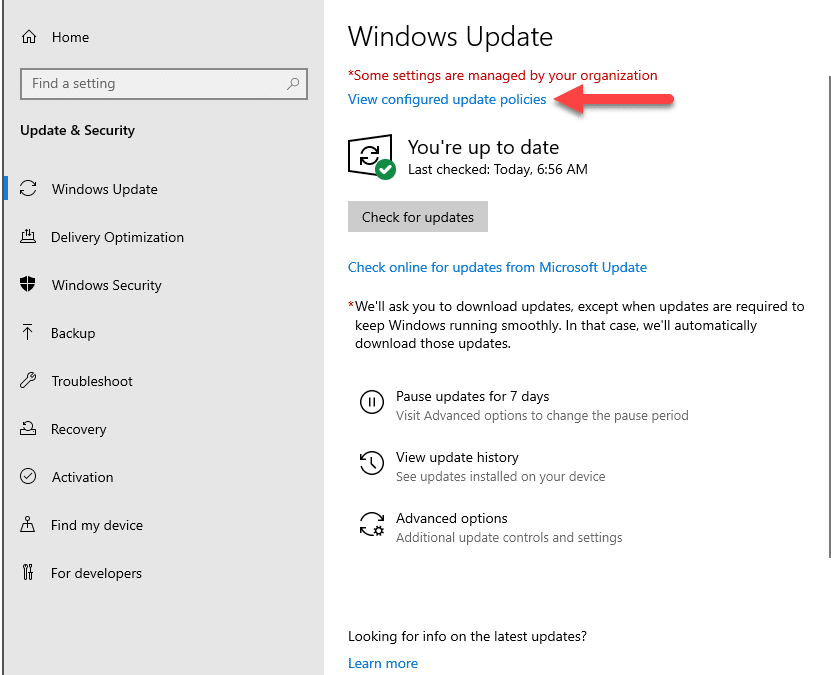
At this point, you can go to your test device(s) and reboot them. Sometimes, it takes an hour or two for the changes and group membership details to take effect. But eventually, you can go to Windows Update and discover that the device is now showing as being controlled/configured by your organization’s policies. (Note: Unfortunately, I do not have this configuration available in my available tenant.)
So, there you go! To expand upon this uncomplicated design, you can create as many update ring policies as possible in MEM, and associated Groups in Intune to control your pilot and initial deployments of Insider builds to your test group. If you have any questions on this process, please feel free to leave a comment for me or leave me a note on Twitter!