How to Copy Active Directory Groups from One User to Another with PowerShell
Creating new Active Directory users isn’t difficult, either with the GUI tools or PowerShell. But in large directories, creating consistent user objects can be an issue when the process is manual. With a little automation, you can make sure that new user objects are created with the right group memberships and attributes by copying them from a template account.
As I wrote recently on Petri, creating new Active Directory (AD) users with PowerShell is easy using the New-ADUser cmdlet. In that article, I showed you how to copy users, including AD attributes like office address, department, job title, and other details with the help of the New-ADUser cmdlet and the -Instance parameter.
The New-ADUser cmdlet is great for creating new user accounts and copying attributes. But as we saw in the previous article, it doesn’t copy users’ group memberships. To do that, we needed to manually add any new users to groups using the Add-ADGroupMember cmdlet. And while that’s OK, it adds an extra couple of steps.
In this article, I’m going to show you how to copy group membership from one AD user account to another. We’ll use an account as a template (accountsuser) and then create a new account (Fleur Wade) with the same group membership as the template user.
Create a new user account and copy group membership using PowerShell
Fleur will be working in accounts and I want to make sure that she is a member of the same groups as my ‘accounts’ template user. Let’s start by using the New-ADUser cmdlet to create Fleur’s account:
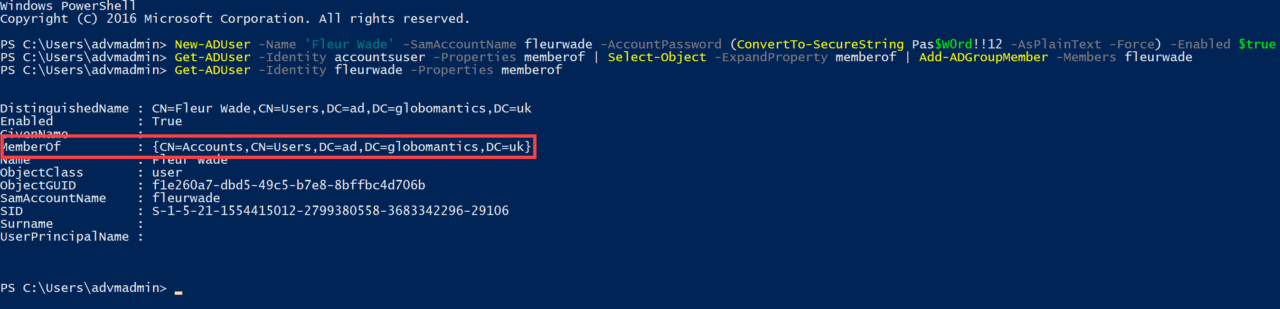
New-ADUser -Name 'Fleur Wade' -SamAccountName fleurwade -AccountPassword (ConvertTo-SecureString Pas$W0rd!!12 -AsPlainText -Force) -Enabled $true
I already have a template user account for users in the Accounts department. For more details on how I set up the accounts user template, see How to Copy Active Directory Users with PowerShell on Petri.
The next step is to enumerate the group membership of the template user (accountsuser) and then add Fleur’s account to the same Active Directory groups. We use the Get-ADUser cmdlet to enumerate which groups accountsuser belongs to. Select-Object is used to create a new object with all the information required by Add-ADGroupMember. Add-ADGroupMember is then used to add Fleur’s account to the same groups that accountuser is a member of.
Get-ADUser -Identity accountsuser -Properties memberof | Select-Object -ExpandProperty memberof | Add-ADGroupMember -Members fleurwade
My template account is a member of the ‘Accounts’ group. To check that Fleur’s account has added to the Accounts group, we can use Get-ADUser:
Get-ADUser -Identity fleurwade -Properties memberof
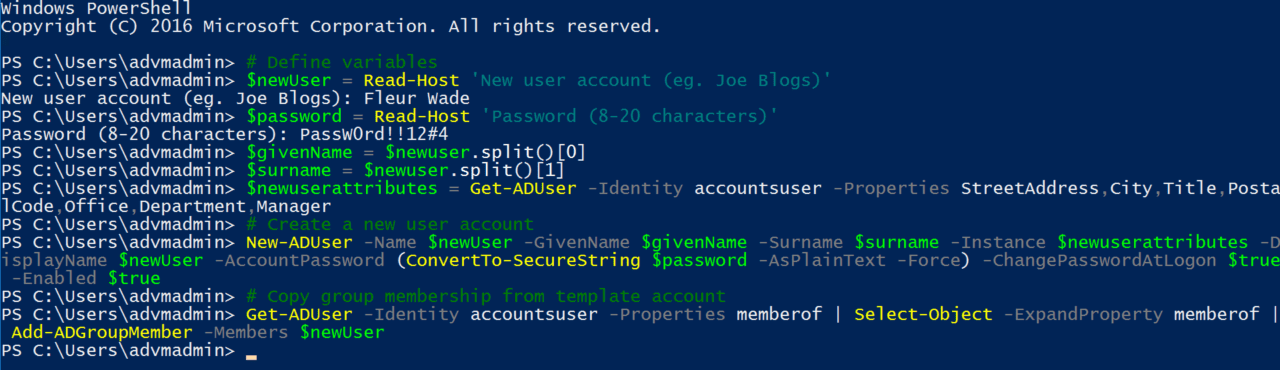
Automate the entire process
Let’s automate the process a bit more so that we only need input the new username and password, and PowerShell will handle the rest. The code below takes input from the console window for the username and password variables. Then it creates values for the givenName and surname parameters of the New-ADUser cmdlet by splitting the value of the $newUser variable.
We then create a variable ($newattributes), which copies the StreetAddress, City, Title, PostalCode, Office, Department, and Manager attributes from accountsuser. The New-ADUser cmdlet then runs to create a new user account based on the variables we defined in the previous section, copying the listed attributes from our template AD account to the new account.
Finally, we use Get-ADUser, Select-Object, and Add-ADGroupMember to add the new account to the same groups that accountsuser is a member of.
# Define variables $newUser = Read-Host 'New user account (eg. Joe Blogs)' $password = Read-Host 'Password (8-20 characters)' $givenName = $newuser.split()[0] $surname = $newuser.split()[1] $newuserattributes = Get-ADUser -Identity accountsuser -Properties StreetAddress,City,Title,PostalCode,Office,Department,Manager # Create a new user account New-ADUser -Name $newUser -GivenName $givenName -Surname $surname -Instance $newuserattributes -DisplayName $newUser -AccountPassword (ConvertTo-SecureString $password -AsPlainText -Force) -ChangePasswordAtLogon $true -Enabled $true # Copy group membership from template account Get-ADUser -Identity accountsuser -Properties memberof | Select-Object -ExpandProperty memberof | Add-ADGroupMember -Members $newUser
And that is it! You can automate the process even further and change the above script to suit your needs. For example, you could modify the code so that the template account must be specified by the administrator in the console window. You could even create a script that sets up new accounts taken from a list or database.