When I started writing about IT in 2005, the security landscape was quite different from that of today’s. Not only were there fewer threats, but also those threats were less sophisticated and infiltrated corporate networks via a limited number of available entry points. Today, with the shift towards cloud computing and employees using a variety of mobile devices outside the relative safety of the corporate intranet, the chance of falling victim to a targeted or opportunistic attack is much greater if the proper protections are not in place.
Microsoft: Questionable Security?
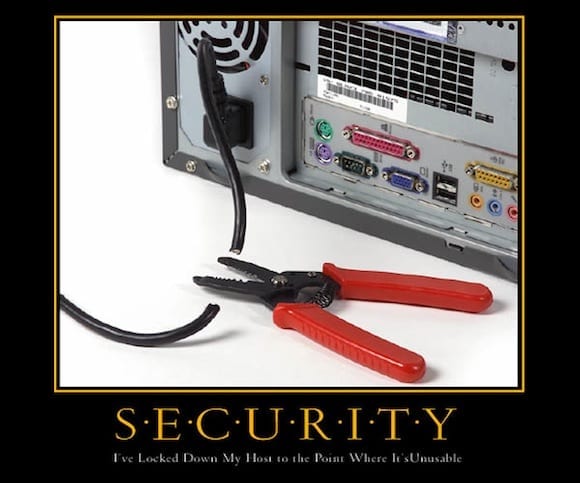
Much of the material I was writing in the past was connected to securing Windows Server on the basis that it was generally considered to be insecure, at least compared to its Linux and Unix counterparts. Over time, the hardening advice Microsoft issued came into question, in that the trade-off in usability often encountered when applying advanced security settings wasn’t worth exchanging for a minor improvement in security. Much of the advice Microsoft now issues is intended for special purpose uses of Windows Server, but hardening advice for high-risk scenarios is still available.
Microsoft has released a number of tools in the past few years that make securing Windows Server easier. The Security Configuration Wizard (SCW) built into Windows Server makes it possible for administrators to configure ACLs, firewall ports, and a number of other security configurations without using Group Policy or modifying the registry. The Baseline Security Analyzer is available for Windows Server and a number of other Microsoft products. There’s also the Security Configuration Manager (SCM), which makes it easy to apply security templates to Windows Server and keep track of any changes you need to make.
Windows Server: Better Solutions
Today, the default configuration of Windows Server is likely to suffice for many organizations. That’s not to say that risk assessments and additional security configuration shouldn’t be considered. Regulatory compliance mandates may require additional server hardening, and Microsoft’s new tools enable organizations to evaluate security on a regular basis, ensuring that unwanted changes haven’t introduced security vulnerabilities and satisfying auditors.
Virtualization also gives organizations the opportunity to improve security. SCM contains templates that organizations can apply to servers running specific roles, such File Server or DHCP, and reduce the attack surface. Before virtualization went mainstream, it was more likely that servers would run two or more roles due to the cost of hardware, making it harder to secure each server – and providing hackers with the opportunity to bring down a range of services rather than just affecting a single role in a virtual machine.
While there will still be some that scoff at the idea of Windows Server being secure, as long as you take some sensible precautions, you should be able to put Windows Server 2012 into production without lots of arcane hardening. Naturally, some usage scenarios will always require more security than others, such as the need for end-to-end encryption of network traffic or two-factor security, but this shouldn’t be turned on out-of-the-box, as it introduces some performance overhead and can be left for IT professionals to configure as needed. Other security innovations, such as AppLocker, BitLocker, and Dynamic Access Control, along with a good security baseline, make Windows Server 2012 a potentially very secure solution.
(Image via ranum.com)