Windows 10 Tip: Block Untrusted Fonts
In today’s Ask the Admin, I’ll show you how to block processing of untrusted fonts using the Graphics Device Interface (GDI) in Windows 10.
Not the sexiest of topics, but Windows 10 contains a new security feature that allows system administrators to prevent users from loading fonts not located in the trusted %windir%/Fonts directory, helping to prevent remote web-based and local escalation of privilege attacks that can occur when parsing fonts.
The feature has three levels of operation: On, Audit, and Exclude apps to load untrusted fonts. When the feature is set to On, only fonts contained in the trusted %windir%/Fonts directory are loaded using GDI and event logging is turned on. Audit turns on event logging but doesn’t block fonts from loading. Exclude apps to load untrusted fonts allows you to set specific apps to load fonts using GDI outside of the %windir%/Fonts directory when the Untrusted Font Blocking feature is enabled.
But before you rush to turn on font blocking, like many security defenses, it comes with some drawbacks. Microsoft notes that you might experience reduced functionality in the following circumstances:
- Sending a print job to a remote printer server if spooler.exe hasn’t been excluded. Fonts not available in the server’s trusted fonts directory won’t be used.
- Print jobs that use fonts, installed by the printer driver’s graphics .dll file, that reside outside of the trusted fonts directory.
- Apps that use memory-based fonts.
- Viewing websites in Internet Explorer that use embedded fonts. IE will use a default font.
- Using Office desktop apps to view documents that include embedded fonts. Office will use a default font.
Block untrusted fonts using Group Policy
The Untrusted Font Blocking feature can be enabled using Group Policy. For more information on using Group Policy, see “How to Create and Link a Group Policy Object in Active Directory” on the Petri IT Knowledgebase.
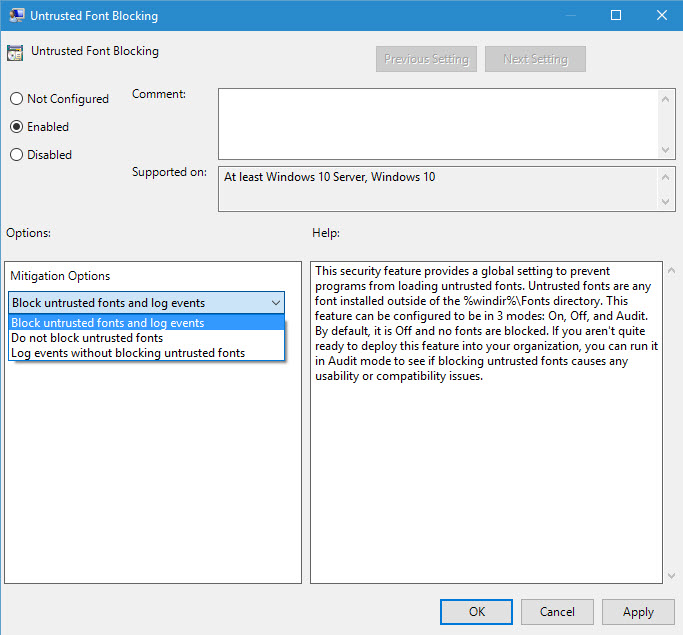
The Untrusted Font Blocking setting can be found in local or Group Policy under Computer Configuration > Administrative Templates > System > Mitigation Options. You’ll note there are three options: Block untrusted fonts and log events, Do not block untrusted fonts, Log events without blocking untrusted fonts.
Excluding processes
Missing from the Group Policy settings above is the ability to exclude processes. Microsoft recommends that in the first instance you try to add any required fonts to the trusted fonts directory. If that’s not possible, then exclude the problem processes or apps by adding the process image name to the registry. For example, if you want to exclude Microsoft Word, add the following value to the registry:
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\Winword.exe
In this article, I explained the Untrusted Font Blocking feature in Windows 10, showed you how to enable it, and how to exclude specific processes from the policy using the registry. If you need to install Fonts on Windows 10, we also have a dedicated guide for that.