It probably won’t come as much of a shock to regular Petri readers but a new report by firmware and hardware security research company Eclypsium says that 40 drivers it tested from different vendors were all found to contain security flaws and all were certified by Microsoft.
Our analysis found that the problem of insecure drivers is widespread, affecting more than 40 drivers from at least 20 different vendors – including every major BIOS vendor, as well as hardware vendors like ASUS, Toshiba, NVIDIA, and Huawei. However, the widespread nature of these vulnerabilities highlights a more fundamental issue – all the vulnerable drivers we discovered have been certified by Microsoft. Since the presence of a vulnerable driver on a device can provide a user (or attacker) with improperly elevated privileges, we have engaged Microsoft to support solutions to better protect against this class of vulnerabilities, such as blacklisting known bad drivers.
According to Eclypsium, recent research shows that flaws in drivers from the likes of ASUS and GigaByte let processes running with standard user rights obtain read and write access to the kernel. These kinds of flaws are already being actively exploited, like Slingshot, which exploits drivers with read and write model-specific register (MSR) capabilities to bypass driver signing requirements. Another example is LoJax, which uses a similar means to hide in firmware and can survive even if the operating system is reinstalled. Although enabling Secure Boot blocks LoJax because it doesn’t have a valid digital signature.
More Than Just Administrator Privileges
Elevation of privilege (EoP) vulnerabilities in Windows and other software is not uncommon. But it’s worth understanding that the flaws found in Windows drivers could allow attackers to elevate to OS kernel mode, which is significantly more access than is granted to root or users with admin rights. OS kernel mode gives hackers access to hardware and firmware directly, potentially making it easier to plant an Advanced Persistent Threat (ATP) like LoJax.
ATPs are more difficult to detect and eradicate than traditional malware because advanced techniques are used to hide in the OS or device firmware. ATPs can usually survive system reboots and they are usually harder to remove than viruses.
The bugs found in drivers could let users with standard rights use a driver as a proxy to gain OS kernel mode access to the system, potentially giving full access to the hardware and firmware. While many ATPs aim to hide and persist for as long as possible, hackers could alternatively use vulnerabilities in drivers to launch denial of service (Dos) attacks or read, write, or redirect data processed by infected hardware.
Can I Trust Drivers with Windows Hardware Quality Labs Certification?
You are welcome to draw your own conclusions, but it would seem not if security is a concern. In terms of compatibility, Microsoft generally does a good job ensuring that certified hardware and drivers work correctly with Windows. And while Microsoft clearly needs to look again at how it certifies drivers for Windows, it must be a shared responsibility between Microsoft and hardware manufacturers to make sure that devices are safe to use.
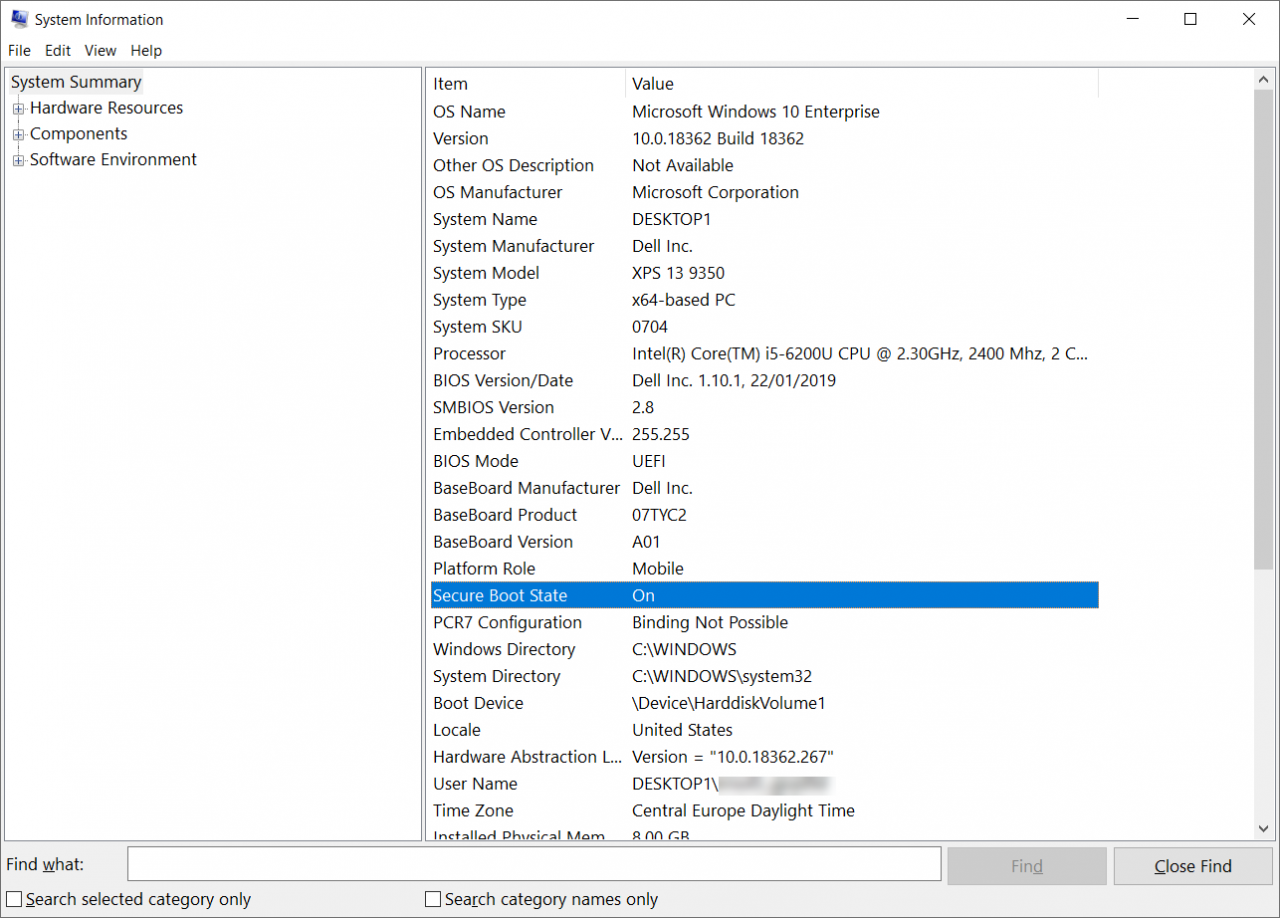
That said, nothing can ever be 100% secure. To help protect your systems, make sure that Secure Boot is enabled if your hardware supports it. Follow best practices, like applying security settings in Microsoft’s security baseline templates; and keep Windows, third-party applications, drivers, and firmware up-to-date. And deploy other defense-in-depth security measures like removing admin privileges from users, application whitelisting, and virtualization-based security (VBS) features like Credential Guard.
You can check whether Secure Boot is enabled on a Windows 10 device by running msinfo32 and checking Secure Boot State under System Summary. Most PCs manufactured in the last few years will support it. If you want more information about applying security templates to Windows, read Microsoft Launches the Security Compliance Toolkit 1.0 on Petri.