Microsoft Adds Pod Sandboxing to Azure Kubernetes Service (AKS)

Last week, Microsoft released a new update that adds pod sandboxing support to its Azure Kubernetes Service (AKS). The new feature allows organizations to run modern applications on AKS in an isolated and secure environment.
Microsoft explained that it’s a standard practice to use Kubernetes for hosting and managing modern applications in cloud environments. However, one of the major drawbacks is that the service doesn’t provide robust support for multi-tenancy capabilities. This makes it impossible to host multiple customers or workloads within a single instance of Kubernetes.
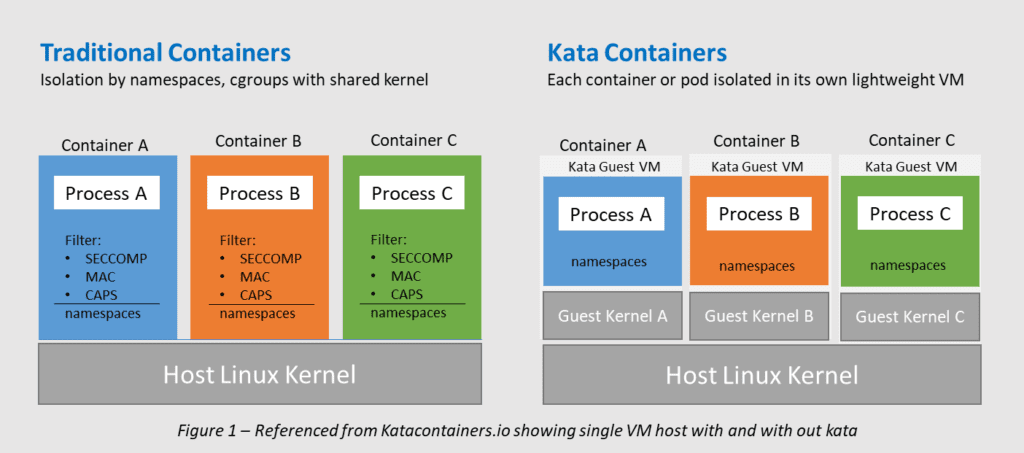
According to Microsoft, modern applications that are bundled together as containers use the same operating system. Each container works like a separate process running on the computer which makes it challenging to keep the containers isolated from each other. This problem could be resolved by running each pod (a collection of containers) on a dedicated VM. However, this approach causes significant performance issues for customers.
To address this problem, Microsoft has developed a lightweight virtual machine (VM) infrastructure called Kata Containers. It’s compatible with Kubernetes and the container runtime interface (CRI) specifications. Microsoft explained that pods that target Kata Containers are treated by Kubernetes like all other containers. However, the process involves adding the containers to a lightweight virtual machine.
“Kata Containers on AKS are built on top of a security-hardened Azure hypervisor using Mariner Linux AKS Container Host (MACH). The isolation per pod is achieved by using a nested lightweight Kata VM that carves out resources from a parent VM node. In this model, each Kata pod gets its own kernel per nested Kata guest VM. This allows users to pack many Kata containers in a single guest VM, while continuing to run containers in the parent VM, providing strong Isolation boundary within a shared AKS Cluster,” Microsoft explained.
Kata Containers provides support for several Linux host and guest images
Currently, Kata Containers only support Linux host and guest images, including Clear Linux, Fedora, and CentOS 7. However, it’s also possible to create custom images for running other operating systems. Microsoft highlighted that the new feature should help to optimize operations for various industries such as health, finance, and ISV/SaaS Partners. You can find detailed instructions on how to use Pod Sandboxing with Azure Kubernetes Service on this support page.
It is important to note Google also provides a gVisor feature that works like a hypervisor to provide secure isolation between containers. It’s designed for enterprise customers that want to guarantee the security of their container workloads. Meanwhile, Amazon came up with its open-source virtualization technology called Firecracker. However, it has yet to get integration with Elastic Kubernetes Service (EKS) to ensure pods isolation.
