Microsoft Confirms Lapsus$ Hacker Group Gained “Limited Access” to Its Source Code

Microsoft has confirmed that the hacking group Lapsus$ managed to gain “limited access” to its security system and steal some parts of their source code. The company says that its security researchers had already been tracking the activities of Lapsus$, which claims to have hacked sensitive data from Samsung, Nvidia, Ubisoft, and Okta.
The Redmond giant detailed in a blog post that the Lapsus$ group compromised an employee account with limited access, but its security teams interrupted the hacking effort mid-way. The company emphasized the leaked source code doesn’t increase the security risks, and the hackers were unable to access customer data or sensitive information.
“This week, the actor made public claims that they had gained access to Microsoft and exfiltrated portions of source code. No customer code or data was involved in the observed activities. Our investigation has found a single account had been compromised, granting limited access. Our cybersecurity response teams quickly engaged to remediate the compromised account and prevent further activity,” the company explained yesterday.
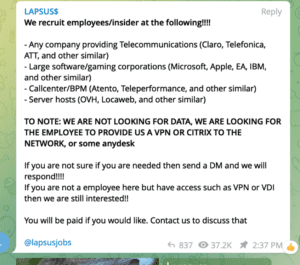
Microsoft highlighted that Lapsus$ has gradually expanded its geographical range to target government and enterprise customers worldwide. Interestingly, the hacking group typically uses different techniques to breach the multi-factor authentication (MFA) systems of the targetted organization. Some popular tactics include SIM-swapping, phone-based social engineering, paying employees to access credentials, purchasing session tokens from public forums, and more.
Microsoft provides recommendations to prevent cyber attacks by the Lapsus$ hacker group
Microsoft has outlined several steps that should help IT Admins protect their organizations. The company recommends that its customers should improve their security practices by implementing secure Multifactor Authentication mechanisms, using trusted endpoints, and leveraging modern VPN authentication techniques. In addition, Microsoft urges companies to follow operational security practices and educate their employees about social engineering attacks.
It is important to note that the hacker group claimed to have access to 37GB of internal source code for Bing and Cortana. However, Microsoft didn’t provide details about the potential source code exfiltration. Microsoft has previously highlighted as a part of the Solarigate investigation that access to source code isn’t an elevation of security risk, and the threat actors still need permissions to modify engineering systems. The firm emphasized that its policy is based on the assumption that the source code is already compromised due to a security breach.
Microsoft says that its cybersecurity response team is still investigating the most recent attacks from Lapsus$, and the company plans to provide additional insights and recommendations soon.






