Microsoft Details FIDO2 Security and Certificate-Based Authentication Updates

Key Takeaways:
- Microsoft has announced a new feature that will let Entra ID users register and sign in using device-bound passkeys managed in Microsoft Authenticator.
- The Microsoft Authenticator app for Android devices is now compliant with FIPS 140 security standards.
- Microsoft has also released some updates for Entra ID Certificate-Based Authentication (CBA).
Microsoft has detailed its efforts to enable phishing-resistant authentication methods for organizations. The company is implementing several security features, including device-bound passkeys, FIDO2 support for iOS and macOS apps, and Certificate-Based Authentication updates, to enhance the overall protection for all Entra ID customers.
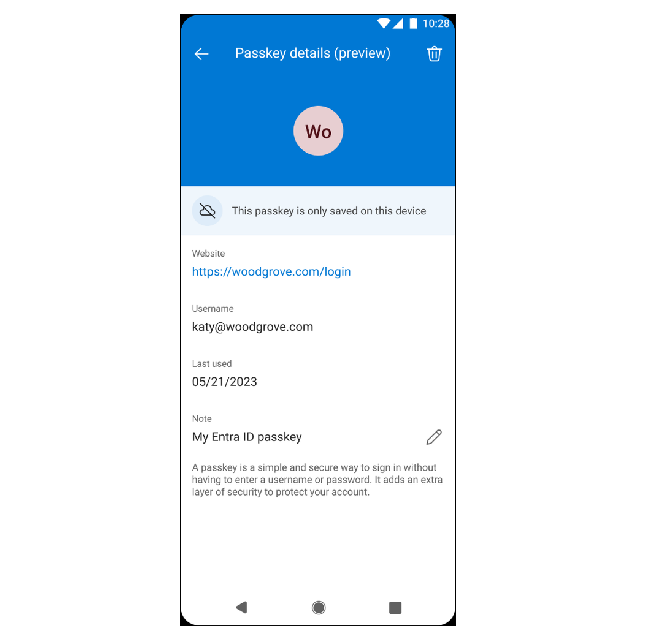
Microsoft has announced that it will soon introduce a new feature for its Entra ID customers. It will allow users to register and sign in to their accounts using device-bound passkeys managed in Microsoft Authenticator. A passkey is a digital credential that eliminates the need for usernames and passwords. Microsoft says that passkey support will be added to the Authenticator app in the first half of 2024.
“This is a cost-effective, phishing-resistant credential available to anyone with the Authenticator app! Passkeys provide you with the latest and greatest security enhancements that will come to the FIDO standard over the next many years – and Authenticator integration lets you take advantage of the security innovations and advanced features Authenticator provides,” Microsoft explained.
Microsoft Authenticator to become phishing-resistant
The latest version of the Microsoft Authenticator app for Android devices is now compliant with the US government’s Federal Information Processing Standards (FIPS) 140 security standard. This compliance applies to all Entra ID authentications that use push multifactor authentications (MFA), phishing-resistant device-bound passkeys, time-based one-time passcodes (TOTP), and passwordless Phone Sign-In (PSI). The Microsoft Authenticator app for iOS is already FIPS 140 compliant.
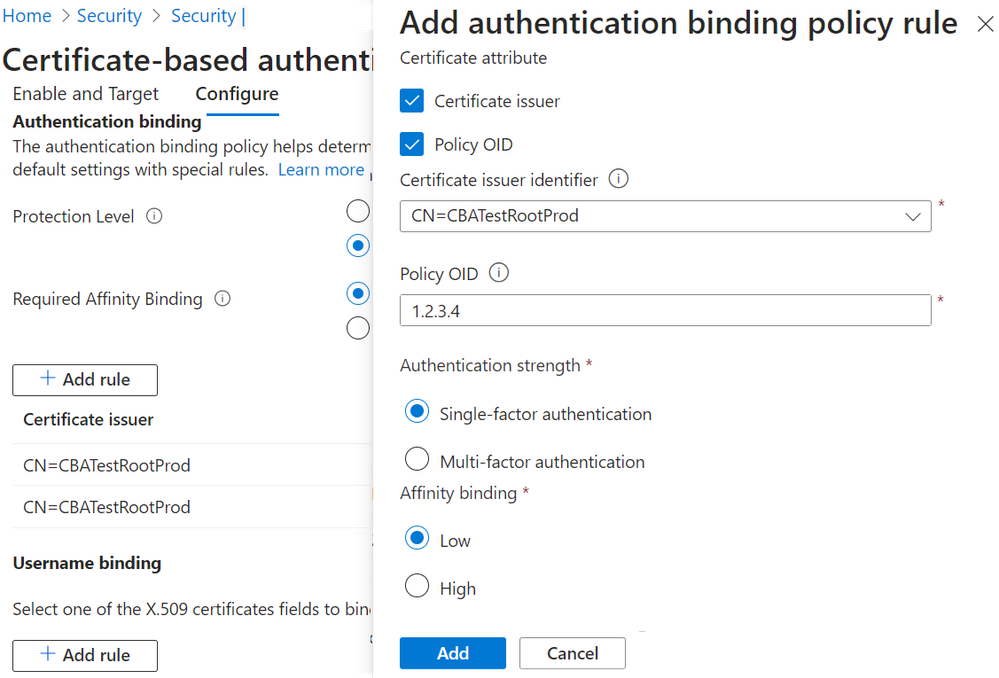
Certificate-based Authentication updates
Last year, Microsoft announced the general availability of Certificate-based Authentication (CBA) for commercial customers. This authentication method is designed to provide an alternative to on-premises identity providers like Active Directory Federation Services (ADFS), which have been the target of attacks due to misconfigurations. Microsoft has reported an increase of over 850 percent in Entra ID CBA usage among government customers.
Microsoft has now made it possible for IT administrators to select certificate strength for different users. Additionally, administrators can configure high affinity (strong) binding for user groups or the entire tenant. Another new feature is the ability to use CBA with other multifactor or step-up authentication methods.
FIDO2 support for iOS and macOS apps
Microsoft announced that FIDO2 authentication support is available in public preview on iOS devices. The feature lets Authenticator users access Microsoft apps on iOS devices with a FIDO2 security key. Microsoft plans to bring the new phishing-resistant authentication option to macOS devices in early 2024.
Lastly, Microsoft introduced FIDO2 authentication support for select MSAL-enabled third-party apps on iOS and macOS. The Microsoft Authentication Library (MSAL) lets developers acquire tokens from the Microsoft identity platform to access secured web APIs. It ensures secure access to Microsoft Graph, third-party web APIs, custom web APIs, and other Microsoft APIs.
Last month, Microsoft announced its Secure Future Initiative to address cybersecurity threats. The initiative is focused on three pillars: AI-based cyber defense, advances in software engineering, and advocacy for more robust application of international norms to protect civilians against cyber threats.