Microsoft Defender Tamper Protection Now Generally Available
Tamper Protection for Microsoft Defender, the antimalware software that is built-in to Windows 10, first appeared in the Windows 10 May 2019 Update (19H1). It is designed to prevent users and malicious software from modifying registry-based settings for Defender that could make a system vulnerable to attack. You may have noticed that Tamper Protection wasn’t enabled by default in Windows 10 19H1. But that is due to change over the coming weeks as Microsoft looks to enable the setting out-of-the-box. According to a report by ZDNet’s Catalin Cimpanu, Microsoft says that starting October 14th, Tamper Protection will be enabled by default for all users in the coming weeks in a multistage rollout.
When Microsoft Defender or Defender ATP Tamper Protection is enabled, malicious software and users won’t be able to change the following features via the registry, Group Policy, or using PowerShell:
- Disable virus and threat protection
- Disable real-time protection
- Turn off behavior monitoring
- Disable Defender’s antivirus components (such as IOfficeAntivirus (IOAV))
- Disable cloud-delivered protection
- Remove security intelligence updates
Tamper Protection is Designed for Enterprises
What’s interesting about Tamper Protection is that when enabled, protected Defender features can’t be changed using Intune, System Center Configuration Manager, and Windows Management Instrumentation. Any requests to change settings will be ignored. And there won’t be any Group Policy setting allowing enterprises to enable Tamper Protection across devices. Again, according to ZDNet’s report, Microsoft says:
“When an administrator enables the policy in Microsoft Intune, the tamper protection policy is digitally signed in the backend before it’s sent to endpoints. The endpoint verifies the validity and intent, establishing that it is a signed package that only security operations personnel with Microsoft Intune admin rights can control.”
So, Tamper Protection can only be turned on/off centrally on devices managed by Microsoft Intune and where Microsoft Defender Advanced Threat Protection (ATP) E5 is deployed. Enterprises using Microsoft Defender ATP will see an alert if the status of Tamper Protection changes on a device. In addition to the requirements already mentioned for Tamper Protection, there are some more requirements if you want to manage Tamper Protection using Intune:
- You must be using Windows security and update security intelligence to version 1.287.60.0 (or above)
- Your machines must be using anti-malware platform version 4.18.1906.3 (or above) and anti-malware engine version 1.1.15500.X (or above). (See Manage Windows Defender Antivirus updates and apply baselines.)
How to Enable Microsoft Defender Tamper Protection Manually
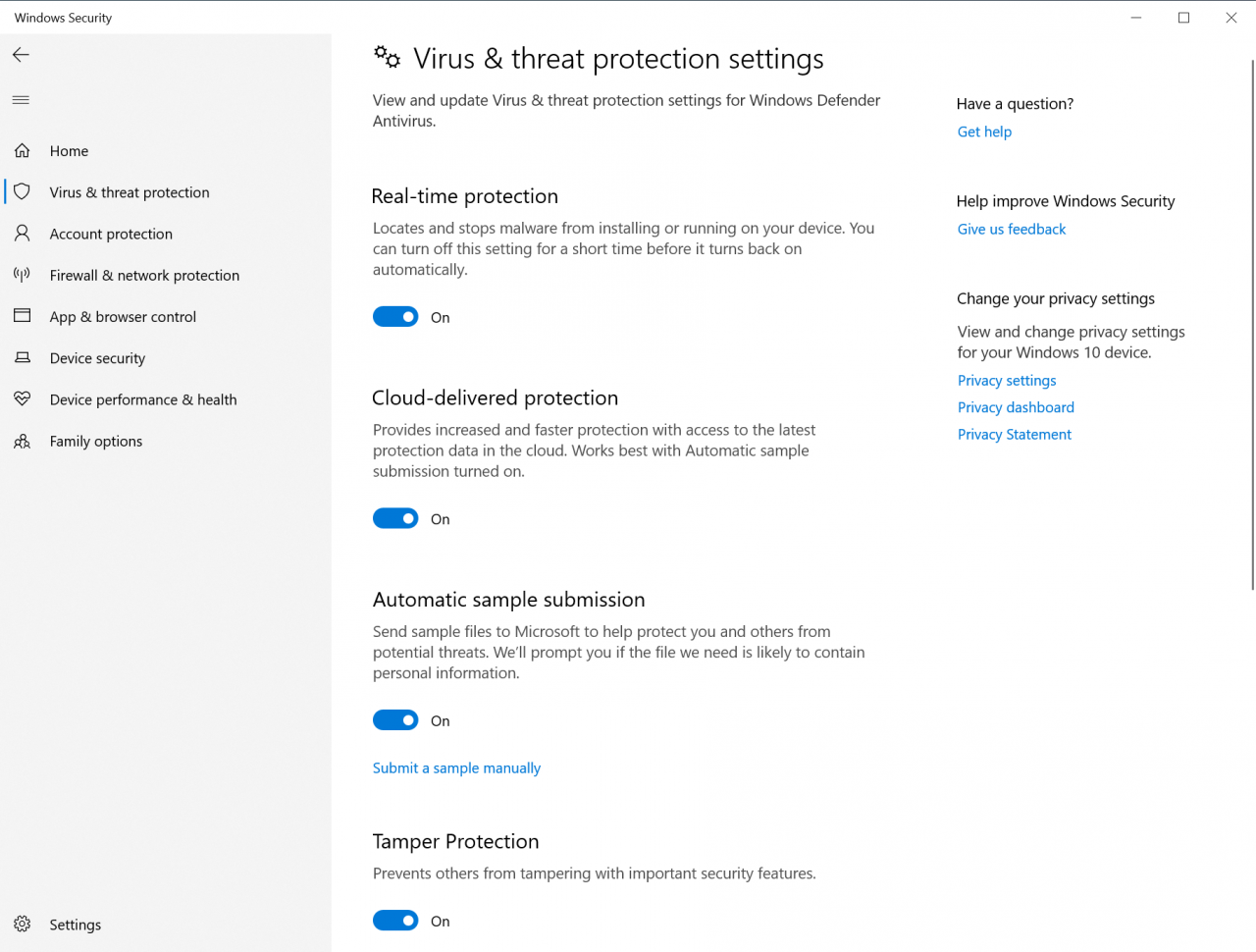
Users wanting to manually enable Tamper Protection can do so using the Windows Security app in Windows 10.
- Type windows security in the search box in the bottom left of the taskbar and select Windows Security from the list of results.
- On the Security at a glance screen, click Virus & threat protection.
- Under Virus & threat protection settings, click Manage settings.
- Scroll down to Tamper Protection and toggle the setting to On.
Tamper Protection Adds to Defender’s Class-Leading Security
As I wrote recently on Petri, Microsoft has been investing heavily in security over the past several years and it appears to be paying off. And because Defender is also used as the basis for Defender ATP, which is an enterprise-class solution, it needs to be more than just ‘good enough’.
Defender won an AV-Test award in the home user category for Windows 10 malware protection for products tested in May and June 2019. Microsoft Defender came joint top with Symantec Norton Security, Kaspersky Internet Security, and F-Secure SAFE; closely followed by McAfee Internet Security Trend Micro Internet Security. Adding Tamper Protection by default only helps to increase the product’s already effective protection.




