Microsoft Defender for Endpoint Now Secures Unmanaged Devices and Linux Gets EDR
- Blog
- Hybrid Cloud
- Post
Microsoft recently announced that its Defender for Endpoint solution can now detect when unmanaged network devices may pose a threat. Microsoft Defender for Endpoint is an enterprise antimalware solution that builds upon the free Microsoft Defender software that’s built into Windows 10 and Windows Server.
Defender for Endpoint helps enterprises prevent, detect, investigate, and respond to advanced-level threats. It includes endpoint behavioral sensors, cloud security analytics, and threat intelligence to provide the extra protection that enterprises need to secure devices. And it comes with centralized configuration, administration, and APIs.
Securing devices for hybrid work
Microsoft says that in a new world of hybrid work, organizations need to protect themselves from ‘bring your own’ (BYO) devices. According to Bret Arsenault, Microsoft’s Chief Information Security Officer, users are 71% more likely to be infected on unmanaged devices. Microsoft believes that this is because organizations can’t set the right security configurations. For example, unmanaged devices might not be updated with the latest software and OS patches, and shadow apps present additional risk.
New capabilities in Microsoft Defender for Endpoint let organizations get more insight and control over unmanaged devices, without needing additional hardware or to install software agents. Using integrated workflows, businesses can onboard and secure devices that might pose a threat.
Detecting vulnerabilities in unmanaged devices
Using technology borrowed from Azure IoT security and from its acquisition of CyberX in 2020, Defender for Endpoint is now able to detect vulnerable Internet of Things (IoT) devices on the local network. And using existing network tooling, block those devices. Where tooling isn’t available to block vulnerable network devices, Defender for Endpoint gives SecOps visibility so that further action can be taken to block or update devices as required.
Windows devices onboarded to Defender for Endpoint can perform read-only SNMP scans of unmanaged devices connected to the local network. Currently, endpoints can perform vulnerability assessments on the following operating systems, with Microsoft planning to add more over time:
- Cisco IOS, IOS-XE, NX-OS
- Juniper JUNOS
- HPE ArubaOS, Procurve Switch Software
- Palo Alto Networks PAN-OS
Defender for Endpoint also discovers endpoints that can be managed, like workstations, servers, and mobile devices. These can then be onboarded to Defender for Endpoint to provide comprehensive protection.
Microsoft Defender for Endpoint on Linux
Microsoft also announced that Defender for Endpoint on Linux is getting extra features. Now generally available, customers can access endpoint detection and response (EDR). Defender for Endpoint supports the following Linux distributions:
- RHEL 7.2+
- CentOS Linux 7.2+
- Ubuntu 16 LTS, or higher LTS
- SLES 12+
- Debian 9+
- Oracle Linux 7.2
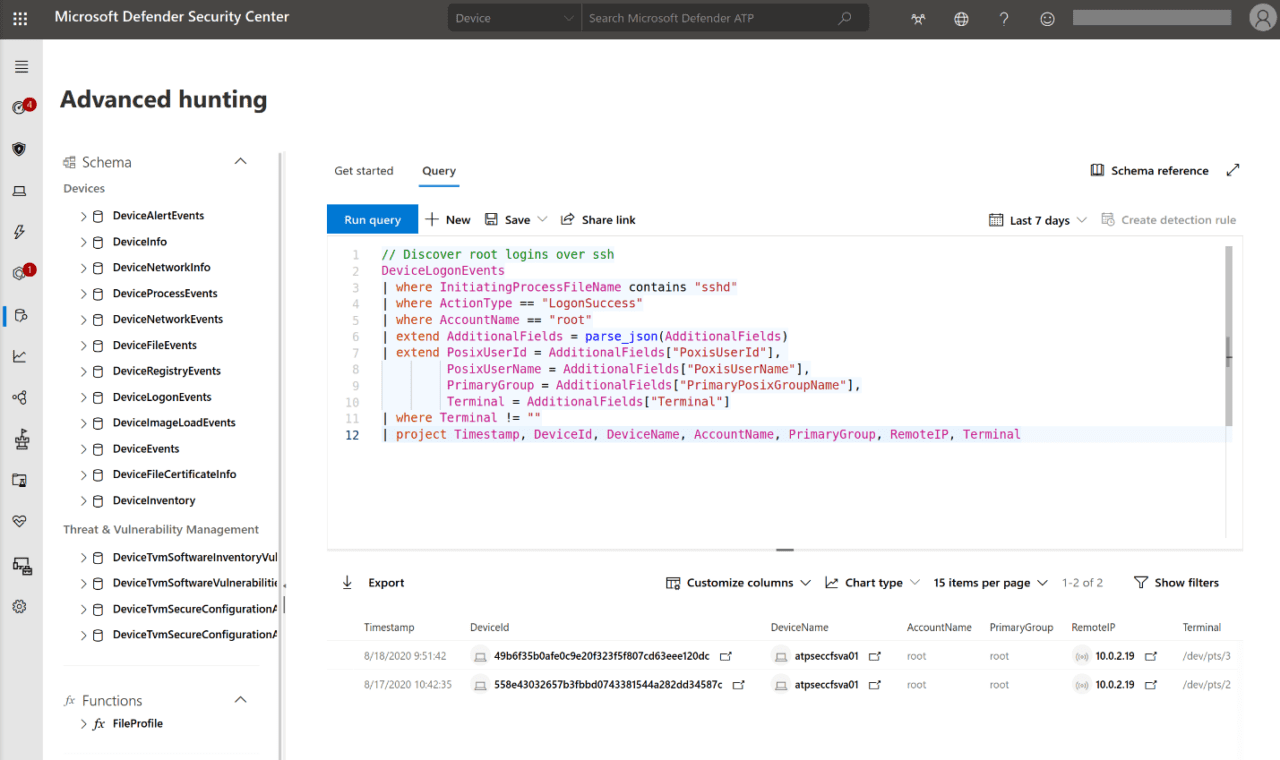
EDR helps organizations detect advanced attacks that utilize Linux servers. It provides SecOps with a machine timeline, process and file creation, network connections, login events, and advanced hunting capabilities. And like on Windows, EDR for Linux provides insights to where threats came from and how malicious processes or activity was created.