Loopback Adapter Installation on Windows Server 2012
- Blog
- Networking
- Post
How do I install the loopback adapter in Windows Server 2012?
While there is a tendency for vendors to assume that we are always connected to a network or the Internet, there are occasions when network connectivity is not available but we’d still like to use an application that requires an IP address. One example is Hyper-V, which when used without a network connection has limited functionality if there is no IP address available on the host.
Install Loopback Adapter
Microsoft’s loopback adapter can be installed to provide a virtual network connection and IP address. Here’s how you do it.
- Logon to Windows Server 2012 as a local administrator.
- Right-click the far bottom left of the Taskbar, over the Start charm when it appears, and select Device Manager from the menu.
- In the Device Manager window, right-click the server name and select Add legacy hardware from the menu.
- Click Next on the welcome screen of the Add Hardware Wizard.
- Select Install the hardware that I manually select from a list (Advanced) and click Next.
- Under Common hardware types, scroll down the menu, select Network adapters and click Next.
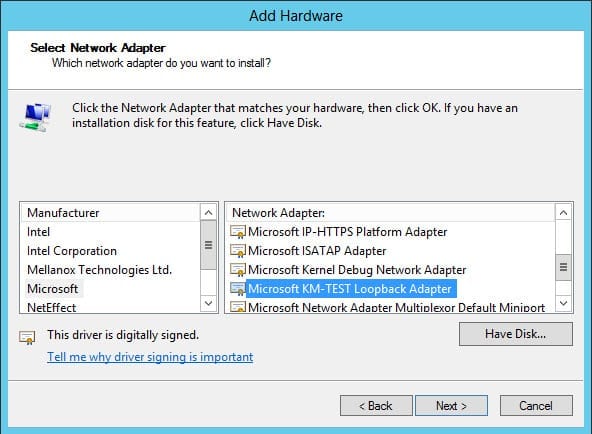
- On the Select Network Adapter screen, select Microsoft from the list of manufacturers.
- Select Microsoft KM-TEST Loopback Adapter from the list of network adapters on the right and click Next.
- Click Next again to confirm that you want to install the loopback adapter.
- Click Finish once the installation has completed.
Configure Loopback Adapter
Now that the loopback adapter is installed on the server, you can configure it via the Network and Sharing Center.
- Right-click the network icon in the bottom right corner of the desktop Taskbar and select Open Network and Sharing Center from the menu.
- In the Network and Sharing Center window, click Change adapter settings.
- In the Network Connections window, right-click the Microsoft KM-Test Loopback Adapter and select Properties from the menu.
- On the Networking tab, select Internet Protocol Version 4 (TCP/IPv4) and click Properties.
- In the Properties dialog on the General tab, configure IP address network and DNS settings as required and click OK.
- Close the adapter’s Properties dialog.