Is it safe to store sensitive information in the cloud?
The seamlessly endless possibilities of cloud computing have changed the way we use the Internet. But with new possibilities come new problems, and security concerns have rightly been highlighted as a potential deal breaker when it comes to deploying cloud services. But just like virtual desktop infrastructure (VDI) before it, there’s also — as Gartner would put it — mass media hype involved, not so much in the technology behind the cloud, but in the term itself from a marketing perspective.
Much of the backend technology we used, and still use, before the cloud revolution isn’t that different from today’s. And on that note, it’s worth looking at an example of pre-cloud tech (email) and cloud storage — think Dropbox and OneDrive.
Let’s take OneDrive as an example, the consumer cloud storage service built-in to Windows 10. I’ve noticed that some avoid using OneDrive to store personal documents, such as scanned copies of passports, bank statements and other official documents, and that’s perfectly valid. But at the same time, those same people are happy to send their scanned passport via email.
It appears that there’s a fundamental misunderstanding of how email works if it’s considered safer than cloud storage. Maybe emailed documents are magically beamed to the recipient without ever being stored on a server somewhere? Or a simple username and password can’t be used to hack email? If you’re happy to email a copy of your passport, then storing the file in cloud storage isn’t technically much different.
OneDrive versus Office 365 email
OK, that might not be entirely true. It largely depends on the email and cloud storage services you compare. As it stands, consumer OneDrive doesn’t encrypt files at rest in Microsoft’s datacenters, but files are encrypted in transit. That differs from Office 365 email, where data is encrypted at rest in the datacenter using BitLocker, and in transit using SSL. Microsoft Accounts also offer two-factor authentication, an important security defense if you’re serious about protecting your account and the data it provides access to.
OneDrive for Business encrypts data at rest and uses a unique encryption key for each file, providing damage limitation if a key is compromised. Each update to a file is also encrypted with an additional unique key. The content encryption keys are encrypted with a master key, and the datacenter disk encrypted using BitLocker, providing a granular level of encryption that makes unauthorized access difficult.
Do you trust your CSP?
But it’s worth noting that none of the above services allow encryption key management. Microsoft manages the keys and can theoretically decrypt your data. The encryption provided by BitLocker protects your data should a disk be physically accessed by a malicious actor, and the granular encryption provided in OneDrive for Business makes it hard for users of the same tenant to get access to data for which they don’t have authorization.
Third-party key management solutions, such as Ciphercloud, can provide more granular control and key management for OneDrive, Office 365, and other cloud services. Microsoft has promised that sometime in 2016, Office 365 users will be able to ‘generate and control their own keys for encrypting content in Office 365.’
Microsoft Azure encryption
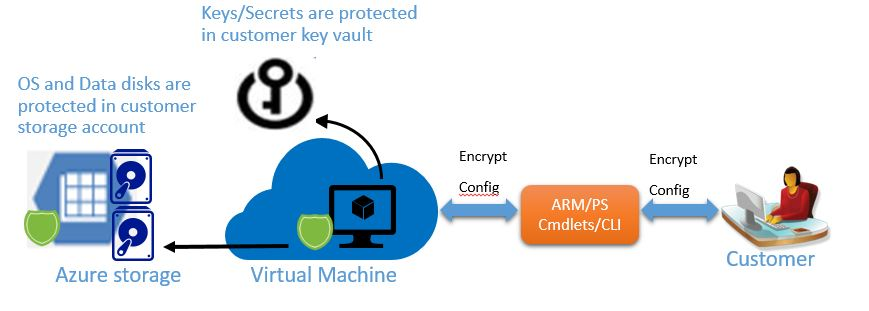
The ability to encrypt Azure virtual machine system disks using BitLocker has been a long requested feature, and Microsoft has provided an answer with Azure Disk Encryption, a new service that’s currently in preview and uses Azure Key Vault for key storage and management. In the meantime, CloudLink SecureVM is available in the Azure Marketplace and provides full volume encryption by emulating a Trusted Platform Module (TPM).
StorSimple also provides a hybrid-cloud storage appliance that sits in your datacenter and connects to the Azure Storage service, and allows customers to encrypt data in the cloud with their own encryption key.
Applications that use Azure Storage can take advantage of client-side encryption, allowing customers to manage their own encryption keys for data stored in tables, blobs, and queues. This solution lets developers encrypt data before it gets sent to the cloud, and decrypt it as it gets downloaded back to the client app.
Is the cloud secure?
Getting security right is a tricky balancing act, and whether the cloud is secure depends on the service, the cloud service provider, and from what or who you’re looking to protect data. But the cloud isn’t inherently insecure, and many of the security challenges we’ve traditionally faced also apply to the cloud. But if security is a key concern, it’s likely you’ll find a solution to suit your needs, so don’t dismiss the cloud out of hand.




