How to Update Windows System Images Using the Antimalware Update Package for Microsoft Defender
If your organization provisions and services Windows using system imaging, Microsoft has released a new tool that can help make sure devices are secure when they are deployed to users. System imaging involves capturing an installation of Windows that contains the configuration settings and software required for your organization’s devices. The resulting capture, or ‘snapshot’ if you like, is known as a system image. The image is then used to automate the installation of Windows at scale.
Creating a standard system image involves a lot of work and testing. Without significant effort upfront, the operating system and applications might not work as expected when it is deployed to users. Because of the work that goes into creating a system image, organizations tend not to recreate them regularly. A new image might only be called for if a new version of Windows is released or if software needs to be added or removed.
For more information using the Microsoft Deployment Toolkit (MDT) and Windows Deployment Services (WDS) to deploy Windows images, check out my 3-part series on Petri:
Deploy Windows 10 Using MDT and WDS, Part 1: Create an MDT Deployment Share
Deploy Windows 10 Using MDT and WDS, Part 2: Create an MDT Task Sequence and Configure WDS
Deploy Windows 10 Using MDT and WDS, Part 3: Deploy Windows 10 from a PXE-Enabled Boot Client
Devices inadequately protected until Microsoft Defender updates
Devices provisioned using a system image are at risk for the first few hours of use as they come provisioned with out-of-date antivirus. To solve the issue, Microsoft recently released a tool that lets IT service existing offline images to update them with the latest Defender definition files, platform, and engine version. Microsoft says:
The first hours of a newly installed Windows deployment can leave the system vulnerable because of a Microsoft Defender protection gap. This is because the OS installation images may contain outdated antimalware software binaries.
The devices on which these deployments are made are inadequately protected until they receive the first antimalware software update. We recommend that you regularly service OS installation images in order to update Microsoft Defender binaries and minimize this protection gap in new deployments.
The new antimalware update package for Microsoft Defender
The new update package for Microsoft Defender works with the following operating systems:
- Windows 10 Enterprise, Pro, and Home
- Windows Server 2019
- Windows Server 2016
The update package will be refreshed monthly to include updates and fixes for Microsoft Defender, along with the latest security intelligence update (antivirus definition file) that is available at the time the update package is released. You can download the 32-bit and 64-bit versions of the update package from Microsoft’s website.
Updating a Windows image using the update package for Microsoft Defender
Before you can service a system image, there are several prerequisites that must be met.
- The device on which you run the update tool must be running 64-bit Windows 10 with PowerShell 5.1 or later version installed.
- The Powershell.Security and DISM PowerShell modules must be installed on the device.
- PowerShell must be running with administrator privileges on the device where the tool is run.
Additionally, Microsoft says that the tool must only be run against offline images. Updating live images can damage the Windows installation. And while there is an option to remove updates you apply, Microsoft recommends making a backup of any images you update using the tool.
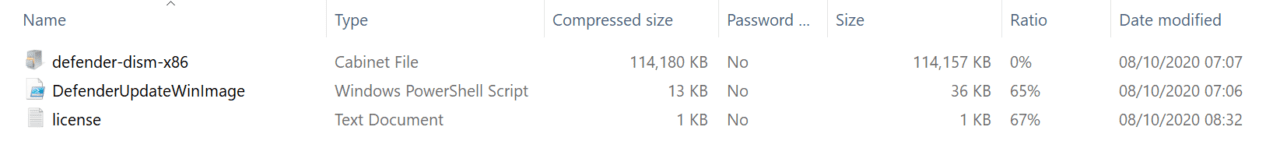
Once you’ve unzipped the package for the architecture you want to update, you can run the script in an elevated PowerShell window:
DefenderUpdateWinImage.ps1 – WorkingDirectory <path> -Action AddUpdate - ImagePath <path_to_Os_Image> -Package <path_to_package>
There are three supported actions. In the above example, the update tool is used to install a Defender update on a system image (-ImagePath). If you want to remove a Defender update from an image, you change -Action to RemoveUpdate and omit the -Package option:
DefenderUpdateWinImage.ps1 - WorkingDirectory<path> -Action RemoveUpdate - ImagePath <path_to_Os_Image>
Finally, you can show the details of an installed update using the ShowUpdate action:
DefenderUpdateWinImage.ps1 - WorkingDirectory<path> -Action ShowUpdate - ImagePath <path_to_Os_Image>