How to Protect Against Active Directory DCShadow Attacks
DCShadow is a feature in the lsadump module of Mimikatz. Mimikatz is an open-source post-exploitation tool used in Windows credential-based attacks. DCShadow was added to Mimikatz in 2018 and it lets attackers achieve persistent privileged access in Windows Server Active Directory (AD), while letting the attacker cover their tracks.
Attacks against AD are common because it controls the security for most systems in your IT infrastructure. If a hacker can get privileged access to AD, then they also have privileged access to all servers and devices joined to the AD domain.
How does DCShadow work?
A DCShadow attack registers any Windows device joined to the AD domain as a domain controller (DC) by creating two new objects in the domain’s Configuration partition. It also changes the service principal name (SPN) of the computer used in the attack.
The attack can be performed from Windows 10. And while Windows 10 cannot be a domain controller, DCShadow tricks AD into thinking Windows 10, or another Windows client SKU, is actually a DC.
Once the device used in the attack is trusted by AD to replicate changes to the directory, the attacker pushes changes that allows them to stay in control of the domain.
After the attacker’s changes have successfully replicated, the new DC objects in the Configuration partition are deleted, helping the attacker to create persistent access to the domain while evading detection. To summarize:
- The attacker registers a rogue DC by creating objects in AD’s Configuration partition
- The attacker replicates changes to AD so that they can maintain persistence
- The attacker deletes the ‘rogue’ DC, which might only exist for a few seconds
Privileged access to Active Directory
Before an attacker can make changes to AD’s Configuration partition, they need privileged access to the domain. You might ask why go through all the effort to register a rogue DC if an attacker already has privileged access to the domain? Because DCShadow is primarily about the attacker trying to remain undiscovered for as long as possible.
Prevention is better than cure
The best way to stop DCShadow, and other attacks against AD, is to prevent hackers from getting privileged access. Domain administrator credentials are usually harvested when hackers exploit vulnerabilities in Windows. For example, IT staff might use domain admin credentials to log in to Windows PCs to support users. At a later stage, a device may be compromised, along with the domain admin credentials.
Privileged access workstations
It’s best practice to only use domain admin credentials and other accounts that have privileged access to AD, on workstations that are specially secured and purposed for managing AD. These workstations are known as privileged access workstations (PAW). PAWs shouldn’t be connected to the public Internet.
Delegating privileges for common admin tasks
Everyday admin tasks, like managing AD users, groups, and Group Policy Objects, can be delegated to users without giving them privileged access to the domain. The Delegation of Control Wizard in Active Directory Users and Computers (ADUC) can be used to delegate privileges for performing common admin tasks.
See Managing Privileged Access to Active Directory on Petri for more information.
Protecting domain accounts with Windows 10 Credential Guard
Windows Defender Credential Guard provides extra protection for domain accounts by isolating credentials in a secure zone that the Windows kernel cannot access, even if it is compromised. Credential Guard requires devices support virtualization-based security (VBS).
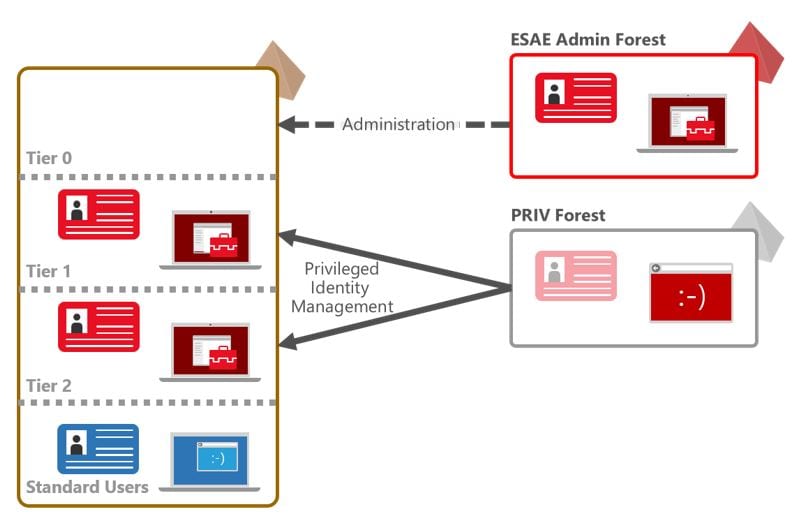
Active Directory tiered administration model
Microsoft’s tiered administration model for managing AD helps organizations better secure their environments. The model defines three tiers that create buffer zones to separate administration of high-risk PCs from valuable assets like domain controllers.
It’s not impossible to move from one tier to another but the model does increase the cost for attackers.
For more information on implementing a tiered administration model, see Why You Should Use Microsoft’s Active Directory Tier Administrative Model and Set Up Active Directory to Support Tiered Administration and Privileged Access Workstations on Petri.
Privileged identity management
A privileged identity management (PIM) solution can help organizations monitor and control privileged access to AD. Windows Server 2016 Shadow Principals and short-lived AD groups help businesses take control of Active Directory when used with a specially hardened AD forest for administration.
PIM provides better security for privileged AD accounts and it also allows the provisioning of standard user accounts in the administrative forest that are granted Just-in-Time (JIT) administrative access to production forests.
For more information on PIM, read Windows Server 2016: Understanding Microsoft’s Enhanced Security Administrative Environment on Petri.
DCShadow attack detection
If you fail to prevent an attack for whatever reason, there are third-party tools available that can monitor the AD replication stream and alert you to attacks like DCShadow.
Windows Event Log
DCShadow can be detected in Windows logs by checking for new objects in the Configuration partition. But once a hacker has privileged access to AD, they can also delete the event logs.
Directory service replication Event ID 4928, ‘An Active Directory replica source naming context was established’, and Event ID 4929 ‘An Active Directory replica source naming context was removed’, can indicate a DCShadow attack.
Monitoring the network
Monitoring network connections for DrsAddEntry and DrsReplicaAdd calls to DCs from non-DCs, might show a DCShadow attack. DrsAddEntry and DrsReplicaAdd calls should only ever come from DCs.
For more information on DCShadow, you can check out the official website here.