February 2025 Patch Tuesday Updates Fix 2 Zero-Day Vulnerabilities
Microsoft’s February 2025 Patch Tuesday includes 57 security fixes and critical vulnerability patches.
Key Takeaways:
- Microsoft released 57 security patches, including three critical vulnerabilities and two actively exploited flaws.
- Microsoft has fixed critical vulnerabilities, such as privilege escalation in WinSock and remote code execution in Excel and LDAP.
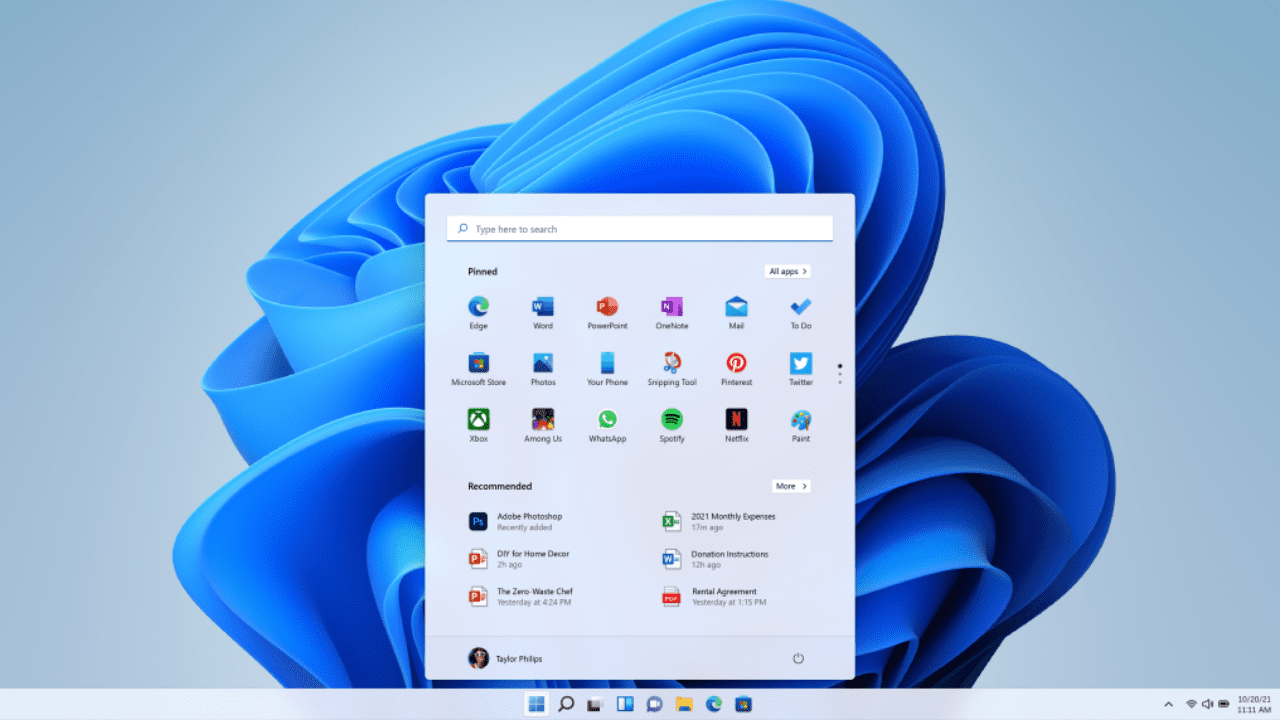
- Windows 11 users get improved taskbar app previews, File Explorer improvements, and a OneDrive continuity feature.
Microsoft has released the February 2025 Patch Tuesday updates for Windows 11 and Windows 10. This month, there are 57 new patches to address vulnerabilities in Windows, Office, Azure, Visual Studio, and Remote Desktop Services.
On the quality and experience front, Microsoft has released a couple of new features and improvements for Windows 11 versions 24H2 and 23H2. Meanwhile, the KB5051974 update automatically installs the new Outlook for Windows app on PCs running Windows 10 version 22H2.
57 vulnerabilities fixed in the February 2025 Patch Tuesday updates
Among the 57 vulnerabilities fixed this month, three are rated critical, 53 are rated Important, and one of them is rated Moderate in severity. Notably, two of these security flaws are publicly known and two of them are already being exploited in the wild. Here are the most important critical vulnerabilities Microsoft fixed this month:
CVE-2025-21418: This is an actively exploited privilege escalation vulnerability in the Windows Ancillary Function Driver for WinSock. This security flaw allows a hacker to execute a specifically crafted program to gain system-level privileges on Windows 11, Windows 10, and Windows Server machines.
CVE-2025-21391: This is a privilege escalation vulnerability in Windows Storage with a CVSS score of 7.1. It could allow a local attacker to delete files from the target system, potentially disrupting applications that rely on this data.
CVE-2025-21194: This is a 7.1-rated security feature bypass vulnerability in Microsoft Surface. The flaw could enable cybercriminals to compromise the hypervisor and the secure kernel on Surface devices.
CVE-2025-21377: This is a zero-day spoofing vulnerability in the NTLM hash disclosure. This flaw could enable hackers to gain unauthorized access to a user’s NTLMv2 hash. Microsoft says that this vulnerability requires selecting the file, right-clicking to inspect it, or performing other actions to trigger it.
CVE-2025-21381: This is a remote code execution vulnerability in Microsoft Excel with a CVSS score of 7.8. It could allow threat actors to view a malicious Excel document in a preview pane to trigger the exploit on a local machine.
CVE-2025-21376: This is a remote code execution vulnerability in Windows Lightweight Directory Access Protocol (LDAP) that affects most supported Windows desktop and server machines. This security flaw could be triggered by an attacker without system privileges and user interaction.
CVE-2025-21379: This is a remote code execution vulnerability in the DHCP Client Service. It requires an attacker to thoroughly map the network and execute a machine-in-the-middle (MITM) attack.
CVE-2025-21177: This is a privilege escalation flaw in Dynamics 365 Sales with an 8.7 CVSS score. Microsoft has already mitigated this vulnerability and doesn’t require any action from end users.
Here’s a full list of all the vulnerabilities Microsoft addressed this month:
| Product | Impact | Max Severity | Article | Download | Details |
| Windows 11 Version 22H2 for ARM64-based Systems | Elevation of Privilege | Important | 5051989 | Security Update | CVE-2025-21373 |
| Windows 10 Version 21H2 for x64-based Systems | Elevation of Privilege | Important | 5051974 | Security Update | CVE-2025-21373 |
| Windows 10 Version 21H2 for ARM64-based Systems | Elevation of Privilege | Important | 5051974 | Security Update | CVE-2025-21373 |
| Windows 10 Version 21H2 for 32-bit Systems | Elevation of Privilege | Important | 5051974 | Security Update | CVE-2025-21373 |
| Windows Server 2022 (Server Core installation) | Elevation of Privilege | Important | 5051979 | Security Update | CVE-2025-21373 |
| Windows Server 2022 (Server Core installation) | Elevation of Privilege | Important | 5052106 | SecurityHotpatchUpdate | CVE-2025-21373 |
| Windows Server 2022 | Elevation of Privilege | Important | 5051979 | Security Update | CVE-2025-21373 |
| Windows Server 2022 | Elevation of Privilege | Important | 5052106 | SecurityHotpatchUpdate | CVE-2025-21373 |
| Windows Server 2019 (Server Core installation) | Elevation of Privilege | Important | 5052000 | Security Update | CVE-2025-21373 |
| Windows 10 Version 22H2 for ARM64-based Systems | Denial of Service | Important | 5051974 | Security Update | CVE-2025-21212 |
| Windows 10 Version 22H2 for x64-based Systems | Denial of Service | Important | 5051974 | Security Update | CVE-2025-21212 |
| Windows 11 Version 22H2 for x64-based Systems | Denial of Service | Important | 5051989 | Security Update | CVE-2025-21212 |
| Microsoft Office 2019 for 64-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21394 |
| Microsoft Office 2019 for 32-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21394 |
| Office Online Server | Remote Code Execution | Important | 5002679 | Security Update | CVE-2025-21394 |
| Microsoft Office 2016 (64-bit edition) | Remote Code Execution | Important | 5002686 | Security Update | CVE-2025-21392 |
| Windows Server 2019 | Spoofing | Important | 5052000 | Security Update | CVE-2025-21377 |
| Windows 10 Version 1809 for x64-based Systems | Spoofing | Important | 5052000 | Security Update | CVE-2025-21377 |
| Windows 10 Version 1809 for 32-bit Systems | Spoofing | Important | 5052000 | Security Update | CVE-2025-21377 |
| Windows Server 2012 R2 (Server Core installation) | Remote Code Execution | Important | 5052042 | Monthly Rollup | CVE-2025-21371 |
| Windows Server 2012 R2 | Remote Code Execution | Important | 5052042 | Monthly Rollup | CVE-2025-21371 |
| Windows Server 2012 (Server Core installation) | Remote Code Execution | Important | 5052020 | Monthly Rollup | CVE-2025-21371 |
| Windows Server 2012 | Remote Code Execution | Important | 5052020 | Monthly Rollup | CVE-2025-21371 |
| Windows Server 2016 | Elevation of Privilege | Important | 5052006 | Security Update | CVE-2025-21358 |
| Windows 10 Version 1607 for x64-based Systems | Elevation of Privilege | Important | 5052006 | Security Update | CVE-2025-21358 |
| Windows 10 Version 1607 for 32-bit Systems | Elevation of Privilege | Important | 5052006 | Security Update | CVE-2025-21358 |
| Windows 10 for x64-based Systems | Elevation of Privilege | Important | 5052040 | Security Update | CVE-2025-21358 |
| Windows 10 for 32-bit Systems | Elevation of Privilege | Important | 5052040 | Security Update | CVE-2025-21358 |
| Windows Server 2025 | Elevation of Privilege | Important | 5051987 | Security Update | CVE-2025-21358 |
| Windows Server 2025 | Elevation of Privilege | Important | 5052105 | SecurityHotpatchUpdate | CVE-2025-21358 |
| Windows 11 Version 24H2 for x64-based Systems | Elevation of Privilege | Important | 5051987 | Security Update | CVE-2025-21358 |
| Windows 11 Version 24H2 for x64-based Systems | Elevation of Privilege | Important | 5052105 | SecurityHotpatchUpdate | CVE-2025-21358 |
| Windows 11 Version 24H2 for ARM64-based Systems | Denial of Service | Important | 5051987 | Security Update | CVE-2025-21347 |
| Windows 11 Version 24H2 for ARM64-based Systems | Denial of Service | Important | 5052105 | SecurityHotpatchUpdate | CVE-2025-21347 |
| Windows Server 2022, 23H2 Edition (Server Core installation) | Denial of Service | Important | 5051980 | Security Update | CVE-2025-21347 |
| Windows 11 Version 23H2 for x64-based Systems | Denial of Service | Important | 5051989 | Security Update | CVE-2025-21347 |
| Windows 11 Version 23H2 for ARM64-based Systems | Denial of Service | Important | 5051989 | Security Update | CVE-2025-21347 |
| Windows Server 2025 (Server Core installation) | Denial of Service | Important | 5051987 | Security Update | CVE-2025-21347 |
| Windows Server 2025 (Server Core installation) | Denial of Service | Important | 5052105 | SecurityHotpatchUpdate | CVE-2025-21347 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Remote Code Execution | Important | 5052016 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Remote Code Execution | Important | 5052032 | Security Only | CVE-2025-21200 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Remote Code Execution | Important | 5052016 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Remote Code Execution | Important | 5052032 | Security Only | CVE-2025-21200 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | 5052038 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | 5052072 | Security Only | CVE-2025-21200 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Remote Code Execution | Important | 5052038 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Remote Code Execution | Important | 5052072 | Security Only | CVE-2025-21200 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | 5052038 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Remote Code Execution | Important | 5052072 | Security Only | CVE-2025-21200 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Remote Code Execution | Important | 5052038 | Monthly Rollup | CVE-2025-21200 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Remote Code Execution | Important | 5052072 | Security Only | CVE-2025-21200 |
| Windows Server 2016 (Server Core installation) | Remote Code Execution | Important | 5052006 | Security Update | CVE-2025-21200 |
| Windows 10 Version 22H2 for 32-bit Systems | Remote Code Execution | Critical | 5051974 | Security Update | CVE-2025-21376 |
| Visual Studio Code – JS Debug Extension | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-24042 |
| Microsoft PC Manager | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21322 |
| Microsoft SharePoint Server Subscription Edition | Remote Code Execution | Important | 5002681 | Security Update | CVE-2025-21400 |
| Microsoft SharePoint Server 2019 | Remote Code Execution | Important | 5002678 | Security Update | CVE-2025-21400 |
| Microsoft SharePoint Enterprise Server 2016 | Remote Code Execution | Important | 5002685 | Security Update | CVE-2025-21400 |
| Microsoft Office LTSC 2024 for 64-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft Office LTSC 2024 for 32-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft Office LTSC 2021 for 32-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft Office LTSC 2021 for 64-bit editions | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft 365 Apps for Enterprise for 64-bit Systems | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft 365 Apps for Enterprise for 32-bit Systems | Remote Code Execution | Important | Click to Run | Security Update | CVE-2025-21397 |
| Microsoft Excel 2016 (64-bit edition) | Remote Code Execution | Important | 5002687 | Security Update | CVE-2025-21394 |
| Microsoft Excel 2016 (32-bit edition) | Remote Code Execution | Important | 5002687 | Security Update | CVE-2025-21394 |
| Microsoft Office LTSC for Mac 2024 | Remote Code Execution | Important | Release Notes | Security Update | CVE-2025-21394 |
| Microsoft Office LTSC for Mac 2021 | Remote Code Execution | Important | Release Notes | Security Update | CVE-2025-21394 |
| Microsoft Office 2016 (32-bit edition) | Remote Code Execution | Important | 5002686 | Security Update | CVE-2025-21392 |
| Microsoft Excel 2016 (64-bit edition) | Remote Code Execution | Important | 5002179 | Security Update | CVE-2025-21390 |
| Microsoft Excel 2016 (32-bit edition) | Remote Code Execution | Important | 5002179 | Security Update | CVE-2025-21390 |
| Microsoft Excel 2016 (64-bit edition) | Remote Code Execution | Important | 5002684 | Security Update | CVE-2025-21387 |
| Microsoft Excel 2016 (32-bit edition) | Remote Code Execution | Important | 5002684 | Security Update | CVE-2025-21387 |
| Windows Server 2012 R2 (Server Core installation) | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2012 R2 | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2012 (Server Core installation) | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2012 | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation) | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 R2 for x64-based Systems Service Pack 1 | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation) | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 for x64-based Systems Service Pack 2 | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation) | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Windows Server 2008 for 32-bit Systems Service Pack 2 | Spoofing | Important | 5051972 | IE Cumulative | CVE-2025-21377 |
| Microsoft HPC Pack 2016 | Remote Code Execution | Important | Release Notes | Security Update | CVE-2025-21198 |
| Microsoft HPC Pack 2019 | Remote Code Execution | Important | Release Notes | Security Update | CVE-2025-21198 |
| Microsoft Surface Hub | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Pro 9 ARM | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Surface Windows Dev Kit | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Pro 8 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Laptop Go | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Go 2 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Hub 3 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Surface Laptop 3 with Intel Processor | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Hub 2S | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Pro 7+ | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Surface Laptop 4 with AMD Processor | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Laptop Go 3 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Go 3 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Surface Laptop Go 2 | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Surface Laptop 4 with Intel Processor | Security Feature Bypass | Important | CVE-2025-21194 | ||
| Microsoft Outlook for Android | Spoofing | Important | Release Notes | Security Update | CVE-2025-21259 |
| Visual Studio Code | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-24039 |
| Microsoft AutoUpdate for Mac | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-24036 |
| CBL Mariner 2.0 ARM | nodejs | CBL-Mariner | CVE-2023-32002 | ||
| CBL Mariner 2.0 ARM | nodejs18 | CBL-Mariner | CVE-2023-32002 | ||
| CBL Mariner 2.0 x64 | nodejs | CBL-Mariner | CVE-2023-32002 | ||
| CBL Mariner 2.0 x64 | nodejs18 | CBL-Mariner | CVE-2023-32002 | ||
| Microsoft Visual Studio 2019 version 16.11 (includes 16.0 – 16.10) | Remote Code Execution | Important | Release Notes | Security Update | CVE-2023-32002 |
| Microsoft Visual Studio 2022 version 17.12 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21206 |
| Microsoft Visual Studio 2022 version 17.10 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21206 |
| Microsoft Visual Studio 2022 version 17.8 | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21206 |
| Microsoft Visual Studio 2017 version 15.9 (includes 15.0 – 15.8) | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21206 |
| Azure Network Watcher VM Extension | Elevation of Privilege | Important | Release Notes | Security Update | CVE-2025-21188 |
Quality and experience updates
Microsoft has released the KB5051987 and KB5051989 patches for Windows 11 versions 24H2 and 23H2, respectively. These updates bring several new features for Windows 11 users, including improved previews for apps on the taskbar, a new Windows Studio Effects icon in the system tray, File Explorer improvements, and mouse performance enhancements.
On Windows 11 version 23H2, there is also a OneDrive continuity feature that asks users if they want to resume work on OneDrive files that they recently opened on their phone. However, this feature currently doesn’t support work and school accounts.
For Windows 10 version 22H2, Microsoft rolled out the KB5051974 update to automatically replace the Windows Mail and Calendar apps with the new Outlook for Windows client. Users will see a new app icon for the new Outlook client in the Start menu’s Apps section.
Windows Update testing and best practices
Organizations looking to deploy this month’s patches should conduct thorough testing before deploying them widely on production systems. That said, applying the patches widely shouldn’t be delayed longer than necessary as hackers start to work out how to weaponize newly reported vulnerabilities.
A best practice is to make sure you have backed up systems before applying updates. Every month, users experience issues with Windows updates that lead to systems not booting, application and hardware compatibility issues, or even data loss in extreme cases.
There are backup tools built into Windows and Windows Server that you can use to restore systems in the event a patch causes a problem. The backup features in Windows can be used to restore an entire system, or files and folders on a granular basis.