One of the highlights of every RSA Conference is the Cloud Security Alliance (CSA) Summit, which is traditionally held on Monday morning of the RSA Conference. This year’s summit was well-attended, with IT security professionals packing the hall to hear from a variety of cloud security experts.
There were several presentations throughout the morning, but two in particular stood out for me: A panel on the top security challenges facing enterprises who adopt the cloud, and another panel that provided feedback on cloud security from a number of the largest cloud service providers, including Amazon, Google, and Microsoft.
Security challenges for companies that adopt the cloud
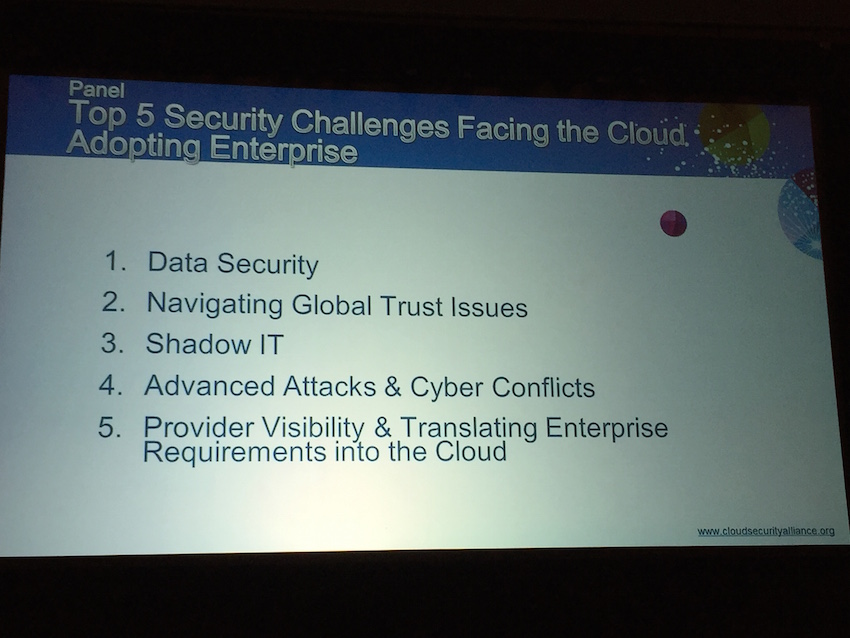
In a wide-ranging discussion about the top security challenges facing businesses who adopt the cloud, six security experts highlighted five cloud security challenges that all IT professionals should be mindful of, namely:
- Data Security
- Navigating Global Trust Issues
- Shadow IT
- Advanced Attacks & Cyber Conflicts
- Provider Visibility & Translating Enterprise Requirements into the Cloud
When it comes to overall data security, John DiMaria of the British Standards Institution suggested that security admins needed to focus on an overall approach to security rather than on traditional perimeter defense. “[Sometimes] you can be too reliant on technology…and what I’d call an ‘eggshell’ protection model: The exterior is hard, but the internal is very soft,” DiMaria said. “There’s a fundamental difference between IT security and information security.”

Chenxi Wang, the VP of Cloud Security & Strategy for CipherCloud, said that data loss prevention (DLP) systems could use improvement. “Traditional DLP systems don’t work, and this remains a huge data loss problem,” Wang said. “Technical solutions that solve narrowly-define problems [aren’t the answer]…we need to focus on the content.” Jay Chaudry, the Chief Executive Officer and Founder of Zscaler, agreed that there was “…no one answer to the DLP problem.”
Enterprise Lessons: The Cloud Provider Perspective
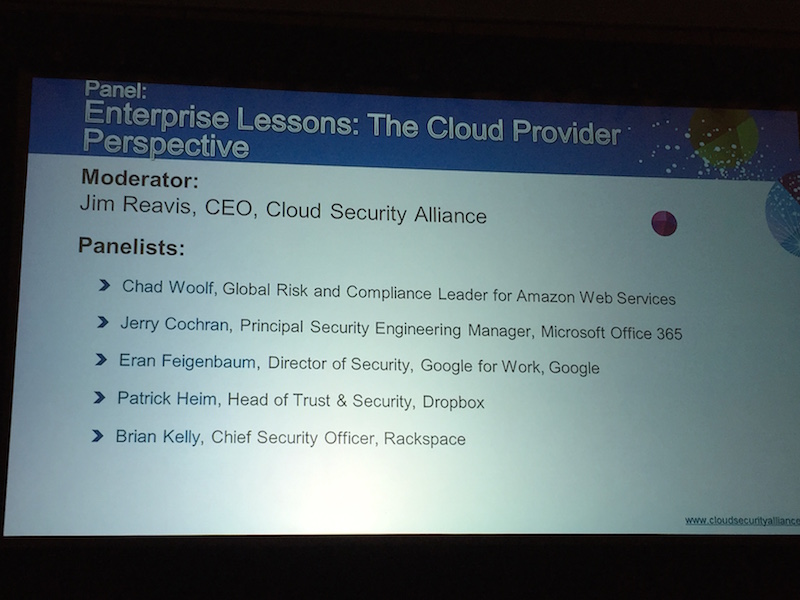
With an increasing number of IT organizations moving workloads into the cloud, the state of cloud security is becoming increasingly important. Getting the perspective of cloud providers on the state of IT security was the focus of the last panel of the conference, which featured executives from Microsoft, Google, Amazon, Rackspace, and Dropbox.

Improving Cloud Security: 2FA, Log Everything, and There are no Silver Bullets
One of the consistent themes mentioned by all of the panelists is the importance of users turning on two-factor authentication for users accessing cloud services. “User authentication is still a big problem,” said Eran Feigenbaum, the Director of Security for Google for Work for Google.
Patrick Heim, the Head of Trust & Security for Dropbox, suggested that IT administrators should “…turn on two-factor authentication for everything you can” and suggested that bad actors trolling for cloud service user credentials had almost reached an “epidemic level.”
Another step that all the providers urged admins to take was to turn on logging, which provides a wealth of information about who is accessing what files, when access is being made, etc. In nearly all cases these logging features are free and readily available, but not all cloud service users may know about them.



