In this four part series, we covered how Windows Firewall started out in Windows XP (in part one), the changes to Windows Firewall in Windows XP SP2 (in part two), and how Windows Firewall evolved with Windows Vista.
In this article we will take a look at the final sets of enhancements that we have available today in Windows 7.
Basic Functionality of the Windows 7 Firewall Service
The Windows 7 Firewall service performs many of the same functions as its Windows Vista predecessor with a few moderate changes.
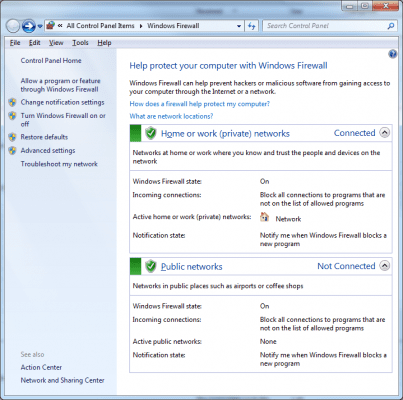
When you open the Windows Firewall from Control Panel –> All Control Panel Items –> Windows Firewall you can see all of the base configuration settings that you can adjust on the system.
As you can see from the screen shot above, one of the added basic functionalites is the ability to configure the firewall service on a network by network basis as each network connection can be assigned its own firewall profile separate of other connections on the computer.
In prior versions of the Windows Firewall service, only one firewall profile could be active at a time. When a system was configured to use multiple networks (e.g. wireless and wired where one was set to DOMAIN and the other set to PUBLIC) the firewall profile that was used for both networks was the one with the most restrictive rule set.
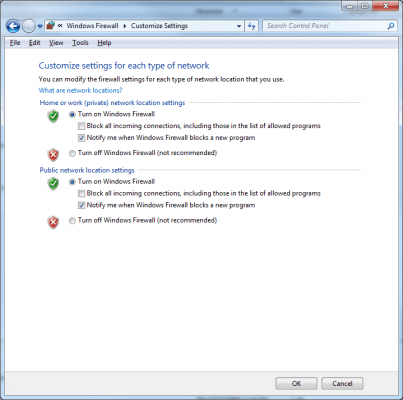
When you need to make changes to the notification settings you can make this selection via Control Panel –> All Control Panel Items –> Windows Firewall –> Customize Settings as shown below.
As you can see from the image above you have the ability to make the individual changes separately to the Home or work (private) network location setting or to the Public network location setting.
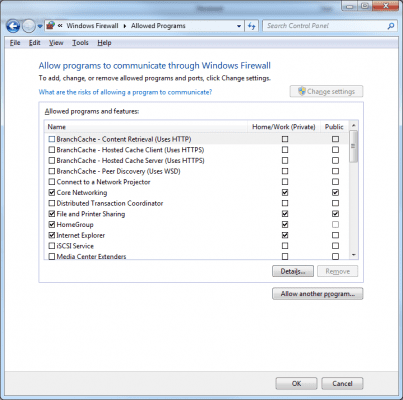
If you need to change the settings for program so that it can communicate successfully through the firewall this can be done by going to Control Panel –> All Control Panel Items –> Windows Firewall –> Allowed Programs as shown below.
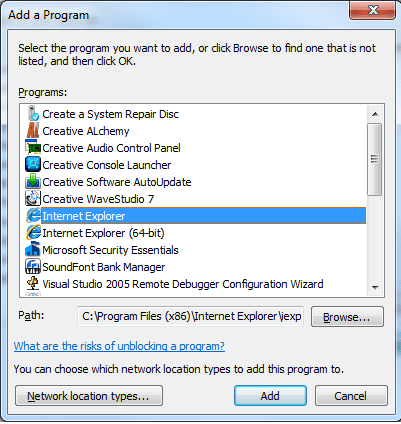
Once you are on this page you can select any of the programs in the list or choose the Allow another program option to Add a Program from the secondary list or by entering the path to the executable or browsing to it.
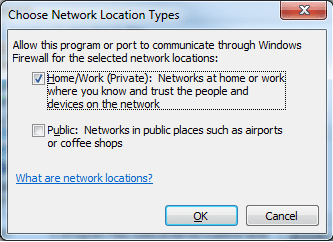
Once you have the application identified you can set the network location type by choosing that option on the page which will bring up the Choose Network Location Types window as shown below.
As you can see, you have the ability to select different network locations for the application from this view.
Windows 7 Firewall Advanced Security Basic Settings
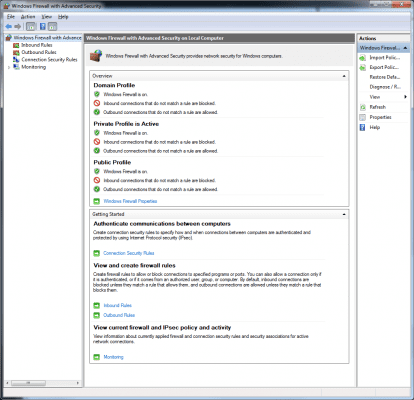
One of the major advances in the Windows Firewall service on Windows 7 is the ability to configure advanced settings for your system through the Windows Firewall with Advanced Security MMC.
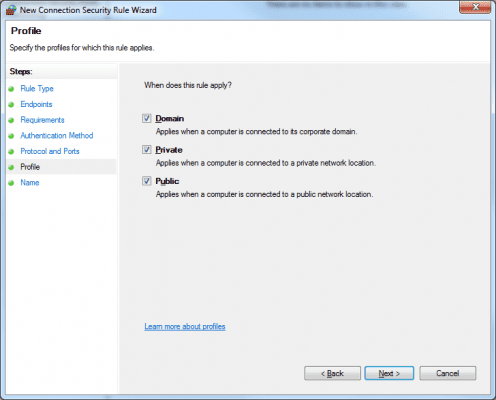
From the main results pane you can work from the overview section and see the current settings for each profile – Domain, Private and Public.
If you want to review the Windows Firewall Properties you can from this section by following the Windows Firewall Properties link which will open a new set of properties pages as shown below.
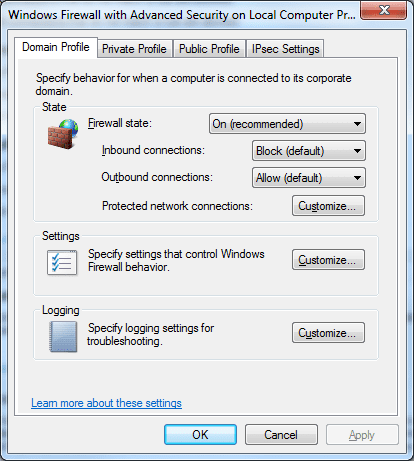
This property page breaks down on the individual tabs, each of the profiles separately if you wanted to make individual changes.
We will review the subsections of the Domain Profile next, understanding that these could be independently changed on the Private Profile and / or Public Profile tabs.
You can review in the STATE section of the property page whether the Firewall state is set to On (as recommended) or if it is turned off.
The default setting for inbound connections is Block (default) but you have the option to change this setting to BLOCK ALL CONNECTIONS or ALLOW.
The Outbound connection setting is listed as Allow (default) but if / as needed this could be changed to BLOCK.
By choosing the CUSTOMIZE option you can elect to choose which networks to apply these settings to if you have more than one available network connection. (e.g. two physical connections present or a physical and a wireless connection; you can apply the settings for each profile to one or the other or both as desired).
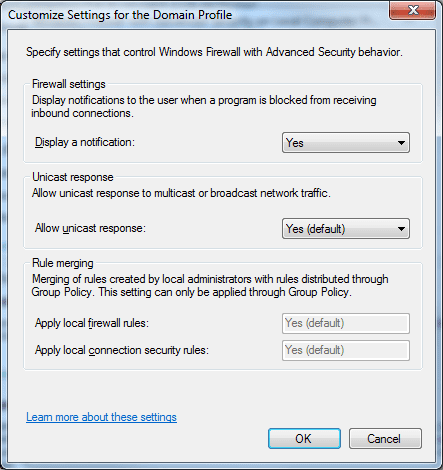
In the SETTINGS section you can customize the settings that control the behavior of the firewall service as shown below.
In the Firewall settings section of the Specify setting that control Windows Firewall with Advanced Security behavior dialog box you can set the behavior regarding the display of notifications that are presented to the end user when a application is blocked from receiving inbound connections.
The default setting is YES and the other option is NO.
The notification of a blocked inbound connection attempt will appear when YES is enabled and there is no separate existing block or allow rule for this application. If a block rule exists, then the application is blocked without displaying the notification to the user.
If the default behavior of Windows Firewall is to block a application, no notification will be displayed
When the notification is displayed to the end user they are given the option to unblock the application if they have network operator or administrator permissions. If the user chooses the action to unblock the application a new inbound rule is created for the application automatically.
From this same property page you have the option to allow unicast response to multicast or broadcast traffic (and the default setting is YES).
You’ll want to allow this setting if you need to control whether the system receives unicast responses to its outgoing multicast or broadcast messages. When the system sends multicast or broadcast messages to other network devices, Windows Firewall with Advanced Security waits as long as 4 seconds for unicast responses from the other systems and then blocks all later responses.
If you change the default setting and disable this setting by selecting NO, Windows Firewall with Advanced Security blocks all unicast responses sent by other systems.
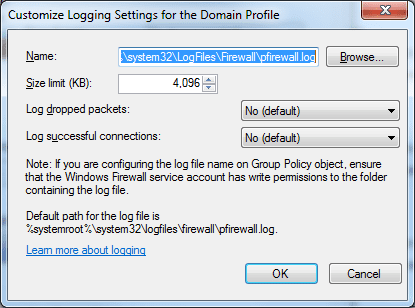
Back on the main Windows Firewall with Advanced Security on Local Computer properties page in the logging section you have the ability to specify the logging settings for each profile as shown below.
You have the ability to redirect where the log is stored (it is stored in %systemroot%\system32\LogFiles\Firewall by default with a file name of pfirewall.log)
The default size limit is 4,096 KB.
The default settings for logging dropped packets and successful connections is NO by default but you can enable these settings as needed.
Additional Changes to Windows Firewall in Windows 7
Windows 7 Firewall with Advanced Security offers additional changes from the prior iterations of Windows Firewall.
Some of these changes include:
Authorization exceptions – As a systems administrator you have the ability to create inbound firewall rules indicating users or computers that have access authorization to the Windows 7 system over the wire. At a more granular level, you can now specify exceptions to inbound firewall rules meaning that while all systems can connect, users or systems that fit the exception rule are denied network access.
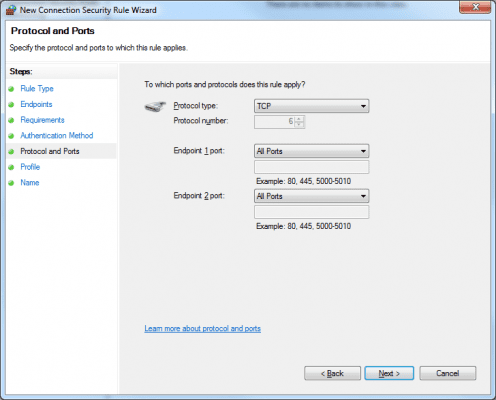
Support for specifying port ranges for rules – Windows 7 firewall now has more flexibility when it comes to port rules as administrators can now specify ranges of port numbers rather than ports one at a time. When rules are created for applications that need access to a range of ports of the same protocol type, it can be set through one rule.
Additionally, these rules can be set to one, some or all profiles.
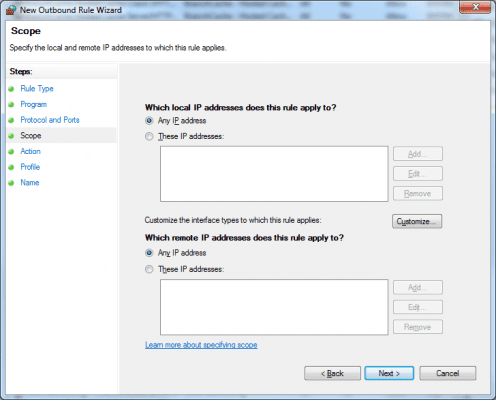
Scope settings for local and remote IP addresses – When you create new rules (inbound or outbound) you can set a specific local IP address or any of them.
As shown below you can also set which remote IP addresses the rule applies to – designated or all.
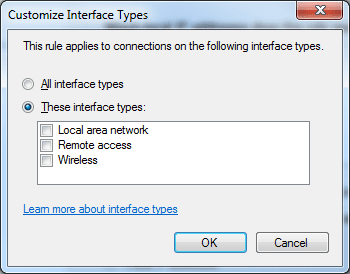
By choosing the Customize button on this page of the wizard you are able to choose the specific interface types that the connection rule applies (all or specific ones).
In this tutorial we reviewed the Basic Functionality of the Windows 7 Firewall Service as well as some of the basic Advanced Security settings. We wrapped up the tutorial with some of the additional changes to Windows Firewall service in Windows 7
Thanks for investing your time in my Evolution of the Windows Firewall series!
I am always looking forward to any feedback you have on this or any of the articles I have written so feel free to offer your feedback!