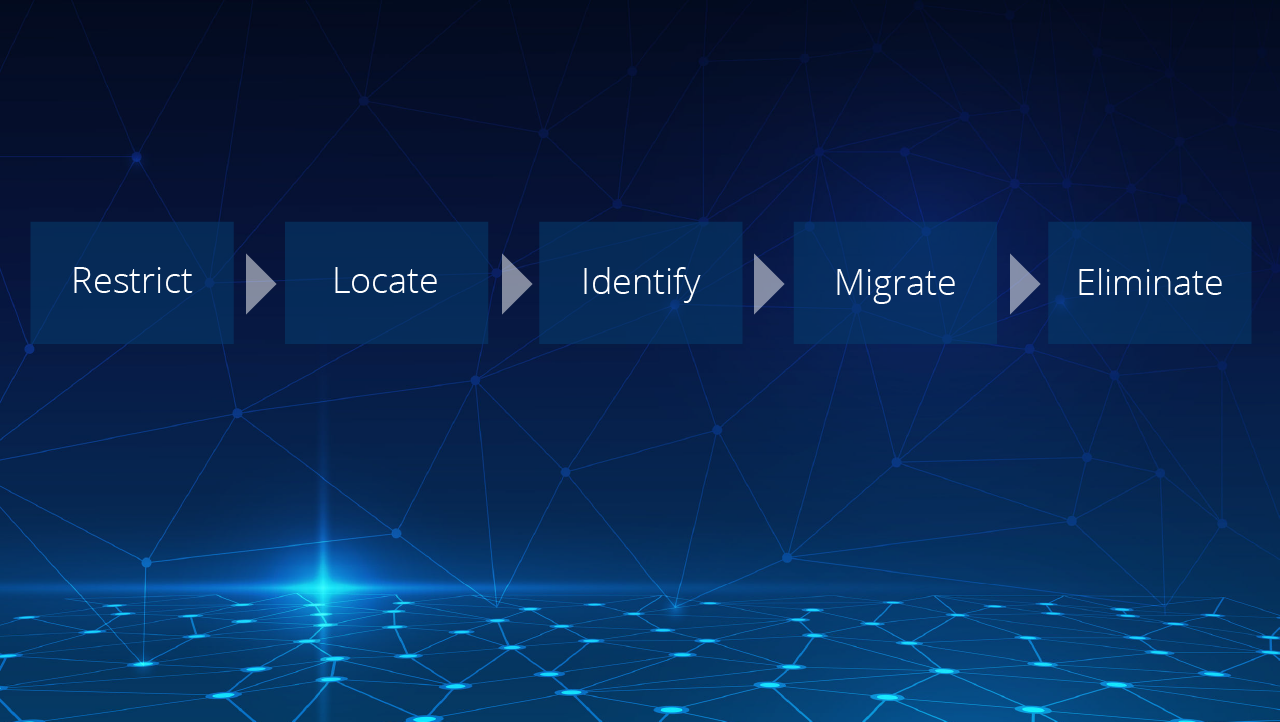
For a long time, email archives and PST files have been commonly used by many organizations, and therefore eliminating them might seem like a daunting task. In the first post in this series, I introduced the five phases of an archive elimination project (Restrict, Locate, Identify, Migrate, and Eliminate) and discussed the Restrict phase in more detail. In this post, we’ll take a closer look at each of the remaining phases.
Locate
The Locate phase is often the most difficult and time-consuming, especially when hunting down PSTs. The goal of this phase is to locate archives and PSTs across the organization and move them to a central location for further processing in later phases. Archives are usually simpler to locate because they exist in one or more archive solutions. PSTs, however, could exist in file shares, on network storage devices, on client workstations, or in all of these locations. PowerShell can be very useful when trying to locate PSTs, but don’t underestimate user self-service options. Self-service need not be complex and can be as simple as instructing users to rename and copy their PSTs to a file share. I once saw an organization develop their own self-service web portal to help facilitate the collection of PSTs and it worked really well for them, but this solution might be overkill in many other environments. A lot can be achieved with a small amount of end-user training.
This phase can also assist the Identify phase. For example, once you locate an archive or PST, you could rename it to reflect the identity of the user it was gathered from. This could help to remove a lot of guesswork later.
Identify
Once you have located all the PSTs across the organization, it is important to determine who owns them. This can be done several different ways, and often a combination of tactics will yield the best results. You can determine the PST file owners based on the
- File name
- File owner
- Message headers inside the archive
This phase is also where you identify the data that will be migrated and the data that will be discarded. Make sure you resist the temptation to migrate data that you no longer need to keep or offers no business value.
Migrate
As the name suggests, the Migrate phase is where the actual data migration occurs. Depending on the archive solution being used, your migration options might be limited to PST extraction or third-party migration tools. When migrating PSTs, there are few native options and many of those don’t scale well in large environments. Microsoft does offer a PST import service for Exchange Online, but third-party migration tools are also available.
Eliminate
Once you have migrated the data, it is time to get rid of the old archives and PSTs. In most cases, this data is simply deleted, but there are some organizations that prefer to archive the data to offline media for a period of time before completely deleting it.
This is also a great time to decommission any archive solutions that are in use, which will, in turn, reduce or eliminate the costs associated with managing and supporting them.
Eliminating archived email and PSTs doesn’t need to be overwhelming. Here are a few recommendations to make your project successful.
- First, it is important to decide if you really need all the data that was archived or in PSTs. A clear understanding of any legislation and regulatory requirements will help you determine which data offers business value and should be migrated.
- Consider using a third-party migration tool. Although it is very tempting to use PowerShell and native ingestion options, these often require a huge time investment. A third-party migration tool will greatly reduce the length and complexity of your project.
- End-user communication during all phases of the project is important. Let them know what is happening and what they can expect once the project is completed.
Individual PST files are troublesome enough, but what about Shared PST files and all the issues that they can cause? The Investigative Toolkit for Shared PSTs explores why PST files end up in shared locations and outlines how to successfully identify suitable targets ahead of a migration.