Setting Up Mobile Messaging in Exchange 2007, Part 2
In the first part of this series, I began walking you through the process of synchronizing a Windows Mobile 6.1 device to an Exchange 2007 mailbox. As you will recall though, the synchronization process failed. In this article, I want to wrap things up by showing you how to correct this issue.
Attention Required
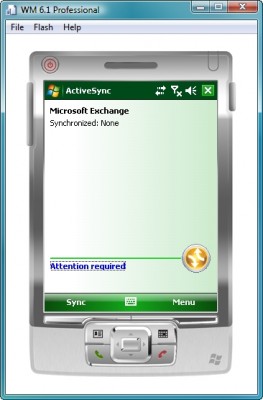
When I concluded Part 1 of this series, we were left with a mobile device screen that indicated that attention was required, as shown in Figure A. Assuming that you have entered your E-mail address, authentication credentials and the name or IP address of your Exchange Server correctly, and the mobile device has basic network connectivity, this error message is almost always related to the device not trusting the Exchange Server’s SSL certificate.
Figure A
The Attention Required error often indicates that the mobile device does not trust your Client Access Server’s SSL certificate.
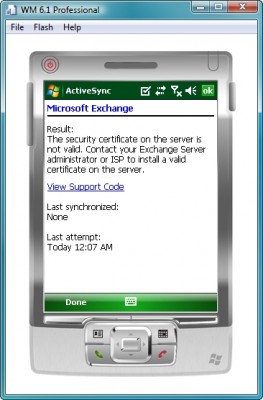
Of course you can find out for sure what the reason for the failure is by simply clicking on the Attention Required link. An error message such as the one shown in Figure B indicates that the SSL certificate is the problem. In the case of a problem with the SSL certificate or with general connectivity, the error message shown when you click the Attention Required link is fairly self explanatory. In other situations, you may just receive an error code. If you receive such a code, you can go to http://support.microsoft.com and look up the code in the Microsoft Knowledgebase.
Figure B
Clicking on the Attention Required link provides you with the details of the error message.
The exact method for fixing an SSL certificate trust issue varies depending on the type of SSL certificate that is being used. Assuming that you have generated the certificate from your own enterprise certificate authority, then you should connect the mobile device to the certificate authority’s Web site by entering https://server name/certsrv (or http://server name/certsrv if for some reason SSL encryption is not required for your certificate server). Upon doing so, Windows Mobile will connect to your enterprise certificate authority, and will prompt you to enter a set of authentication credentials.
Once you log into the server, scroll to the bottom of the following page that you are taken to, and click the option to download a CA certificate, certificate chain, or CRL. On the following screen, you must choose the option to download the CA certificate in Base 64 format. Windows will now ask you if you want to open the file after it is downloaded. You must click Yes. This will cause the certificate to be installed automatically once the download completes.
ActiveSync
Now that the required certificate is in place, our Windows Mobile device should trust our Enterprise Certificate Authority, and more importantly, it should trust our Client Access Server. Before we attempt to perform another synchronization though, there are a couple of settings that you should take a moment to verify.
Begin by opening ActiveSync, and then clicking on the Menu button. Click the Configure Server option. Click Next, and you should see a screen that displays the server’s name, as shown in Figure C. Since we are using SSL encryption, the name entered on this screen must match the client access server’s fully qualified domain name. The name that you enter here absolutely must match the name contained in the client access server’s SSL certificate. Otherwise, you will have a mismatch on your hands, and the encryption process will fail.
Figure C
You must make sure that the server name matches the client access server’s fully qualified domain name.
The other thing that you need to verify is that the This Server Requires an Encrypted (SSL) Connection check box is selected. It has been my experience that if you forget to select this check box, then the synchronization will fail, even if all of your settings are correct.
Conclusion
The synchronization process should now work. One thing to bear in mind is that my Enterprise Certificate Authority is running on Windows Server 2003. I have heard unconfirmed rumors that Windows Server 2008 certificate authorities specifically block Windows mobile devices from making certificate requests. This is something that I hope to look into, and possibly write about in the future.