IPv6 Header vs IPv4 Header
- Blog
- Networking
- Post
Overview
When studying IPv6, one of the main things that differs from IPv4 is the complexity of the IPv6 header compared with that of its predecessor’s header. The IPv6 header was designed to be less complex and easier to process than the IPV4 header, and with efficiency as one of the main design elements. This article takes a look at the contents of the IPv6 header and how they compare with the contents of the IPv4 header.
IPv6 Header
Figure 1 below shows the contents of the main contents of the IPv4 header and will be used as a comparison to the IPv6 header elements.
Figure 1 – IPv4 Main Header
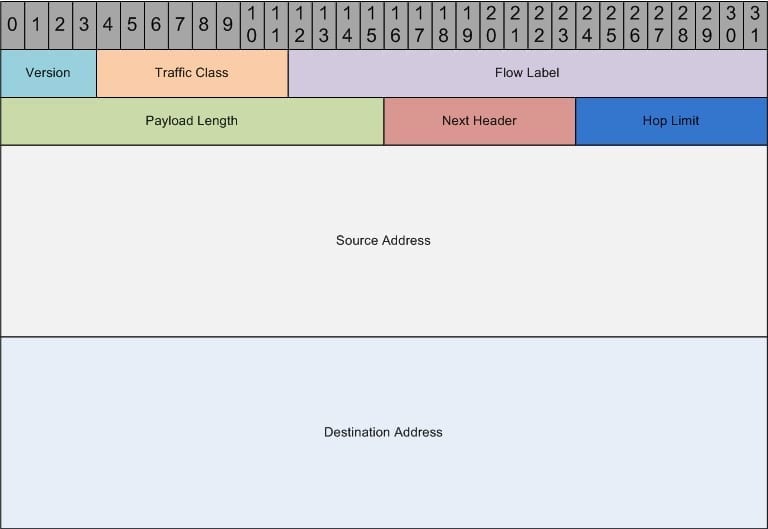
The main IPv6 header is shown in Figure 2 below:
Figure 2 – IPv6 Header
There are a number of unfamiliar fields within the IPv6 header but each of them replicates some of the functionality of the IPv4 header fields. Table 1 takes a look at each of these fields and what they are used for:
| Version | The version field is 4 bits long and contains the IP version to be expected in the following contents; since this article is talking about IPv6, this value is always going to be 6 (0110). |
| Traffic Class | The traffic class field is 8 bits long and operates the same as the IPv4 Type of Service field; this includes support for the marking of traffic based on a differentiated services code point (DSCP). |
| Flow Label | The flow label field is 20 bits long and is new to IPv6 and enables the ability to track specific traffic flows at the network layer. |
| Payload Length | The payload length field is 16 bits long and operates the same as the IPv4 length field; this field includes the length of the data portion of the IPv6 packet. |
| Next Header | The next header field is 8 bits long and operates similarly to the IPv4 protocol field. The next header field indicates what to expect after the basic IPv6 header; this includes options like a TCP or UDP header and packet. |
| Hop Limit | The hop limit field is 8 bits long and operates similarly to the IPv4 Time to Live field. This field is used to specify the maximum number of routers that the packet is allowed to travel through before being discarded. |
| Source Address | The source address field is 128 bits long and operates the same as the IPv4 source address field, with the exception of the length differences. |
| Destination Address | The destination address field is 128 bits long and operates the same as the IPv4 destination address field, with the exception of the length differences. |
Summary
With the exhaustion of the IPv4 address space just a short time away, it is in the best interest of any current or future network engineers to become familiar with IPv6. This includes the different header fields and address types, as well as how the different routing protocols are configured compared with their IPv4 counterparts. Keep on the lookout for a number of different IPv6 based articles, which should be coming out shortly.