Hive Ransomware Group Attacks Vulnerable Microsoft Exchange Servers

Security researchers have revealed a new series of ransomware attacks carried out by the Hive ransomware group to target Microsoft Exchange Servers. Hive is a popular ransomware-as-a-service (RaaS) model that was first discovered in June 2021.
The Hive ransomware group targets business networks with several methods and mechanisms, including phishing emails with attachments. It has previously targeted non-profit organizations, healthcare providers, financial companies, and the energy sector.
According to the Varonis Forensics Team’s report, Hive attackers are now exploiting the ProxyShell vulnerabilities in Microsoft Exchange Server. The Redmond giant released security patches to address the ProxyShell flaws in May 2021, but some organizations are still running vulnerable servers. The security vulnerabilities enable the hackers to gain system privileges on affected servers remotely.
Once exploited, the Hive ransomware group creates a new system administrator account and then uses Mimikatz to steal the NTLM hash. Furthermore, it allows threat actors to use the pass-the-hash technique to take full control of the account. The attackers can now scan the backup servers to access sensitive data and information.
Next up, a custom malware payload is deployed via a “windows.exe” file to perform specific tasks such as encrypting user files, clearing event logs, deleting shadow copies, as well as disabling security solutions. Finally, users will also see a ransomware note advising them to contact their sales representative via a website accessible through the Tor network.
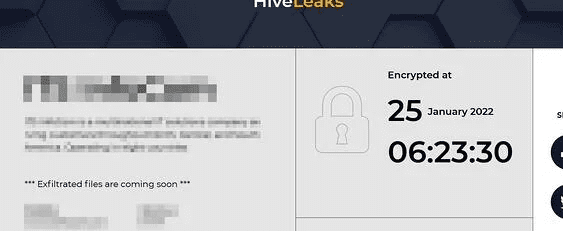
The Hive group threatens the organization to leak the sensitive data on the “HiveLeaks” Tor website if it refuses to make the ransomware payment. Additionally, the website shows a countdown timer to intimidate victims. The Varonis Forensics team added that it took less than 72 hours to attack a customer’s networks.
Security researchers recommend organizations to patch Exchange servers
“Ransomware attacks have grown significantly over the past years and remain the preferred method of threat actors aiming to maximize profits,” the Varonis Forensics team explained. “The impact of an attack can be detrimental. It may potentially harm an organization’s reputation, disrupt regular operations and lead to temporary, and possibly permanent, loss of sensitive data.”
The Varonis security team advises IT admins to ensure that the latest patches are installed on Exchange Servers to prevent ransomware attacks. Moreover, it is recommended that organizations should block SMBv1, enforce password rotation policies, and restrict employee account privileges based on their roles.



