The Friday Funny: Death Star Help Desk
We’ve already blogged about Stormtroopers guarding Google data centers and Star Wars-themed custom PC cases, but now it’s time for something completely different: A behind-the-scenes look at the IT help desk at the Death Star.
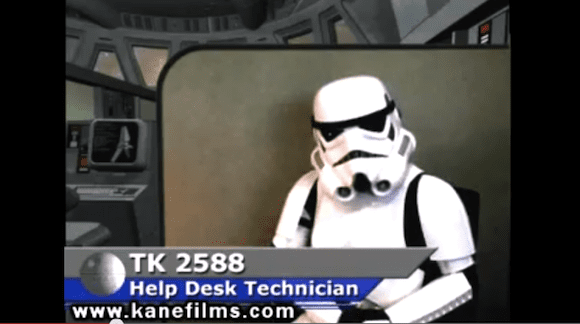
Produced by Kane Films, the short film shows a few minutes in the life of Imperial Help Desk Technicians (such as TK 2588, pictured) responding to all sorts of support requests from mostly clueless callers. Watch the video below and see for yourself what the IT department on the Death Star has to deal with.
So what do you think IT support on the Death Star would be like? Drop me an email with your thoughts.
- Follow Jeff James on Twitter (@jeffjames3) and Google+ (add Jeff to your circles)
- Follow Petri IT Knowledgebase on Twitter (@petri_co_il)
- Follow us on Facebook and Google+ as well!