
Cybersecurity researchers have discovered that the threat actors are testing new attack techniques to distribute malware. Indeed, the latest version of the highly sophisticated Emotet botnet uses PowerShell commands attached to the XLL files to target Windows PCs.
Emotet is an advanced Trojan that is primarily used to spread malware via phishing emails on compromised Windows systems. It was widely used as a backdoor to distribute ransomware before a global law enforcement operation shut down the servers in January 2021. The Emotet botnet reemerged in November with a massive email campaign aimed at thousands of customers worldwide.
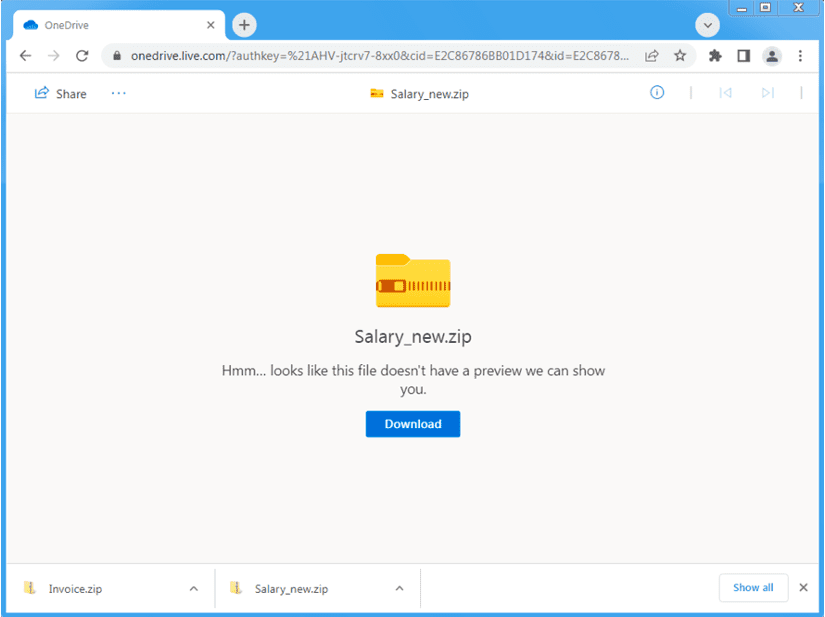
According to the security researchers at Proofpoint, the attackers are now targeting compromised email accounts to send phishing emails. These emails contain catchy subject lines (such as Salary) that entice the recipient to click on them. However, the email body includes a OneDrive URL that hosts zip files with Microsoft Excel Add-in (XLL) files. Once the recipient clicks and runs the Emotet payload, the XLL files infect Windows machines with malware.
Emotet campaigns are moving away from VBA macros
Unlike previous Emotet attacks, the latest campaign uses the XLL files containing PowerShell commands rather than Visual Basic for Applications (VBA) scripts. This change follows Microsoft’s announcement about its plans to block VBA macros by default across its products in April 2022. The Redmond giant says that this move should help protect customers from phishing attacks.
“After months of consistent activity, Emotet is switching things up. It is likely the threat actor is testing new behaviors on a small scale before delivering them to victims more broadly, or to distribute via new TTPs (Tactics, Techniques, and Procedures) alongside its existing high-volume campaigns,” explained Sherrod DeGrippo, VP of threat research and detection at Proofpoint.
Cybersecurity researchers have advised organizations to create awareness among employees regarding the new phishing techniques. It is also recommended that they should use simulated attacks and train employees in the cybersecurity domain.



