Azure Active Directory Gets SMS-based Authentication and Email Address Sign-In
Microsoft provides several different ways for users to log in to Azure AD without a username and password. For example, users can sign-in using the Microsoft Authenticator app or a FIDO2 security key. Azure Active Directory (Azure AD) is the identity management platform used by Office 365, Microsoft 365, and of course Azure. Organizations can also use Azure AD as the identity provider for their own cloud-based applications.
Azure AD SMS-based authentication
Now in preview, Azure AD SMS-based authentication lets users sign in using their registered mobile phone number. Users receive a text message that they use to confirm their identity. Before you can use SMS-based authentication, all users enabled in an SMS-message authentication policy must be assigned one of the following licenses:
- Azure AD Premium P1 or P2
- Microsoft 365 (M365) F1 or F3
- Enterprise Mobility + Security (EMS) E3 or E5 or Microsoft 365 (M365) E3 or E5
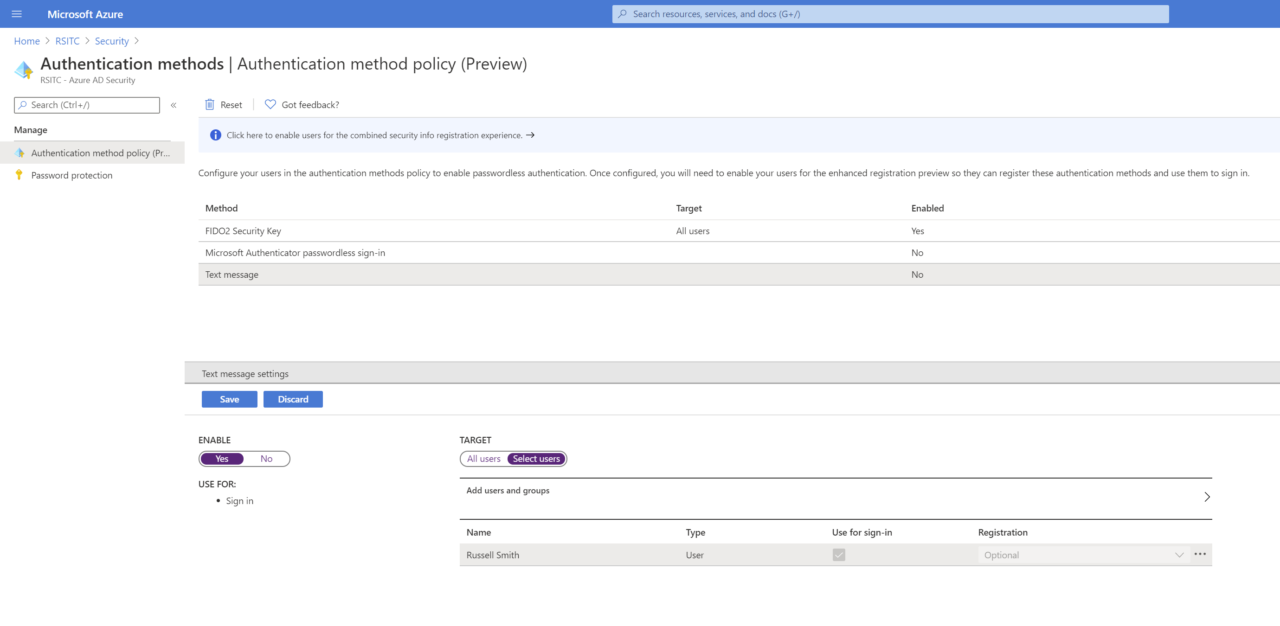
And while SMS-based authentication is in preview, it can’t be used with multifactor authentication (MFA) or native Office apps except Teams. Text message sign-in isn’t enabled by default in Azure AD. You can enable it under Authentications methods in the Security section of Azure AD management.
Users can either register their mobile phone number in the My Sign-Ins page of their account profile. Alternatively, Azure AD global admins, authentication admins, and privileged authentication admins can assign a phone number in the Azure portal to each user.
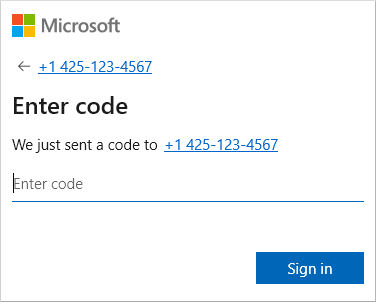
Once SMS-based authentication is enabled and users have a mobile phone number registered in Azure, they can enter their phone number in the Sign in dialog instead of their username. All the user then needs to do is wait for the SMS code to arrive and enter it to confirm their identity.
Azure AD alternate email address sign-in
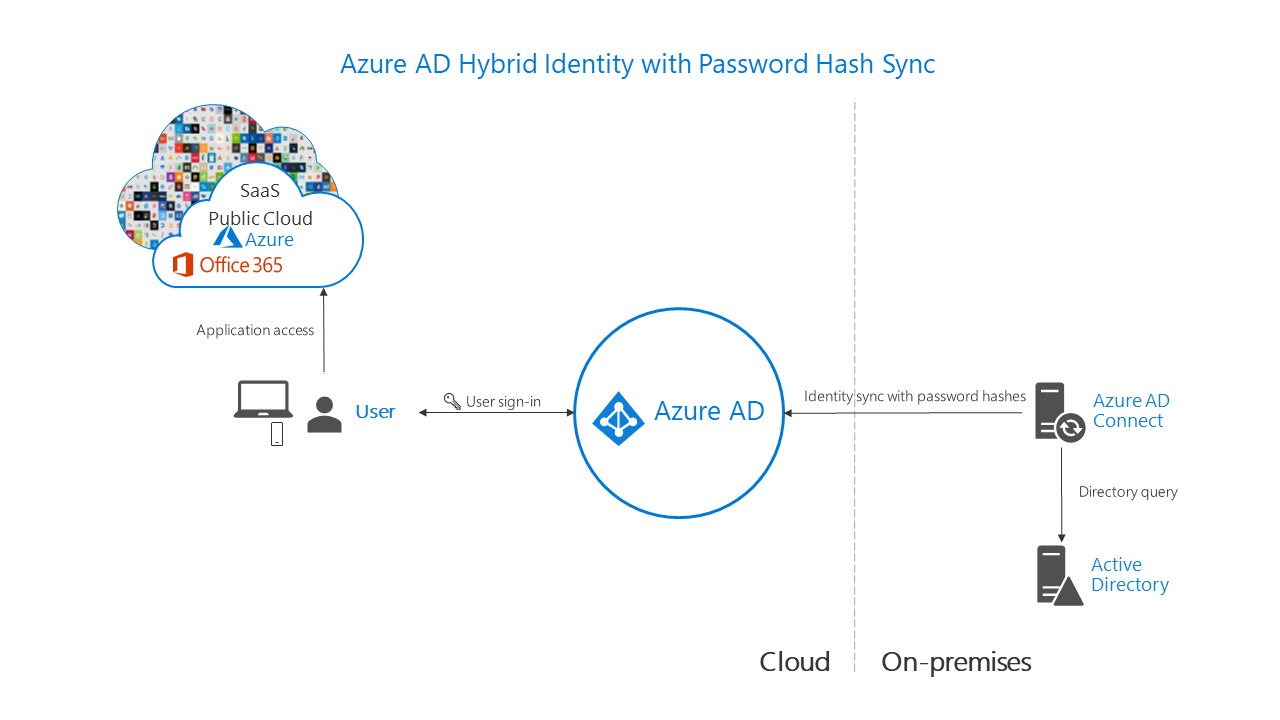
Also in preview, Microsoft now lets users sign in to Azure AD with an alternate email address. The idea is to help organizations move to hybrid authentication, which lets employees access both cloud and on-premises resources with a common user identity. Hybrid authentication is commonly achieved by synchronizing password hashes from Windows Server Active Directory to Azure AD using Azure AD Connect.
But because there might be a mismatch between the User Principal Name (UPN) configured in Azure AD and Windows Server Active Directory, users might still need to use different identities to log in to cloud apps and on-premises AD. UPN is a user’s login name in an email address format. And in some cases, businesses don’t want to use their Windows Server AD UPN to sign in to Azure AD for compliance reasons.
When signing in with an alternate email address is enabled in Azure AD, the email address configured in the ProxyAddress attribute in Windows Server AD can be used to log in to cloud apps. The only requirement is that the email address domain specified in the ProxyAddress attribute is verified in Azure AD.
Alternate email address login is set in the Azure AD HomeRealmDiscoveryPolicy. Creating or modifying an existing policy can be done using PowerShell. For instructions on how to enable alternate email login in Azure AD, check out Microsoft’s website here.