Product History
There used to be a saying in the IT industry that “you wouldn’t get sacked for buying IBM”; whilst that may be somewhat dated the same could be said for Cisco equipment nowadays. There are plenty of alternative vendors providing firewall solutions with many similar features and at a lower price but the industry standard is still Cisco. The Cisco PIX range of firewall/NAT devices was originally launched in 1995 but the models most readers are likely to encounter are the 501, 506 and 515 which were launched in 2002. They were finally discontinued in 2008, their longevity was mainly down to their use of the PIX OS which enabled new features to be provided via firmware upgrade without the need for major hardware updates. Although the Cisco ASA range was launched in 2005 and aligned as a replacement for the PIX range Cisco users tend to resist change and so ASAs have only started to become widespread in the last couple of years.
The original release versions of the ASA officially combined the separate firewall, VPN and IPS (Intrusion Prevention Systems) functionality of several Cisco devices, although the current PIX OS at the time (version 7.x) supported all these features. In fact the ASA range started life running PIX7.0 and only diversified with the release of version ASA8.0 which moved back in line with the main Cisco IOS by using their customized Linux based kernel.
For users from a Unix background this makes Cisco devices’ use of text files for all configuration settings reassuringly familiar but for those from a Windows background it can seem impossibly complex. Cisco attempted to address this first with the PIX by introducing the PIX Device Manager, a Java based GUI front-end for the PIX OS, however a frustrating number of bugs tended to drive admins back to the command line for any advanced configuration. Fortunately they started from scratch with the ASA and designed the ASDM (Adaptive Security Device Manager), again a Java based management console but this time one that allows you to do virtually all the configuration without having to resort to a text editor. The latest ASA version is now 8.2 and ASDM is on version 6.1:

ASA Models
There are six main models in the ASA range, from the basic 5505 branch office model up to the 5580 datacenter versions; a full comparison is available on the Cisco website here. Although this article will concentrate on the 5505 and 5510 models the basic feature set is in fact fairly consistent across the range, the main differences being in the maximum traffic throughput handled by each model and the number/type of interfaces.
At the most basic level the ASA is a transparent or routed firewall/NAT device, this means it is designed to sit between your LAN and the Internet; one interface (normally known as “outside”) will be connected to your Internet access device and one or more interfaces (e.g. “inside” and “DMZ”) will connect to your internal networks. This enables the ASA to inspect and control all traffic passing between your network and the Internet, exactly what it does with that traffic is the clever bit.
ASA 5510 
The ASA5510 is intended to be a single device solution to your Internet security requirements and with its 300Mbps throughput and 9,000 firewall connections per second capacity will be suitable for most office deployments. The key features will be covered in more detail later but in brief these are; firewall/NAT, SSL/IPsec VPN, content security and intrusion prevention. It has five 10/100Mbps ports, by default these provide one outside (Internet) interface, one management and three internal network interfaces but they are fully reconfigurable and also support vLANing for further network subdivision if required. Functionality can be upgraded via a Security Services Module port which provides support for additional Content Security and Intrusion Prevention features.
ASA 5505
The ASA5505 is intended for small or branch office and teleworker deployments, often in conjunction with a 5510 or higher model at the head office to which it will establish a secure VPN, whilst providing full security for other Internet traffic. The device has 8 10/100Mbps Ethernet ports, including 2 with Power over Ethernet support suitable for PoE devices such as IP phones or cameras, so it can be used as single unit solution for the smaller office. Key differences compared to the 5510 are the reduced support for VPN connections (only 10 but upgradeable to 25 with license), only 3 vLANs (25 with Security Plus license) and only a slot for the optional Security Services Card so there is no option for the advanced Content Security services.
Key Features
Firewall
All ASA models include a fully featured policy based firewall and routing engine which allows you complete control of which traffic you allow in and out of your network. Layer 2/3 firewalling allows you to specify which hosts are allowed access through the ASA and also to perform Network Address Translation to map internal hosts to public IP addresses. Layer 7 firewall goes several steps further and also allows you to define access policies based on application and protocol type, providing extremely granular control over Internet access and protection against advanced types of network attack. Unlike many competitor’s firewalls the ASA’s policy and interface based approach to access control gives you complete control over traffic leaving your network as well as incoming, for example allowing you to restrict Instant Messaging use to only your approved client application. Deep packet inspection goes beyond simply analysing the protocol and port of the attempted connection to discover the application behind it making it virtually impossible for users to circumvent company IT policies.
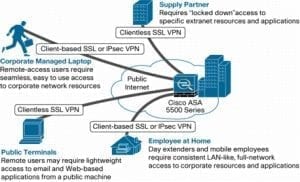
SSL & IPsec VPN
Even the ASA 5505 includes full support for IPsec and SSL VPN endpoints, providing highly encrypted tunnels for office to office and remote user to office connections. The basic license for all ASAs allows IPsec VPN connections up to the maximum supported on each model but only includes two SSL VPN licenses, to allow for testing before deployment. The 5505 will support up to 25 simultaneous VPN connections, whilst the 5510 supports a maximum of 250 – these can be any combination of IPsec or SSL, and site to site or remote client types.
IPsec VPNs are commonly deployed between Cisco VPN devices for site to site connections, or initiated by client software on the remote worker’s computer. Included with all ASA license bundles is the Cisco AnyConnect VPN client, with versions available for all major operating systems; Windows 2000 up to Windows 7, Mac OS X (10.4/5), Linux Intel kernel 2.6.x and even Windows Mobile 5.0/6.0/6.1 . Cisco AnyConnect provides several improvements over the basic IPsec functionality built into those operating systems, key features are:
- DTLS protocol support to help minimize latency for applications such as VoIP
- Support for SSL tunneling to ensure connectivity even through restrictive proxies and firewalls (if web browsing is possible then so is a VPN connection)
- Advanced encryption and wide range of authentication protocols, including two factor smartcard/token based
- Flexible IP tunneling for consistent user experience with features such as connection retention, ensuring the mobile user retains connectivity through disconnections, reboots and standby/hibernation.
Cisco’s SSL VPN makes supporting mobile and remote users even simpler, by using the same protocol as that used for secure web sites a VPN connection is available anywhere the user can browse the web. The SSL VPN can be initiated via an ActiveX or Java control so no client has to be pre-installed on the user’s system, all they have to do is browse to the website and provide the necessary credentials.
Intrusion Prevention
Cisco’s Intrusion Prevention System goes beyond the standard firewall functions to analyse data packets for known and potential threats, including malware, network intrusion and application exploitation. This ensures maximum network security by intercepting undesirable traffic before it reaches the internal network whilst regular automatic signature updates maintain protection against new threats. IPS support is an optional feature that can be added via the purchase of an AIP SSC (upgrade card) for the ASA5505 or an AIP SSM (upgrade module) for the ASA5510. The AIP SSM has all the standard features of the AIP SSC but with increased throughput capacity (150Mbps/9k connections per second vs 75Mbps/4k cps) and support for Global Correlation and Day Zero attack anomaly prevention. Global Correlation involves much more than regular signature updates, using a real time connection with the Cisco Security Intelligence Operations infrastructure to monitor the current threat status Internet wide, identifying and preventing fast spreading threats as they happen. Day Zero Attack Prevention analyzes your normal network behaviors so it can detect anomalous behavior representing potential threats and block it, even before official detection signatures have been released.
- AIP-SSC Intrusion Prevention System upgrade card for ASA5505
Content Security
Content Security is not available on the ASA5505 but can be added to the ASA5510 with the purchase of the CSC-SSM module. This provides a comprehensive range of network security and control features including:
- Malware scanning using Trendlabs protection to scan both Internet and email traffic and eliminate viruses, worms and other threats such as spyware.
- Anti-spam to remove unsolicited commercial emails
- Anti-phishing protects against spoofed identity attacks and prevents users disclosing confidential information inappropriately
- Comprehensive web access protection; all traffic is scanned so protection cannot be bypassed, e.g. through employees using personal webmail services which would not usually be protected by corporate email protection
- URL filtering and content protection – gives you full control over which employees can access what, definable by categories and content, again applying to all web access so undesirable content can be blocked whether on a website, in an email or in a file download.
CSC-SSM licenses are available in several different options according to the number of users supported and the feature set; basic licenses support Anti-virus and Anti-spyware while the advanced licensed add URL & Content filtering, Anti-spam and Anti-phishing. Security updates are provided by Trendlabs and licensed on a yearly subscription basis.
Conclusion
Cisco’s ASA range greatly extends the usual definition of a firewall to provide a complete network perimeter security solution, and with the 5505 and 5510 models what used to be “enterprise only” features are now available to the SME network. Having said that several of these features are not included with the basic device package; they have to be purchased as separate licenses, which is important to bear in mind when comparing costs. However this does allow you to tailor the device to your requirements, so you only pay for features as and when you need them.
With the ASDM GUI Cisco have gone a long way to reduce the complexities of configuration and management that used to be the hallmark of their appliances so deployment should be within the capabilities of most network admins too. The next article in this series will cover the basics of ASA setup and administration using the ASDM interface.