Security
- Blog
- Security
LATEST

Microsoft Sentinel Now Lets IT Admins Detect Low and Slow Password Spray Attacks
Last Update: Feb 02, 2023
- Aug 15, 2022
-
Microsoft has released a new guided hunting notebook for its Microsoft Sentinel solution. The notebook enables organizations to leverage machine learning to detect, investigate as well as block low and slow password spray campaigns. Password spraying is a type of brute force attack that allows malicious actors to gain unauthorized access to computer systems. Hackers…

Microsoft Sentinel Launches New Log4j Vulnerability Solution In Public Preview
Last Update: Feb 02, 2023
- Dec 22, 2021
-
Microsoft has announced some important updates for Microsoft Sentinel, its scalable cloud-native SIEM tool that provides AI-powered security analytics in enterprise environments. The Redmond giant has launched a new solution in public preview that should help IT Admins to detect Apache Log4j vulnerabilities. Last week, Microsoft acknowledged the emergence of an Apache Log4j vulnerability (CVE-2021-44228)…

Microsoft Warns About New Consent-Phishing Attacks Used to Steal Data
- Feb 01, 2023
-
Security researchers have discovered a phishing campaign that tricked users into authorizing permissions for malicious OAuth applications. Microsoft has disabled several fraudulent Microsoft Partner Network (MPN) accounts that breached organizations’ cloud environments. Microsoft explained in a security advisory that the security firm Proofpoint discovered the campaign in early December. The threat actors initially impersonated legitimate…

Microsoft Defender for Endpoint Adds Device Isolation Support for Linux Machines
- Jan 31, 2023
-
Microsoft Defender for Endpoint has introduced device isolation support in public preview on onboarded Linux machines. The security feature enables IT admins to isolate Linux machines manually via the Microsoft 365 Defender portal or API requests. According to Microsoft, the threat actors will no longer be able to remotely connect with the isolated Linux devices….

Bitwarden – An Open-Source Alternative to LastPass for Business and Personal Use
Last Update: Jan 24, 2023
- Jan 03, 2023
-
I’ve been using Bitwarden for the last couple of years and in this overview, I’ll look at why you might consider Bitwarden as an alternative to proprietary solutions like LastPass and 1Password. And I’ll give an outline of the pricing, architecture, and features for business and personal use. What is Bitwarden? Bitwarden is an open-source…
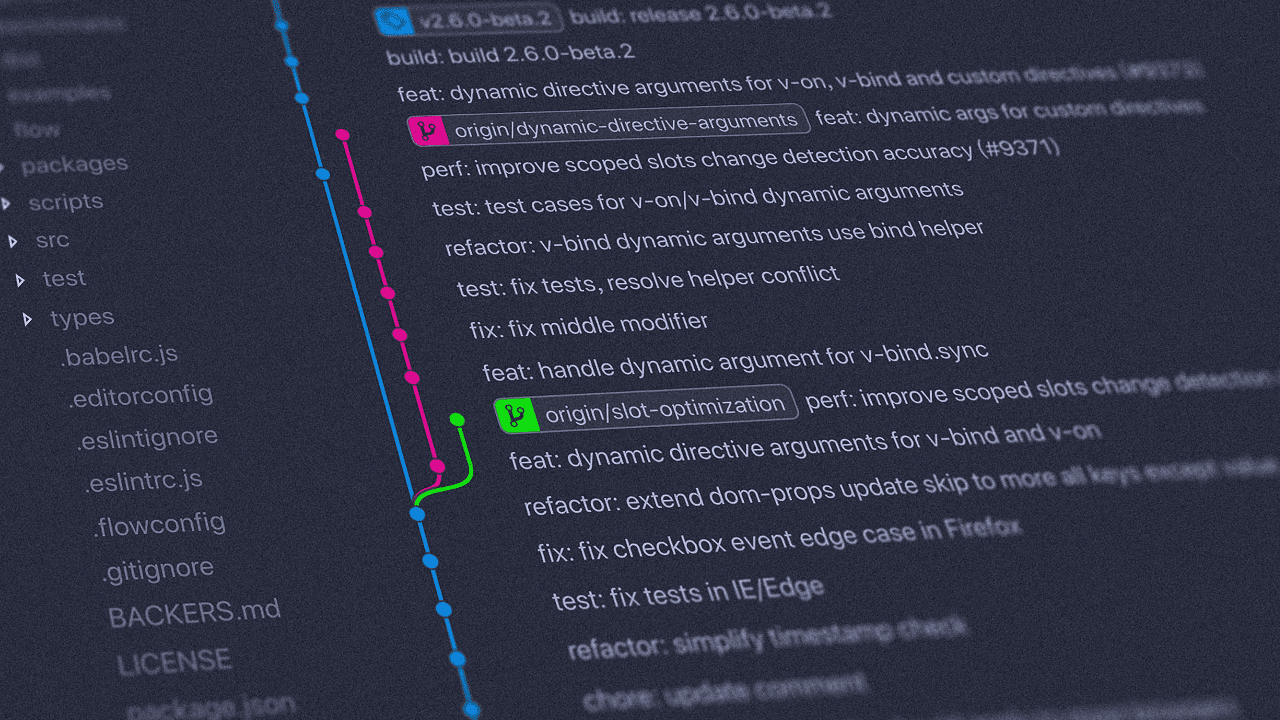
Git Releases New Security Updates to Block Remote Code Execution Attacks
- Jan 18, 2023
-
Git has recently released new updates to address two critical security vulnerabilities that could allow hackers to launch remote code execution attacks. The company has also patched another Windows-specific flaw affecting the Git GUI tool. Security researchers from X41 and the GitLab Security Research Team first identified the security vulnerabilities as part of an audit…
PyTorch Discloses Internal Dependency Compromised with Malicious Code
- Jan 04, 2023
-
Last week, PyTorch identified a supply chain attack that potentially caused developers to download a compromised PyTorch dependency. The PyTorch team published an advisory to warn developers that the package includes malicious code to steal system data. PyTorch is an open-source framework that allows Python developers to build machine-learning applications. It was mainly developed by…
Why You Should Restrict Access to Office 365 Using Microsoft Conditional Access Policies
Last Update: Jan 04, 2023
- Jun 15, 2022
-
Organizations adopting Microsoft’s cloud services need to keep their employees safe, especially when employees need to access these cloud services while being outside of the organization’s network. In this guide, we’ll explain how organizations can set up Conditional Access policies to restrict how their users can access Office 365 and other Microsoft services. What are…
How to Create Conditional Access Policies using PowerShell
- Jan 04, 2023
-
When working in a Microsoft 365 environment, IT pros can use Conditional Access policies to control access to their tenant. In this article, we’ll detail how to create Conditional Access policies using PowerShell instead of the graphical user interface, and why using PowerShell to do that can help you save some time Conditional Access policies…
LastPass Confirms Hackers Stole Personal Data and Encrypted Password Vaults
- Dec 23, 2022
-
Back in August, LastPass announced that its systems were compromised in a security incident. Now, LastPass CEO Karim Toubba disclosed that the threat actors managed to copy encrypted passwords and other data stored in customer vaults. In a blog post published yesterday, LastPass revealed that hackers accessed customer data such as names, telephone numbers, email…






