Azure AD: Set Up Self-Service Password Reset
In today’s Ask the Admin, I’ll show you how to set up self-service password reset in Azure Active Directory (AD).
One of the most time-consuming jobs for IT departments is dealing with users’ passwords. Microsoft claims that support-assisted password reset typically accounts for 20 percent of an organization’s IT budget. Practical problems can also impair the user experience, such as waiting for the help desk to respond to a password reset request, so any technology that reduces costs and improves the user experience, while keeping systems secure, is worth a look.
Because Azure AD can be integrated with on-premises AD, the self-service password features in the cloud can be extended to your onsite directory, although Azure AD Premium is required for that functionality. Azure AD Basic, or any Office 365 subscription, provides the ability for cloud-only users and cloud-only administrators to reset their own passwords, while the free Azure AD tier allows only cloud administrators to reset their own passwords. For more information on Azure AD, see What is Azure Active Directory? on the Petri IT Knowledgebase.
Before starting, you’ll need an Azure AD tenant connected to an Azure subscription. Additionally, at least two users assigned an Office 365, an Azure AD Basic, or Premium license already assigned. For more information about assigning licenses to users, see Use PowerShell to Create and Assign Licenses to Office 365 Users on Petri IT Knowledgebase. Licenses can also be assigned to users in the Office 365 management portal.
Password Reset Policy
Let’s start by enabling password reset policy in Azure AD.
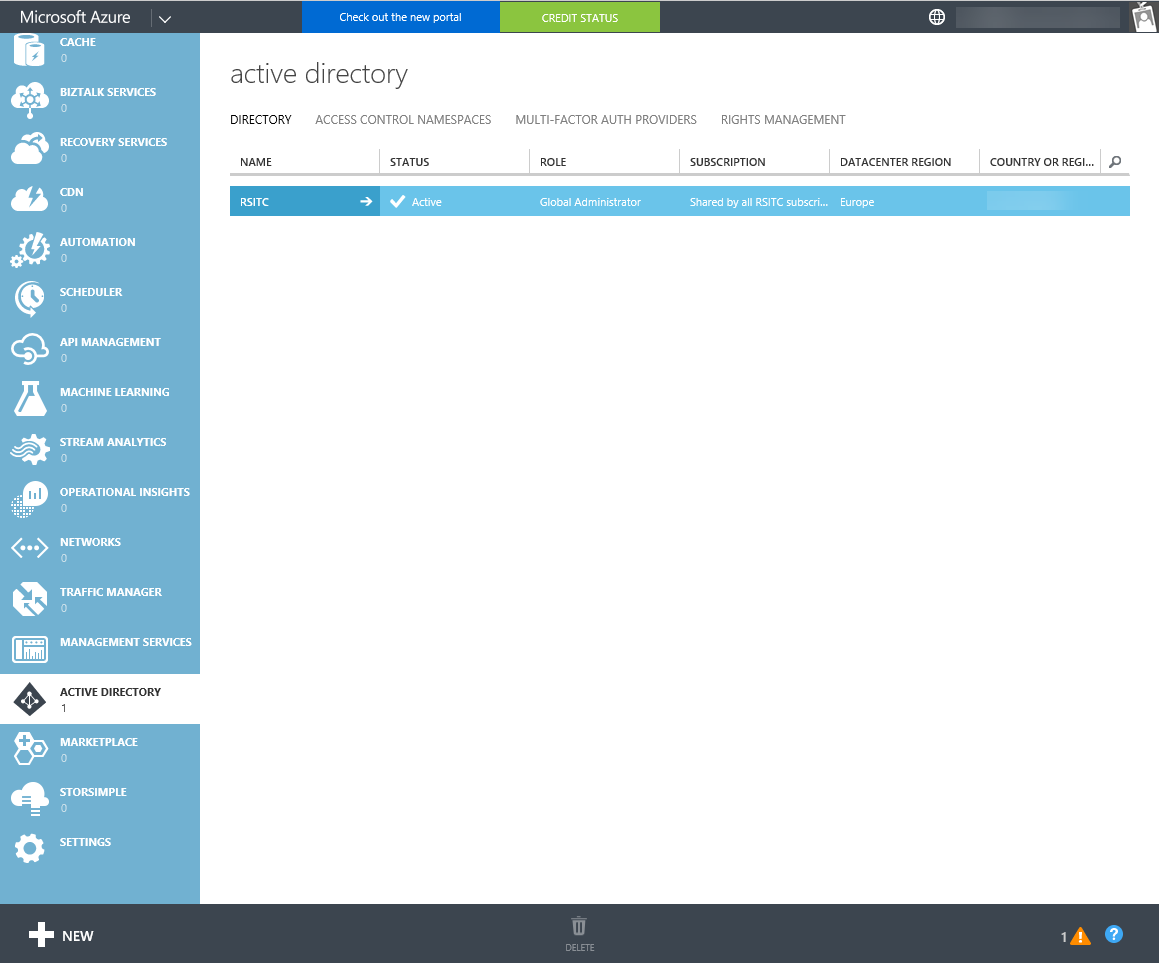
- Log in to the Azure classic portal here using an administrator account.
- In the portal window, click ACTIVE DIRECTORY in the list of options on the left.
- In the list of available directories, click the directory you want to modify.
- Switch to the CONFIGURE tab.
- Scroll down to user password reset policy and change the USERS ENABLED FOR PASSWORD RESET to YES.
The password reset experience can be customized with additional options that now appear in the portal window. For instance, you can specify if passwords can be written back to on-premises AD or determine the methods users may use for additional verification, such as a mobile number or alternate email address.
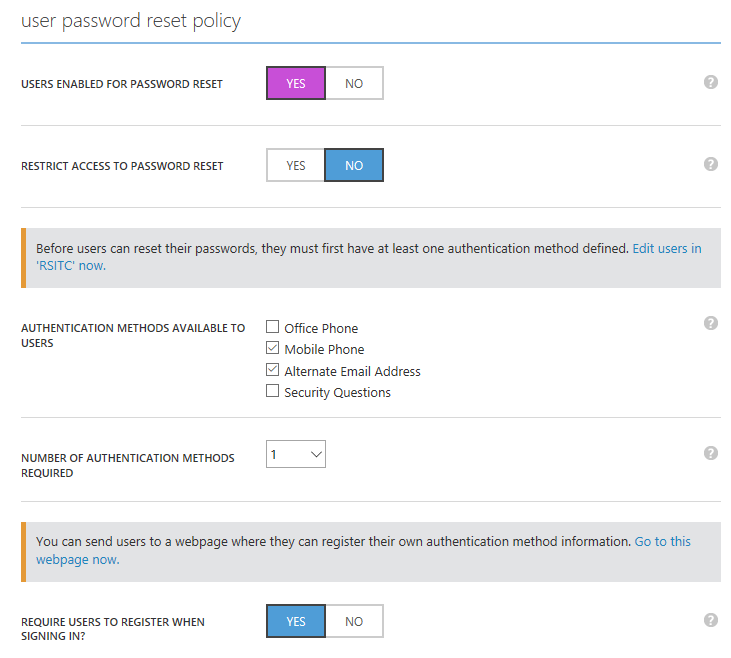
If you need more explanation about each setting, hover the mouse pointer over the question mark icon to the right of each option. In this example, I’ll leave the policy configuration with the default settings.
- Click SAVE at the bottom of the portal window.
Verify User Contact Data
Testing password reset requires that users have contact data information recorded in the directory. For example, if you allowed password reset using an alternate email address, then an alternate email address must be already stored in the directory for each user.
Users can log in to the User Registration Portal and provide the information themselves. If you have synchronization configured from on-premises AD, then contact information for users can be synchronized to the cloud. Administrators can also manually enter contact information for users in the Office 365 or Azure Classic admin portals.
When logging in to the User Registration Portal, users will be prompted to verify their contact details if an administrator has enabled password reset policy for the directory. If contact details don’t already exist for the user, they’ll be asked to provide and verify them.
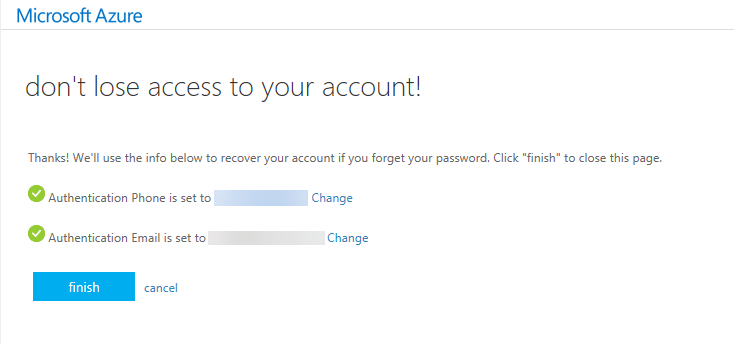
Perform a Password Reset
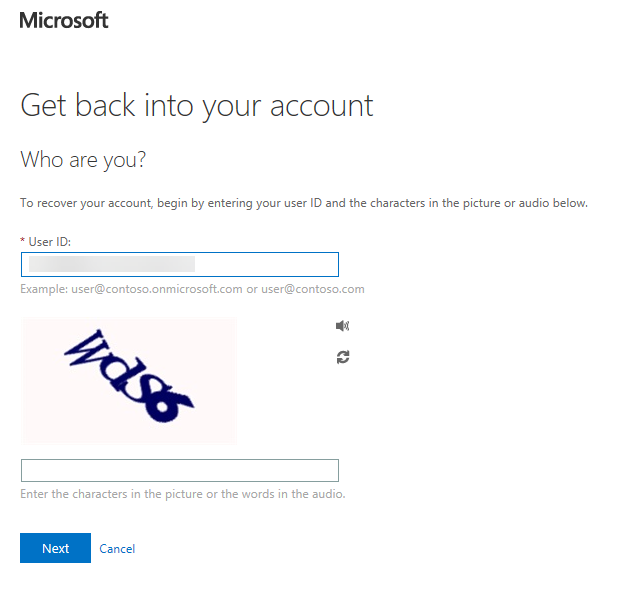
To test the password reset functionality, log in to a site that uses Azure AD for authentication, such as the Office 365 portal, and click the Can’t access your account? link.
- Click Work or school when prompted to choose the account type.
- On the Get back into your account screen, confirm the user ID, and enter the characters in the picture as prompted.
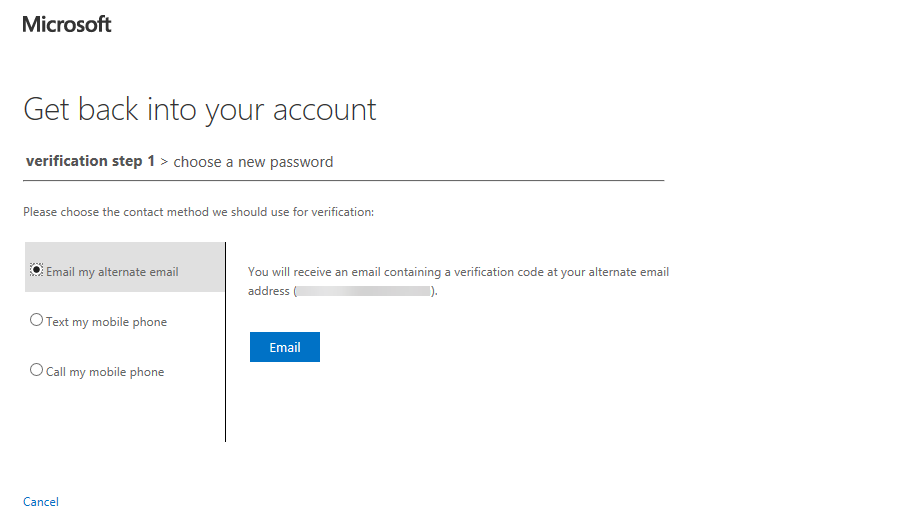
- On the verification step 1 screen, choose a verification method, such as Email my alternate email, and click Email.
- Check your email, and enter the verification code in the browser window. Click Next.
- On the choose a new password screen, enter and confirm a new password, and click Finish.
- On the Your password has been reset screen, click the link to sign in with the new password.
In this article, I showed you how to configure and test password reset policy for cloud-only users in Azure Active Directory.




