We all know what a virtual private (VPN) network connection is and why we use it, right? But aren’t we tired of the number of steps we have to go through each time we want to establish a VPN connection to a corporate back-end? Or are you tired of the number of help desk calls you get from traveling users, calling you because “the file server is down,” or “my application isn’t responding,” or “the intranet.company.local” website is not resolving? And the usual answer? “I’m sorry Mr. Helpdesk, you’re right! I forgot to start up my VPN connection. Now it’s all working again.”
If the above scenarios sound familiar, you’ll be thrilled to learn about auto-triggered VPN in Windows 8.1. As the name suggests, it’s a VPN connection that can be triggered automatically. It can be configured to auto-connect when starting a certain application (for instance, Remote Desktop or your accounting application) that can be both Store Apps and traditional Windows applications. They can also connect to a specific DNS-zone (eg. Intranet.company.local), which is actually pretty cool.
Setting Up Auto-Triggered VPN
The only thing you need to know to make this magic work is some Powershell knowledge. The main cmdlets are:
- Add-VPNConnectionTriggerApplication
– when using it in combination with a specific application. The full cmdlet should look like this: Add-VpnConnectionTriggerDnsConfiguration [-Name] <string> –DnsSuffix <String> [-DnsIPAddress <string[]>] –PassThru
- Add-VPNConnectionTriggerDNSConfiguration
– when using it in combination with a specific DNS Zone. The full cmdlet should look like this: Set-VpnConnectionTriggerDnsConfiguration [-Name] <string> [–DnsSuffix <String>] [-DnsIPAddress <string[]>] [-DnsSuffixSearchList <string[]>] –PassThru
You can run these cmdlets on an individual basis per machine/per user, have them pushed by using Group Policy scripts, and even push VPN Profiles by using SCCM 2012 or Windows Intune.
How Auto-Triggered VPN Works
So that now you know about auto-triggered VPN and how you can configure it on your system(s), it’s about time to actually walk you through some examples.
As a prerequisite, I already preconfigured a VPN Profile on my PC, making sure that it actually works. Actually, I already had this VPN Profile on my Windows 8 machine and had been using it on a daily basis, after which I upgraded to Windows 8.1 and can reuse this same VPN Profile for auto-triggered VPN.
Example #1: Fire Up VPN When Starting RDP
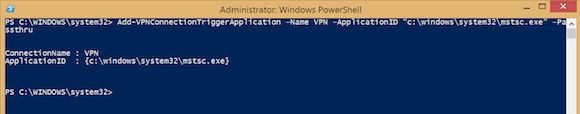
In this first example, I want to have my auto-triggered VPN being activated whenever I start mstsc.exe.
- Setup your dial-up VPN connection and make sure it is working fine
- Run the following Powershell cmdlet: Add-VPNConnectionTriggerApplication –Name <your VPN Profile Name> –ApplicationID “c:\windows\system32\mstsc.exe” –Passthru
- Verify the auto-triggered VPN profile settings by going to Networks and selecting your VPN profile. Select Let Apps automatically use this VPN Connection if it’s not already selected.
- From your Start Screen, start typing MSTSC.exe, which will bring up the Remote Desktop client.
- Select your networks in the toolbar, and your VPN profile will have a status of “Connecting” or “Connected” (depending on how quick you can select it!).
As you can see in my own example, the VPN connection to one of my customers will start whenever I launch mstsc.exe, even when connecting to another network. The reason I chose mstsc.exe is that I assume it is known by most users and easy to showcase my demo. To make it a bit more “network specific,” let’s go to the next example.
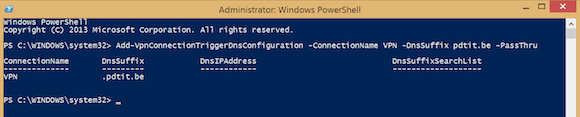
Example #2: Fire Up VPN When Connecting to a Specific DNS Namespace
In this second example, I want to make sure my VPN profile auto-trigger only works when I’m connecting to a specific DNS namespace. In a demo similar to the first example, let’s again imagine I need to perform a remote RDP connection to my customer’s backend. But this time I want the VPN connection established only when I connect to “server.externalcustomerdomain.com,” where it should be inactive when I connect to “server.externalcustomer2domain.com” or some other internal servers.
- Setup your dial-up VPN connection and make sure it is working fine.
- Run the following Powershell cmdlet: Add-VpnConnectionTriggerDnsConfiguration -ConnectionName VPN -DnsSuffix <your public DNS suffix> -PassThru
With this configuration, the VPN will be triggered whenever I connect to a resource having that namespace, irrelevant from what application I’m trying the connection. Think of a client/server application like a CRM or sales backend system, which relies on a network connection with the organization’s backend to pull data out of a database. Where the end user was required to first establish the VPN connection before, it is all happening automagically as of now.
Removing VPN-Triggered Connections
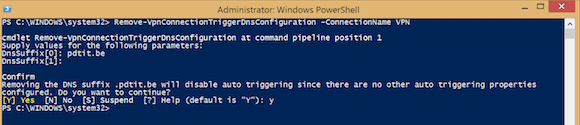
In this last section, I’ll show you how easy it is to remove your auto-triggered VPN connections.
As you could expect already, we have to go back to Powershell for this. But now we use Remove-VPNConnectiontrigger, as in the following example:
Remove-VpnConnectionTriggerDnsConfiguration -ConnectionName VPN
It will ask you for the DNSSuffix, followed by a final approval.
This completes my article on how to make use of the new Windows 8.1 feature, auto-triggered VPN. Being a technical consultant myself and heavily relying on VPN connections to connect to my customers, this saves me a lot of time and frustration – yes, when I’m stupid enough to forget to establish the VPN connection first before trying RDP.
Until next time!