Windows Image Deployment with FOG
Whether you have five or 5,000 PCs, managing your OS images is a crucial part of your IT infrastructure. Done well, an image management solution can free up your time and make your help desk (and by extension your users) blissful. Done poorly or not at all and you have entered the misty realms of error prone manual labor, tedium and late nights.
FOG (Which stands for Free, Open-source Ghost) can help clear the air surrounding your current image management system (or lack thereof).
Basic Components
FOG is a Linux based server application that uses TFTP, PXE and client MAC addresses as its core components. Once installed you don’t need to hack around in the Linux CLI to operate the software because it uses a handsome PHP based web interface.
FOG relies on the network’s DHCP service to supply clients with DHCP options 66 (TFTP) and 67 (PXE server). The FOG installation can act as the network’s DHCP server or you can use an existing DHCP server.
FOG tracks PCs entirely based on their MAC address. Hosts can be entered into FOG’s database manually in the GUI, via an imported CSV file or automatically via a client-side command given during the PXE boot process.
Server Installation
FOG can be installed easily on Fedora or Ubuntu based distributions in spite of it not being included in an official sources list. There are thorough instructions at the official Fog User Guide. There is also a listing of flash tutorial videos on FOG’s web site as well as YouTube videos on “csyperski’s” channel that will help you navigate the installation process among other topics. In fact, a great way to get started with installing FOG is to watch csyperski’s 11 minute YouTube video titled “Installing FOG on Ubuntu 8.10“.
But who is this “csyperski” person and why should you care about his YouTube videos? He is Chuck Syperski, chief developer of the FOG project and his YouTube channel is devoted to FOG instructional videos.
There are a few “gotchas” to look out for in the installation such as needing to change FOG’s config.php file if you choose a different MySQL password or changing the TFTP password if you use Fedora, but all of those are thoroughly documented in the easy to read User Guide. A standard installation should take less than 10 minutes to set up.
If you don’t want to bother with installing the package on your own, you can download the FOG virtual appliance which takes mere seconds to set up.
Supported Client Operating Systems
FOG can deploy both Windows and limited Linux images, however the project’s emphasis is on Windows deployment and management. The FOG user manual itself describes its support of Linux as “primitive”. As of this writing, the latest version of the FOG project is .28 which fully supports Windows 2000, XP, Vista, Widnows 7 and Server 2003.
The FOG Service
FOG shines in its support for Windows because of the FOG service which, when pre-installed in the deployed image, will allow you to manage many settings on your Windows PCs from within the FOG console. Some of those settings include the ability to automatically log out a user after a period of inactivity, create a shutdown/reboot schedule and even manage installed printers.
In the context of image deployment, the most important features that the FOG service offers is the ability to change the hostname of a machine after deployment as well as joining the machine to an Active Directory domain. As you can see, FOG goes beyond simple image management and can allow you to create a more well behaved and uniform fleet of PCs.
Using FOG
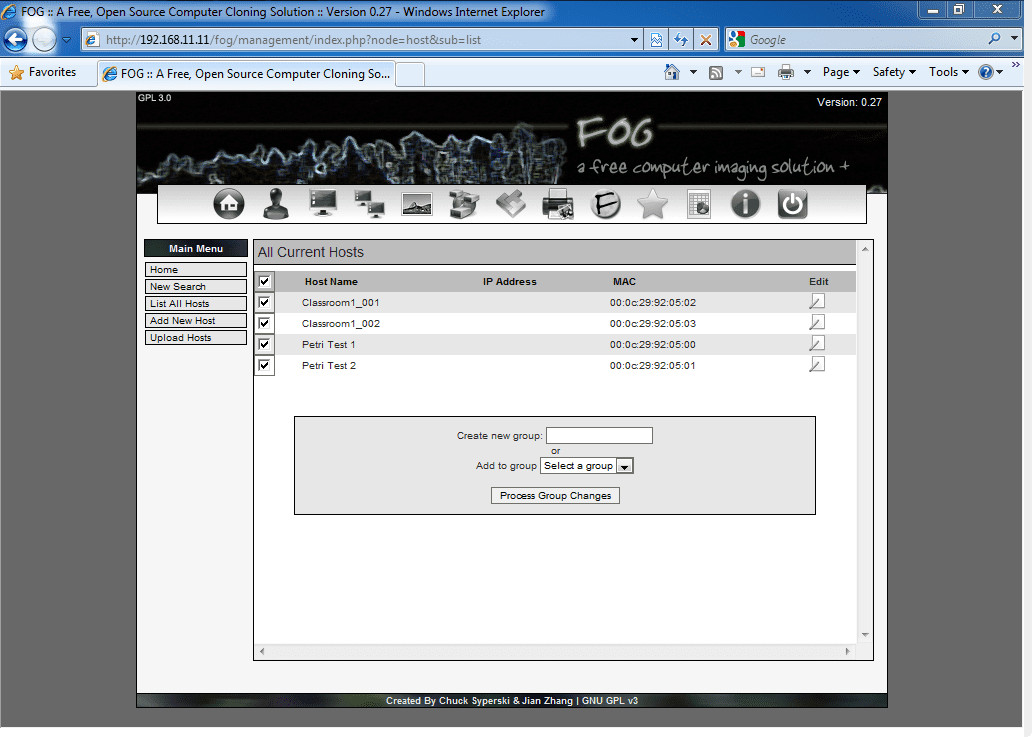
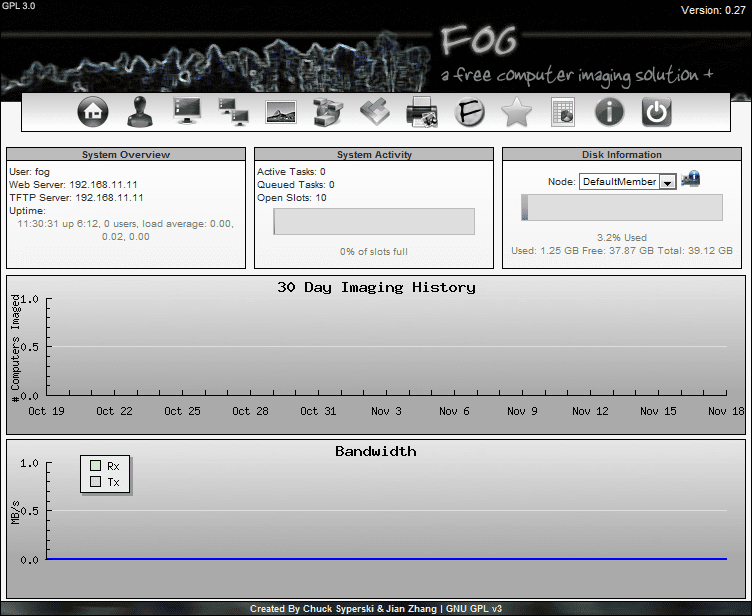
As mentioned previously, FOG is administered entirely through a web interface. After logging in you are greeted with a System Overview page that shows you usage statistics for the FOG system.
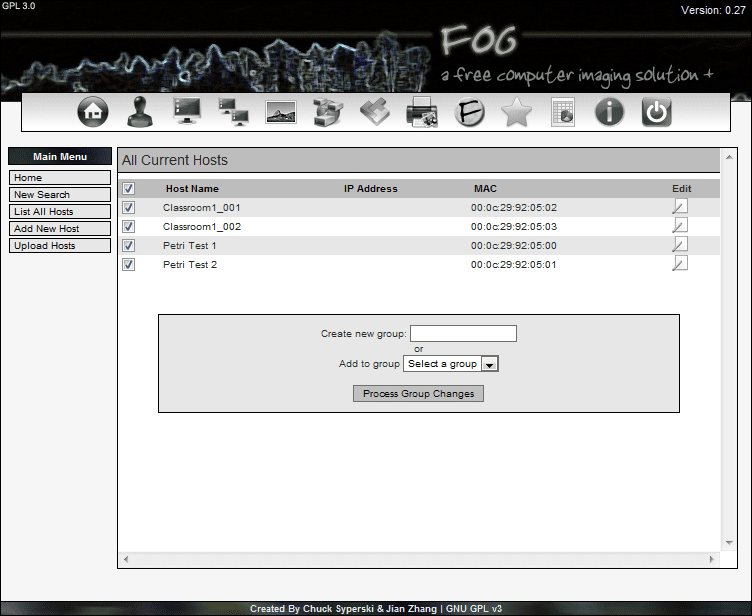
From the Host Management section, you can quickly view the hosts that the FOG server is aware of and create new hosts. The Group Management feature allows you to organize multiple hosts into logical groupings to make managing your deployment tasks easier.
The clever search feature finds existing hosts or groups based on any string within the host name and narrows the list down as you type the string. For instance the hosts “Petri Test 1” and “Petri Test 2” can be found by simply typing “tri”. In fact, by the time I typed the “r” , the two hosts had already been returned.
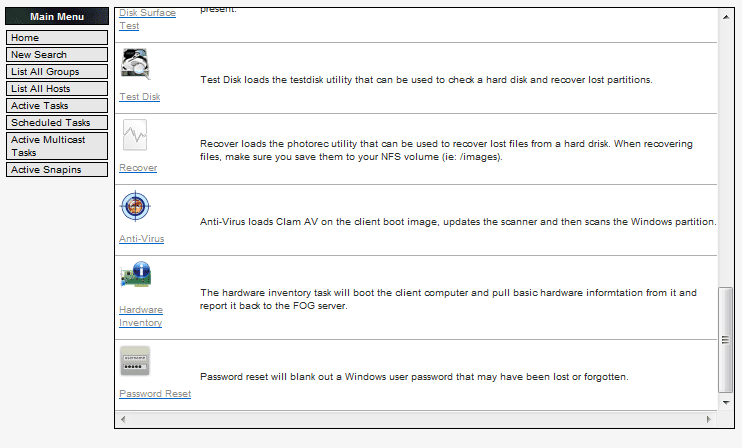
Individual PCs or groups of PCs can have more than just your standard corporate images pushed to them. Not only can destructive images be deployed, but also some predefined non-destructive boot images that include some very useful troubleshooting tools. Some of the most interesting deployment options that are included with a default FOG installation are:
- Sending WoL packets
- Sending a non-destructive Memtest86+ image to a PC or PCs on their next reboot
- Performing a variety of disk wipes such as a “lazy wipe” (zeros out the MBR) or a full wipe (several passes of random characters across the entire disk)
- Performing a variety of disk checks such as a surface check or the testdisk utility to check the disk or recover partitions
- The ability to send down a non-destructive boot image with the photorec utility installed in it to recover lost files
- The ability to send down a non-destructive boot image with Clam AV installed in it to perform an antivirus scan. This could be useful to extract a particularly stubborn infection that other scanners couldn’t remove due to certain files being actively used.
And there are even more unique images that can be pushed to a client under the “Advanced Actions” section.
Client Side Tasks
Client side tasks allow you to perform a few FOG tasks on the client PCs themselves. When a PC boots up from its PXE device, it will display the FOG PXE boot screen for three seconds. If no deployment task has been assigned to that host, the next boot device in line on the PC will be used. That three second pause during the FOG PXE banner screen gives you the ability to type client side commands. As of FOG version .28 the only three options are
- fog.memtest (calls down the memtest86+ boot image)
- fog.reg (Simple inventory of the PCs MAC address and limited hardware information with no input from the user)
- fog.reginput (Starts a complete hardware registration process and requires user input for things like the hostname, IP address, OS ID, etc.).
This could be quite handy if your handling a PC that is across the office (or campus!) from the FOG server and don’t feel like walking back to the server room to assign a hardware inventory task to a troubled PC.
Image Management
You can add images to FOG’s repository by adding your target machine’s MAC address to FOG and then applying an upload task to it from the FOG console. After you create the task within FOG and reboot the target machine, it will boot from FOGs capture image and send its hard drive image back to the storage server. Of course, typically Windows PCs will be sysprepped first.
Unfortunately, FOG cannot have image files manually added to its store. All images in FOG’s store must be collected via the “upload image” task. If you have a collection of images already (such as .ISO or .TIB files), you will have to apply the image to a hard drive, and then put the drive in a computer that you can PXE boot from and upload the image to the FOG server. This limitation is current as of FOG version .28 and may be addressed in future versions.
Images are assigned several “types” when they are created and captured. Types determine what is captured and how the image behaves when it is applied to a PC. The image types that are available are:
- Single Partition (Captures a single NTFS partition. The partition is re-sizable when it is applied to a PC. For example, a 500GB partition can be applied to a 40GB hard drive as long as the data on the 500GB partition is less than 40GB)
- Multiple Partition – Single Disk (All supported partitions on the first disk that FOG detects are imaged. However, FOG cannot re-size the partitions during a deployment.)
- Multiple Partition – All Disks (All supported partitions on all disks that FOG can access are imaged. FOG cannot re-size the partitions during a deployment.)
- Raw Image (A sector-by-sector copy of the hard drive will be taken which will create an exact duplicate of the disk. This creates very large files and will drastically increase the capture and deployment times. It might be useful for attempting a recovery of a corrupt drive, however.)
Deploying Images
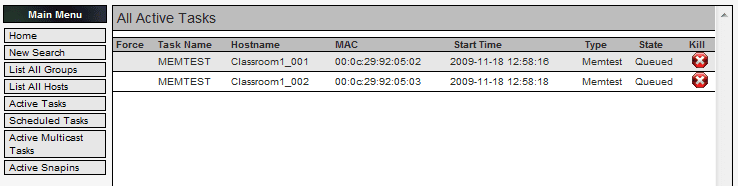
Deploying images is as simple as selecting an individual host or group within the FOG interface and assigning it a deployment task. You can view all current active tasks in the “Active Tasks” page. Tasks can be created to run once or on a cron-style schedule.
Storage servers are assigned queue lengths which determines how many simultaneous clients each server can deploy an image to. FOG can deploy images using multicast which can save deployment time and bandwidth when pushing an image to a group of computers. The ability to use multiple storage servers each with their own queue length can further reduce deployment time. For example, 3 storage servers with a queue length of 20 will be able to simultaneously service a total of 60 computers.
According to the FOG project’s own tests it only took 14 minutes for two servers with a queue size of 20 and 10 respectively to image a room full of 30 PCs. If you have more PCs than available queue slots (E.g. 60 client PCs but only two storage servers each with a queue length of 20 for a combined total of 40 simultaneous PCs you can image), the PCs that did not get a queue slot will sit patiently and wait for an available slot. The waiting PCs will display a status message indicating how many PCs are ahead of it and how long it has been waiting.
If you install the FOG service in your Windows images, you have the ability to create reboot schedules which could combine with the previous features to routinely schedule offline antivirus checks, memtests or wipe and reload entire classrooms full of computers every semester without so much as a single mouseclick.
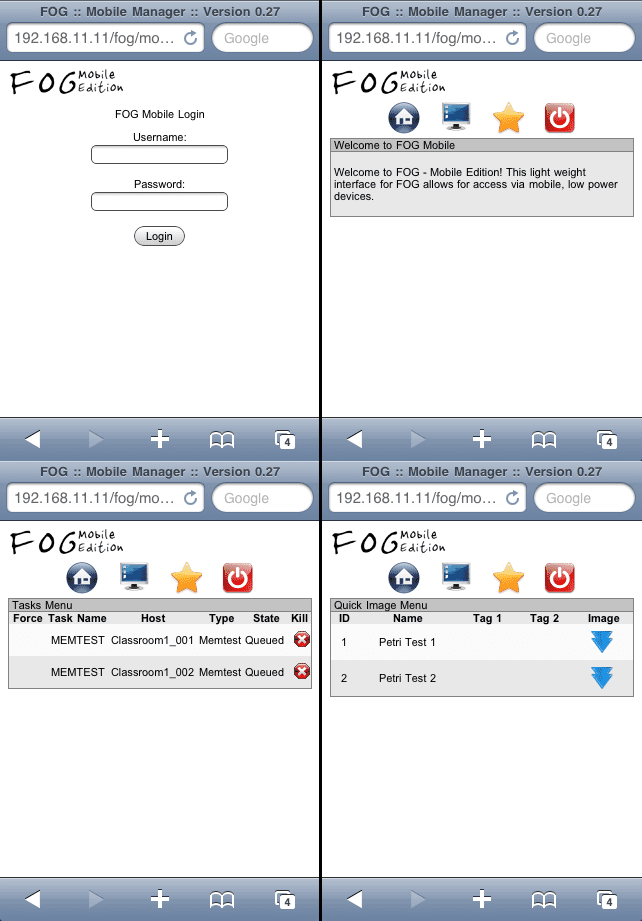
Mobile Interface
Yes, there is even a mobile version of the FOG web interface! Found at the URL http://[yourFOGserver]/FOG/mobile, The mobile FOG website has a very limited amount of tasks that can be performed. You can only search for hosts, image them and view/cancel active tasks. Of course, there’s nothing stopping you from using the full-featured FOG site on a mobile device, but the mobile site is nice and lightweight if it’s limitations are acceptable for your purposes.
FOG is a actively developed, open-source image management system that can save you time and money as you manage your fleet of PCs. FOG also goes beyond simple image management and becomes a troubleshooting tool that allows you to perform offline antivirus scans, memtest86 tests, attempt lost file recovery and more!
If there are features that you believe are lacking, don’t discount FOG yet. Features are constantly being added and if you have skills that could aid in development, you are certainly welcome to help out.
Give FOG a try in your environment and it just might cause the clouds of confusion surrounding your PC images to melt away.