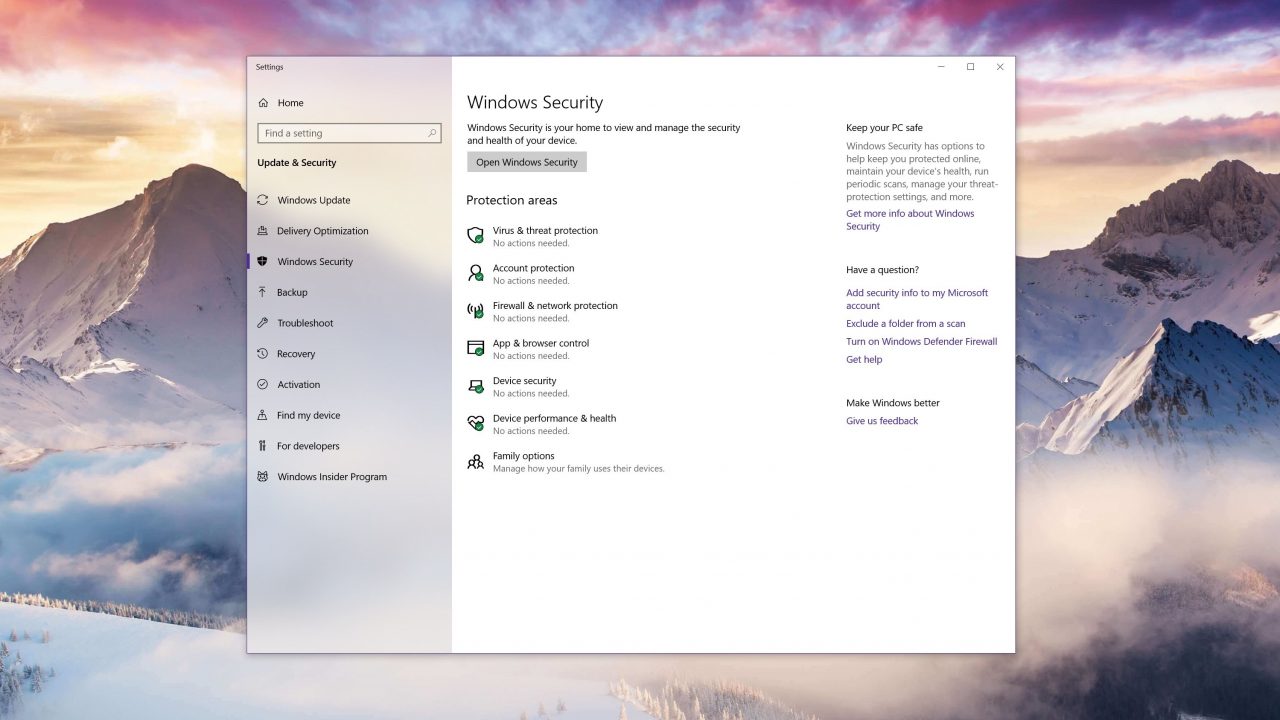
Windows Defender, the built-in antivirus protection for Windows 10, is receiving a significant update that will help make the tool more robust for detecting and protecting your device. Microsoft is making this transition for the product to further harden it from attacks and to improve its ability to handle increasingly complex malware.
Because the antivirus software has elevated system permissions, this makes it a bigger target for attack. If a malicious piece of software is able to compromise the antivirus platform, in theory, it could take over the impacted system; Microsoft is moving Defender to its own sandbox and is trialing this new feature today.
By moving Windows Defender to a sandboxed environment, if the application is compromised, the impact is minimal. Microsoft has a lengthy blog post, which you can read here, that describes in detail the update.
While this feature may not be revolutionary, it will significantly help Defender remain a secure application in even the most hostile of environments; think of it as a security blanket, for your security blanket.
Microsoft is currently enabling this functionality with Windows Insiders but if you want to force your install into a sandbox, you change the variable (setx /M MP_FORCE_USE_SANDBOX 1) and restart your machine. This functionality is supported on Windows 10 version 1703 and later.