Connect to Windows Azure Resources Using a VPN: Install Client and Root Certificates, Configure VPN
In part one of this two-part series, I showed you how to set up a point-to-site VPN in Windows Azure and create a self-signed root certificate to upload to Azure. A point-to-site VPN connection can be useful for connecting directly to Azure server resources from remote devices or in situations where a site-to-site IPsec VPN is not available, or isn’t possible to set up because the technical requirements cannot be met.
In part two, I’ll show you how to create a self-signed client certificate, how to install the root and client certificates, and finally, how to configure and test the VPN connection from your on-premise or remote client to Windows Azure.
Windows Azure VPN: Create a Client Self-Signed Certificate
Now we need to create a certificate for the VPN client machine. You should create a unique client certificate for each device that will connect to the Azure virtual network. The following makecert command should be run on the same machine where the root certificate was created.
- Open a command prompt in the directory where you want to save the client certificate. makecert.exe should be located in the same directory. To open a command prompt, right-click the directory folder while holding Shift, and select Open command window here from the menu.
- Type makecert.exe -n “CN=WINDC1Azure” -pe -sky exchange -m 96 -ss My -in “CONTOSO2” -is my -a sha1 and press Enter. In this example, I’m creating a client certificate for use from a DC called WINDC1Azure. You can replace the common name (CN) with anything that’s appropriate.
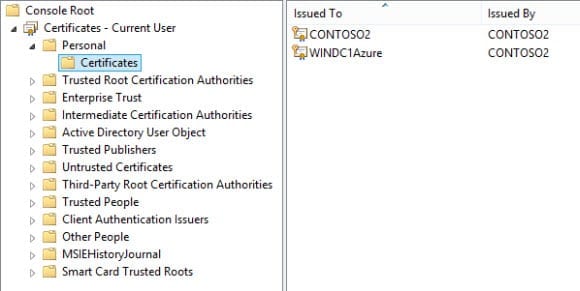
- Go back to the Certificates MMC we opened earlier.
- Under Certificates – Current User, Personal, right-click Certificates and select Refresh from the menu. The new client certificate will appear in the center pane.
- Right-click the certificate created by makecert in the center pane and select All Tasks, Export from the menu.
- In the Certificate Export Wizard, click Next on the welcome screen.
- On the Export Private Key screen, select Yes, export the private key and click Next.
- On the Export File Format screen, check Personal Information Exchange – PKCS #12 (.PFX) and click Next.
- On the Security screen, check Password.
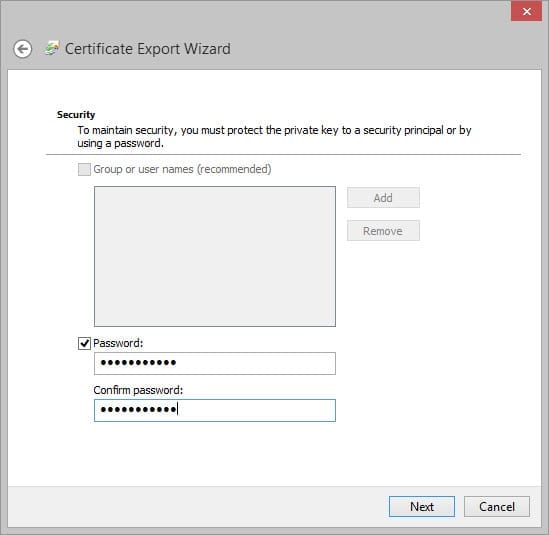
- Enter a password, and once more in the Confirm password box, and click Next.
- On the File to Export screen, click Browse and save the certificate to your working directory for makecert. Make sure the file has the .pfx file extension. Click Next to continue.
- Click Finish to complete the process.
Install the Root and Client Certificates
Now that we have both our root and client self-signed certificates, it’s time to upload the root certificate to the Azure management portal and install the client certificate on an on-premise server.
Upload the Root Certificate to Azure
Log on to the Azure management portal and follow the instructions below to upload the root certificate:
- In the Azure management portal, click Networks in the left pane.
- In the center pane under networks, click the virtual network you created earlier.
- Now click Certificates.
- Click Upload a Root Certificate.
- In the Upload Certificate dialog, click the folder icon under Certificate.
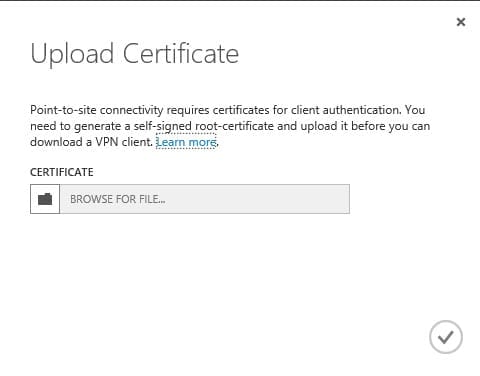
- Browse to the .cer file of the root certificate we created using makecert and click Open in the Choose File to Upload window.
- In the Upload Certificate dialog, click the tick icon to complete the procedure.
- Wait for a few moments while the certificate is uploaded to Azure.
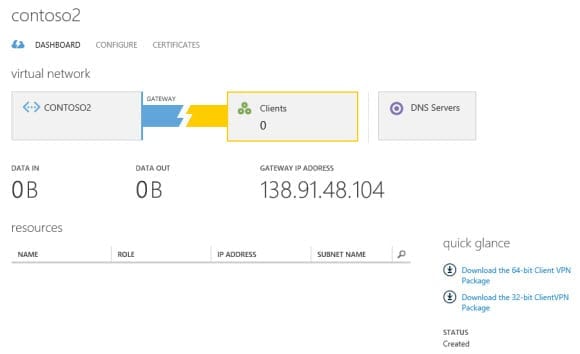
Now click Dashboard and note that the alert for the missing root certificate should have disappeared from the network diagram.
Install the Client Certificate on the On-Premise Server
Before installing the VPN client on the on premise server, we need to install the client certificate created using makecert.
- Log on to the server where you want to install the client certificate. Move the .pxf certificate file we exported in the previous steps and double click it.
- In the Certificate Import Wizard, select Current User as the Store Location, and click Next.
- Give consent or enter administrative credentials if prompted.
- On the File to Import screen, click Next.
- On the Private key protection screen, type the password for the private key and click Next.
- On the Certificate Store screen, check Automatically select the certificate store based on the type of certificate and click Next.
- Click Finish to complete the procedure.
Download and Install the Windows Azure VPN Client
Once the certificates are in place, we can download the VPN configuration package from the Azure management portal and run it on the on premise server.
- In the Azure management portal, click Networks in the left pane.
- In the center pane under networks, click the virtual network you created earlier.
- Now click Dashboard.
- Below quick glance, click Download the 64-bit Client VPN Package.
- After a few moments, Internet Explorer will prompt you to save the file. Save it to a convenient location on the server.
- Double-click the downloaded file and click Yes when prompted to confirm installation.
- Click the network icon in the bottom left of the desktop taskbar.
- You should see the VPN connection for your Azure virtual network in the list of networks. Click it and then click Connect.
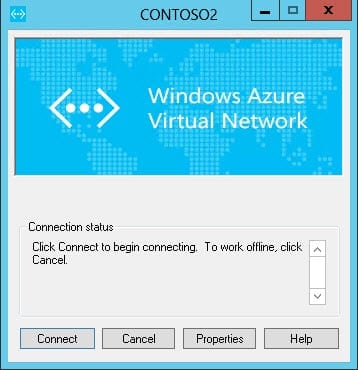
- In the Windows Azure Virtual Network pop-up dialog, click Connect.
- You will be prompted to confirm an update to the routing table. To perform the custom action, click Continue. Give consent or administrative credentials if prompted.
A secure connection to your Windows Azure virtual network should now be established.
Test your Secure Connection
Open a command prompt, type ipconfig /all, and you should see a PPP connection with the name of your Azure virtual network. It should have an IP address that corresponds to the range that we configured for point-to-site VPN clients in part one.
Let’s see if we can connect to a resource running on one of our Azure servers. To perform a simple test, I have set up Windows Server 2012 R2 in a virtual machine in Windows Azure and configured a file share that everyone has access to. If you are not sure how to configure a VM in Azure, see “Deploy Windows Server 2012 in an Azure Virtual Machine.” Additionally, you can find instructions on how to configure a file share using Server Manager in my article “Create a File Share in Windows Server 2012 R2 Using Server Manager.”
Once you have a server on Azure setup with a file share, open File Explorer on your on premise machine, where you established a VPN connection to Azure, and see if you can access the share using the Azure server’s IP address. For example, type \\10.0.0.4\ in the address bar of File Explorer, replacing 10.0.0.4 with the IP address of your remote server, and press Enter to see a list of available shares.


