In part one of this multi-part series, we took a look at downloading and installing VMware vSphere PowerCLI, the free PowerShell snapin for managing your VMware infrastructure. Now we need to do something with it. Today I’ll go through the steps of setting up and configuring PowerCLI.
(Need to catch up? Check out the rest of this series! In part three: use PowerCLI to start and shutdown VMs. In part four: PowerCLI and PSDrives, and in part five: created a new VM. Finally, in part six: use PowerCLI to manage your ISO files.)
Add Snapin to PowerShell
Before we can do anything we need to add the snapin to our PowerShell session.
PS C:\> add-pssnapin vmware.vimautomation.core
If you are ever in doubt about what version you are running, the snapin has a handy command.
PS C:\> get-powercliversion PowerCLI Version ---------------- VMware vSphere PowerCLI 5.1 Release 2 build 1012425 --------------- Snapin Versions --------------- VMWare AutoDeploy PowerCLI Component 5.1 build 768137 VMWare ImageBuilder PowerCLI Component 5.1 build 768137 VMware License PowerCLI Component 5.1 build 669840 VMware VDS PowerCLI Component 5.1 build 1012428 VMware vSphere PowerCLI Component 5.1 build 1012428
Now we are ready to manage our environment, but first we need to connect to a server.
PowerCLI: Connect to Server
The cmdlet we need is called Connect-VIServer. Take some time to look at full help and examples. The PowerCLI cmdlets also support online help so you can run a command like this:
PS C:\> help Connect-VIServer –online
To connect to a server you need to specify a name or IP address and you need to be authenticated (assuming your current credentials don’t suffice). You can use a saved PSCredential object and specify a username and password, or you can simply run the command and enter credentials when prompted.
PS C:\> connect-viserver 172.16.10.111
If you prefer a simple one-line approach, you can even enter the password as part of the command.
PS C:\> connect-viserver 172.16.10.111 -user root -Password P@ssw0rd
I’m going to connect with a previously created credential object.
PS C:\> connect-viserver 172.16.10.111 -Credential $c
A feature you might want to take advantage of – assuming you need to specify credentials – is to securely keep them in the local credential store. When you logon use the –SaveCredentials parameter.
PS C:\> connect-viserver 172.16.10.111 -Credential $c –SaveCredentials
In the future, when you connect to the server all you need to do is specify the server name. Although Connect-VIServer has a cool parameter, -Menu, which will display a text list of recently connected servers.
PS C:\> connect-viserver -Menu Select a server from the list (by typing its number and pressing Enter): [1] esx.jdhitsolutions.local [2] 172.16.10.111 2 Name Port User ---- ---- ---- 172.16.10.111 443 root PS C:\>
Configure PowerCLI
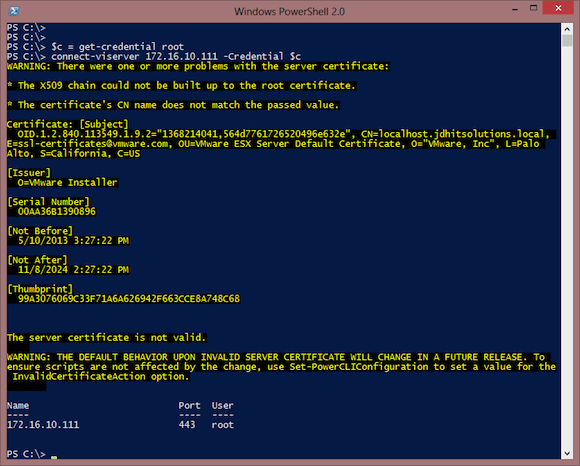
The first time you connect you might see a warning like you see below in Figure 1.
In my environment I’m not using any sort of certificates. But I don’t want to be bothered with the warning, so I’ll follow the suggestion and use the Set-PowerCLIConfiguration cmdlet.
PS C:\> Set-PowerCLIConfiguration -InvalidCertificateAction ignore
These are the possible values you can use:
- Unset – This is the default value and is essentially the same as Warn.
- Prompt – If the server certificate is not trusted the cmdlet will prompt you for a course of action before it continues.
- Fail – The cmdlet will not establish connection if the certificate is not valid.
- Ignore – The cmdlet will establish the connection without taking into account that the certificate is invalid or not.
- Warn – The cmdlet will display a warning saying that the certificate is not valid, the reason why it is not considered valid and then will print additional information about the certificate.
You can always run:
PS C:\> Get-PowerCLIConfiguration
To see the current configuration and change it any time.
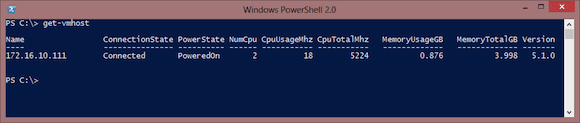
Now that we have that out of the way let’s see what servers we can work with using Get-VMHost.
PS C:\> Get-VMHost
In my case, I only have a single ESXi server but you might see more servers listed. You can also specify a host by name.
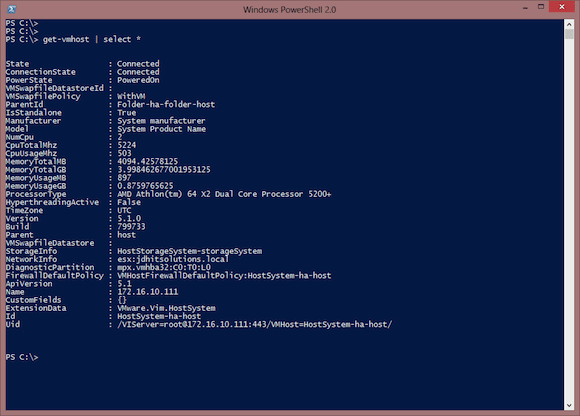
And as with most objects in PowerShell, there is more to the object than what you see here.
PS C:\> get-vmhost | select *
There are some settings you might want to configure, but we’ll cover those in a future article.
Disconnecting
As long as you are connected to the server you can perform all sorts of management magic, which I will be discussing later. If you close your PowerShell session you will automatically be disconnected. But you can also manually disconnect.
PS C:\> Disconnect-VIServer
This will disconnect you from the server you are currently connected to. You will be prompted for confirmation. If you prefer not to be bothered, set the confirm parameter to false.
PS C:\> Disconnect-VIServer -confirm:$false
I’ve covered several cmdlets for connecting to a VMware infrastructure server and configuring some basic PowerCLI settings. I didn’t cover every possible setting, and your environment may require additional steps. So take the time to read full help and examples for all the cmdlets I’ve demonstrated in this article. Next time we’ll look at some basic virtual machine management.