
In this post we will show you how to create a guest cluster on Windows Server 2012 (WS2012) R2 Hyper-V hosts using shared VHDX.
Using Shared VHDX: Prerequisites
There are some prerequisites for using shared VHDX.
- The VHDX file(s) that will be shared must be placed on either an SMB 3.0 share or a Cluster Shared Volume (CSV).
- The WS2012 R2 hosts that will run the virtual machines (that are using the Shared VHDX files) must be clustered.
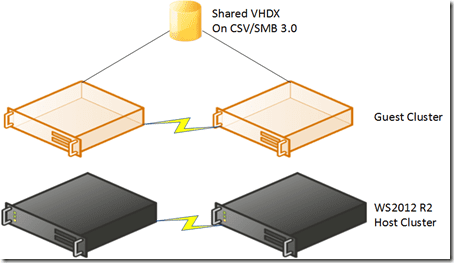
The clustered hosts that are running the virtual machines do not need to be in the same host cluster. That means a guest cluster can span multiple host clusters. A CSV cannot span clusters; therefore in this particular cross-host-cluster scenario, you must use SMB 3.0 shares to store the shared VHDX file(s).
You will need at least two shared VHDX files:
- A 1 GB VHDX file to use as the quorum or witness disk
- One or more data VHDX files to store the clustered data
Network the Virtual Machines
There are many ways to network the virtual machines using the concepts of converged networks. But to keep it simple, we will do the following.
- Assume that the hosts’ virtual switch is connected to a NIC team
- Create two virtual NICs in each VM that will be clustered. The first will be for management and client access, and the second will be used for cluster communications.
Install the guest OSes of the virtual machines, configure the computer names, patch them, join them to a domain (and the necessary reboot), and add the failover clustering feature in Server Manager. Configure the IP addresses of the two networks in each virtual machine:
- The management or client access IP address
- A cluster private network IP address
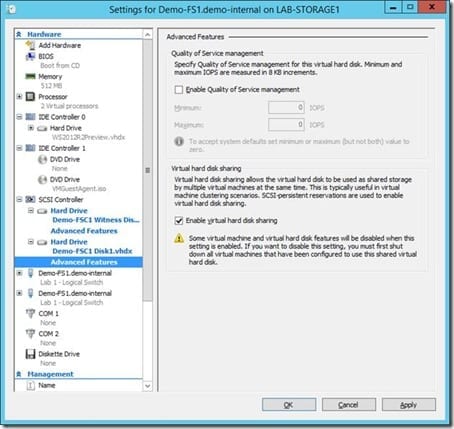
Add the VHDX files that are to be shared to the SCSI controllers of each of the guest cluster virtual machines. Then expand the properties of the VHDX files (as below) and check the box to Enable Virtual Hard Disk Sharing. You will get a warning on subsequent virtual machines that the VHDX has already been used by another virtual machine if you forget to check this box.
Log into one of the VMs and open Disk Management. Bring each shared VHDX online, initialize it (GPT is best) and format it. Be careful with your disk naming habits.
- Name the VHDX files after the cluster and the role to make it easy to tell what the files are for when managing hosts. For example, “GuestCluster1 Witness Disk” and “GuestCluster1 Data Disk 1.”
- Label the volumes using the same names. For example, “Witness Disk” and “Data Disk 1.”
- You should use those same names again to rename the disks when they are added to the cluster later on. For example, “Witness Disk” and “Data Disk 1.”
Create the Guest Cluster
Do the following to create the guest cluster.
- Launch Failover Cluster Manager and click the option to Create Cluster from the Actions pane on the right.
- Enter and add the names of the desired virtual machines in the Select Servers screen.
- You should perform the cluster validation to ensure that you have correctly configured your virtual machines, their networking and storage. Run all the tests and wait for the results. Fix any warnings or errors and repeat the validation test. A warning is a pass, but there may still be issues that cause availability problems.
- After a pass, choose to create the new cluster. In the Access Point For Administering The Cluster screen, enter the desired computer name and IP address for the new guest cluster. Both must be unused on the network.
- In the Confirmation screen, you can keep the box check to automatically add all available cluster storage. You might clear this if you will have lots of shared VHDX files and you want to gradually add them one by one. The cluster will be created for you after this.
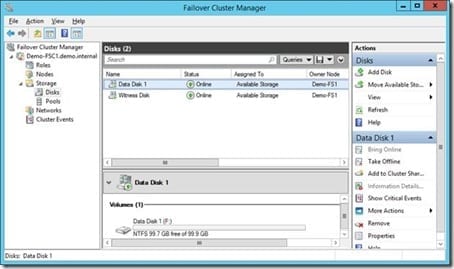
It is good practice to do the following once the cluster is operational.
- Double-check the quorum model.
- Rename (in Properties) each cluster disk to match the file name and volume label (as previously mentioned).
- Rename each cluster network (in Properties) to match the names of the network connections. For example, Management and Cluster.
- Don’t forget to install any recommended updates for failover clusters on your guest OS (use your favorite search engine to find the page on the TechNet Wiki).
Now your guest cluster is ready for you to install highly available services.


