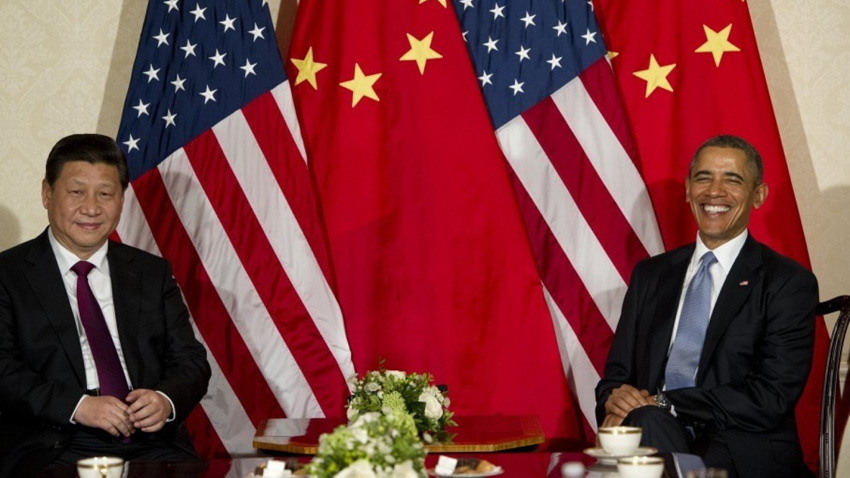
U.S president Barack Obama will meet with Xi Jinping, the President of the People’s Republic of China, in Washington D.C. today. And while the two presidents have much to discuss, given growing tensions between their two countries, a potential cyber-security agreement is top-of-mind.
According to various sources, the two had hoped to announce a dramatic if largely symbolic agreement on cyber-security, but those talks broke down ahead of Xi Jinping’s trip. So it’s more likely we’ll see a more general agreement to cooperate moving forward.
The need for a cyber-security accord is obvious, given the various probes and attacks that have become public over the past few years. Security experts believe that China has been secretly pinpointing weak points in the largely unprotected infrastructure of the United States. And it would take action to cripple this infrastructure in the event of a war or other military conflict.
(In this case, infrastructure refers to the U.S. power grid, banking systems, cellular networks, hospitals, and so on. Select commercial facilities, such as stadiums, convention centers, and museums are also considered covered by this term because they serve the public, not the government.)
The original accord wouldn’t have actually prevented such action, even on paper. As Admiral Michael Rogers, who heads up the U.S. Cyber Command said earlier this year, any US actions during wartime would “be in line with the broader set of norms that we’ve created over time. I don’t expect cyber to be any different.”
Instead, it was designed as an agreement by which both countries would pledge not to attack infrastructure during times of peace. This is a low bar, and more important, it is completely unenforceable.
Such an agreement would also not have prevented the Chinese and other bad actors from performing the numerous U.S. governmental and military hacks that have occurred over the past few years. National Intelligence director James R. Clapper Jr. said recently that such events are considered “intelligence collection” not “attacks.” Oh, and the United States does it too.
It also would not have covered the state-sponsored electronic theft of intellectual property, an area in which China is suspected to be a particularly egregious offender.
Given how little the now-diminished accord would have covered, one might naturally wonder why the U.S. and China were so eager to make it happen. Part of it is just related to current events, with both countries trying to downplay escalating incidents in the South China Sea, in particular. But the accord would have also been historic.
“It would be the first time that cyber is treated as a military capability that needs to be governed as nuclear, chemical and biological weapons are,” the Center for American Progress’ Vikram Singh told the New York Times.
For decades, the United States and the Soviet Union stared each other down in a Cold War that threatened to end with nuclear annihilation. Today, that threat remains, and various nuclear treaties between the two companies did little to stem the development of nuclear weapons. Still, the basic agreement that no nation would use nuclear weapons in a first strike sets what the Obama administration calls a “set of norms of behavior” that can and should be apply to cyber-security as well.
That agreement is unlikely to happen this week. But the door is open, and perhaps we can arrive at some common sense cyber-governance and less belligerent relations ahead of a more sweeping agreement.


