Apple, Google, Microsoft and other leading tech firms have joined a consortium of civil society organizations and security and policy experts in calling on US president Barack Obama to reject proposals to require US companies to offer encryption back doors in mobile devices and software. Such a move, the group says, would be insecure and wrong-headed, and lead to abuse, despite the obvious advantage for law enforcement.
“Introducing intentional vulnerabilities into secure products for the government’s use will make those products less secure against other attackers,” a letter to president Obama reads. “We urge you to reject any proposal that U.S. companies deliberately weaken the security of their products. We request that the White House instead focus on developing policies that will promote rather than undermine the wide adoption of strong encryption technology. Such policies will in turn help to promote and protect cybersecurity, economic growth, and human rights, both here and abroad.”
As the letter notes, various statements by administration officials have suggested that Obama should require American companies to not use encrypted products that don’t have a governmental back door, while others have even called on Congress to ban such products in the US.
“I don’t want a back door,” said US Navy admiral Michael Rogers, who serves as the Commander of the US Cyber Command, Director of the National Security Agency, and Chief of the Central Security Service. “I want a front door. And I want the front door to have multiple locks. Big locks.”
The group petitioning Obama disagrees strenuously with this stance, as the existence of multiple locks—or keys, in encryption parlance—would weaken security and make it possible for bad actors, not just law enforcement, to obtain supposedly protected data on mobile devices.
“Strong encryption is the cornerstone of the modern information economy’s security,” the letter explains. “Encryption protects billions of people every day against countless threats—be they street criminals trying to steal our phones and laptops, computer criminals trying to defraud us, corporate spies trying to obtain our companies’ most valuable trade secrets, repressive governments trying to stifle dissent, or foreign intelligence agencies trying to compromise our and our allies’ most sensitive national security secrets.”
In the wake of the Edward Snowden revelations about NSA spying capabilities, president Obama appointed a panel to review government surveillance programs. Three of the five members of that panel have signed the letter, which includes over 140 listed signatories.
The battle of encryption on mobile devices started last year when Apple announced that it would encrypt personal data on new iPhones by default. Google and Microsoft quickly announced that they would do so as well in subsequent releases of their mobile OSes. Microsoft’s version will be included in Windows 10 Mobile, which ships on new devices later this year.
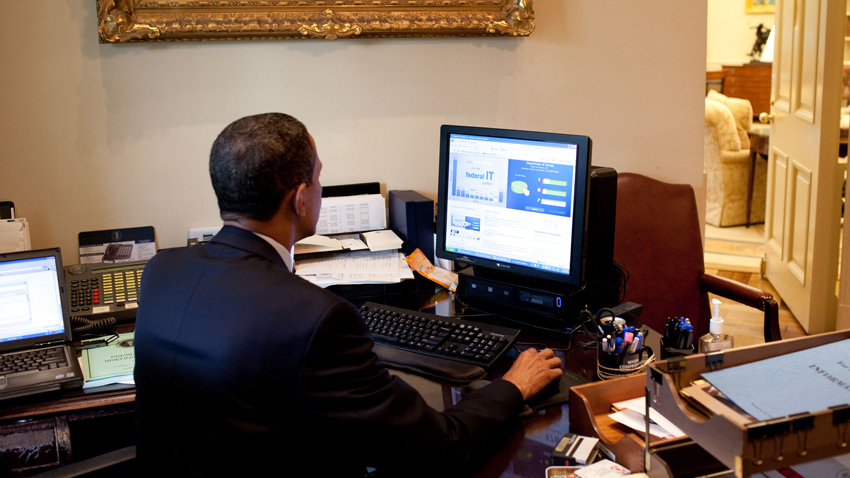
It’s not clear where president Obama stands on this issue, though he at least believes that encryption is necessary.
“There’s no scenario in which we don’t want really strong encryption,” the president said in February. “I lean probably further in the direction of strong encryption than some do inside of law enforcement. But I am sympathetic to law enforcement, because I know the kind of pressure they’re under to keep us safe. And it’s not as black and white as it’s sometimes portrayed.”
I agree with the consortium’s recommendation that president Obama follow the advice of his own Intelligence and Communications Technologies Review Group, which recommended in December 2013 that the US government should “fully support and not undermine efforts to create encryption standards; not in any way subvert, undermine, weaken, or make vulnerable generally available commercial software; and increase the use of encryption and urge US companies to do so, in order to better protect data in transit, at rest, in the cloud, and in other storage.” It’s the right thing to do.