One of the most confusing things to understand when learning about the switched part of network is the Spanning Tree Protocol (STP – 802.1D) and how it works to allow traffic to be efficiently forwarded through the switched network. This article will take a look at the STP path selection process, how a root switch is elected, how root and designated ports are assigned, and how each switch port is determined to be a root or a designated port as well as which ports will be forwarding or blocking.
STP Root Bridge / Root Switch Selection
The first question to really ask is: What is a root bridge? On an STP network, the root bridge (also known as a root switch) is intended to be the top of the forwarding pyramid, the forwarding decisions for the rest of the switched network depend on the location of the root bridge. The selection of the root bridge is determined by the bridge configured priority; by default this would be the switch with the lowest MAC address. It is important for anyone building a network using STP to ensure that the location of the root bridge is relatively central to the switched network so that forwarding decisions are made as efficiently as possible. This is possible because each switch can be configured with a lower bridge priority, which ensures it becomes the root switch.
Path Selection
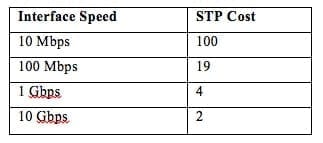
Once the root bridge has been selected (or elected), the formation of the forwarding tables can begin. One concept that must first be reviewed, however, is the idea of STP interface costs. Depending on the speed of the connected interfaces on the switches, they will be assigned a specific STP cost, these costs are then used to determine the total cost from the current switch to the root switch. Each of the switches throughout the network will send STP traffic between each other to determine this total path cost. Table 1 shows the common default STP interface costs that are used.
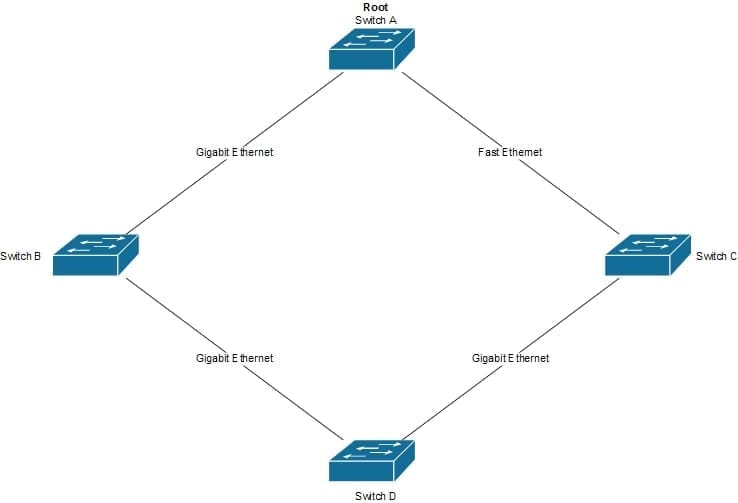
Now we’ll see how this is used to determine the optimal path. An example of this will be based on the topology shown below in Figure 1.
First, the switches will calculate the path cost to the root switch (in this example, the root switch is Switch A). Below are the path calculations per switch:
- Switch A – Cost = 0 (It is the root switch)
- Switch B – Cost = 4 (Through the B to A link)
- Switch C – Cost = 12 (Through the C to D, D to B, and B to A link)
- Switch D – Cost = 8 (Through the D to B and B to A link)
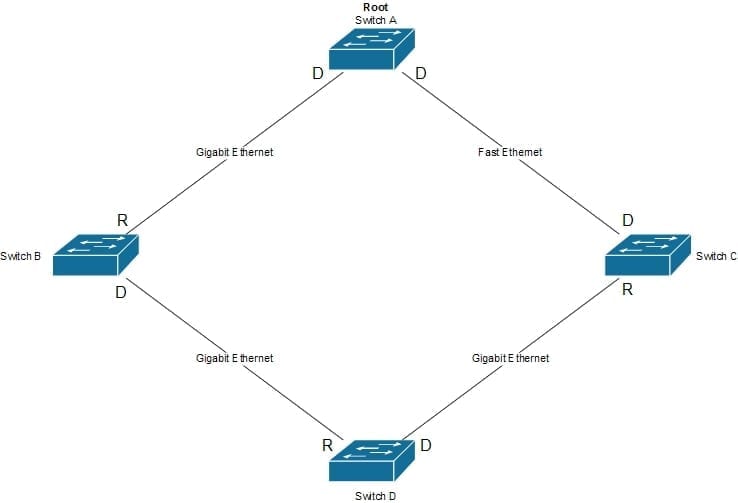
The outgoing ports towards the root switch with the least cost are marked as Root ports (The path taken to the root switch), all other ports are marked as Designated ports (Paths away from the root); these are shown in Figure 2.
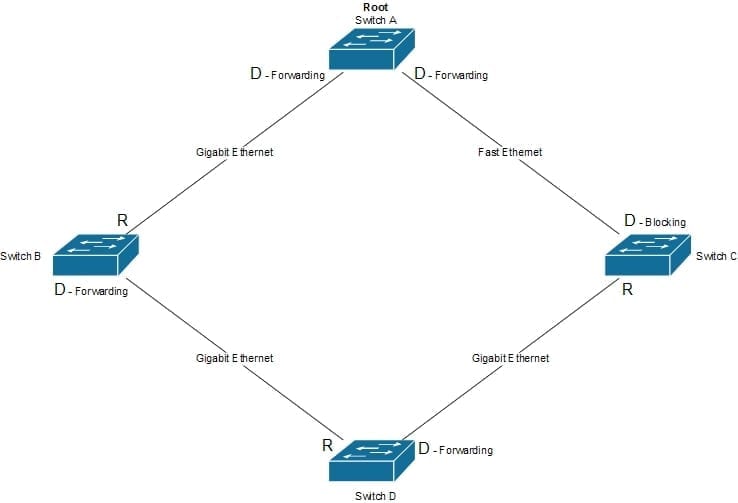
Since the main purpose of STP is to avoid switching loops, some work needs to be done for the link between Switch A and Switch C. With STP there can only be a single forwarding designated interface per segment. When more than one designated interface exists on a segment then one of the switches needs to put their interface into a blocking state; in this state STP traffic is still received but no user traffic is forwarded. The selection of which switch will begin blocking is determined by the switch with the least cost path to the root. In this case Switch A has the least cost path to the root (0) so Switch C will begin blocking its interface to this segment (some texts don’t call this a designated port but a non-designated port). This is shown below in Figure 3.
If something should happen to the connectivity between Switch A and the segment between Switch A and Switch C, then Switch C would begin forwarding on its interface.
For most Cisco switches this process is not done per STP instance (once per switch), but instead it is done per VLAN (once for each VLAN configured). What this means is that the forwarding path from a switch to the root could be different for each VLAN configured (with manual configuration intervention).
Since the article is written from the perspective of 802.1D and not the newer STP standards, it would be good to complete some further reading on how the newer 802.1w standards forward differently; however, this process is completed very similarly and all of the material discussed here should give a good base for this further research.