Spanning Tree Protocol: STP Port States
- Blog
- Networking
- Post
Overview
The Spanning Tree Protocol (STP) has long been a staple of Local Area Networks (LAN) in multiple environments. It is required in environments where multiple layer 2 paths exist between the various layer 2 devices within the LAN. Each of these ports that connect these devices together pass through a number of different states (Port states) that allow STP enough time to determine the status of the network and in what final state the port should be placed. This article takes a look at these port states, what happens during each of them, and why they are needed for STP operation.
What are STP Port States?
The main purpose of STP is to prevent switching loops throughout a LAN. The way it does this is by controlling the redundant links that connect into the same network segment. Each network segment is only allowed to have a single designated port that is used to forward traffic onto it. All other access points into the same segment are enabled, but in a blocking state that disallows traffic flow. If a failure should occur on the forwarding port, one of the blocking ports will be transitioned into forwarding state to continue to allow access to the network segment. This transition process includes a number of different states, including each of the states shown in Figure 1.
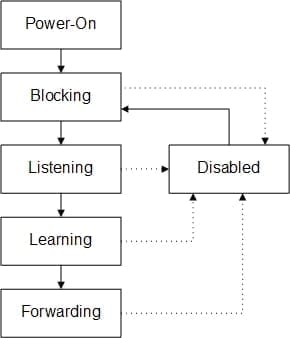
Figure 1 – STP Port States
What Happens During Each STP Port State?
Each port begins in a blocking state as the STP process tries to get a handle of the environment. If it is determined by STP that the specific port is ready to be transitioned into a forwarding state, it is transitioned first into a listening state. During the listening state, the device does nothing but listen to the STP traffic coming in from the other devices on the LAN; once the forward delay (15 seconds) timer expires, it transitions into the learning state. Once in the learning state, the device will start to build the MAC address table with the addresses seen on the port. The port does no forwarding of frames in this state; once the forward delay (15 seconds) timer expires, it transitions into the forwarding state. Once the port is in the forwarding state, it is fully operational and begins forwarding frames.
Advantages and Disadvantages of STP Port States
The major disadvantage of STP (802.1D) when used on modern networks, is that it can take a long time for a port to transition from a blocking state to a forwarding state, at least 30 seconds. This amount of time is simply too long on modern networks. While keeping the switched network from developing loops is more important than having no loop prevention mechanism, something needed to be developed to expedite this process. Initially, this was done via very careful modification of the STP timers (hello, forward delay and max age); this process was highly risky as the timers could change considerably, depending on the specific LAN characteristics. Other options included Cisco proprietary features like Uplink Fast, Backbone Fast and Port Fast; these too could be risky and required specific configuration knowledge and only Cisco equipment.
All of these issues were addressed with the introduction of the Rapid Spanning Tree Protocol (RSTP – 802.1w). This evolution of STP allows the transition process from blocking to forwarding to go from 30-50 seconds to 6 seconds (or less depending on timers). While the way that RSTP does this is outside the scope of this article, keep in mind that most modern switching environments utilize RSTP over STP for obvious reasons.
Summary
Some readers may ask, why cover a protocol that is no longer widely used? Generally speaking, while the original version of STP (802.1D) is not typically used, RSTP is an evolution of the STP protocol, not a completely different protocol. To understand the fundamentals of RSTP, the reader must understand what it is improving on. Hopefully the content of this article will enable the reader the ability to understand how STP port states work, so that future implementations of STP or RSTP can be understood.


