Sharing Files in the Cloud using Azure Files
In this Ask the Admin, I’ll show you how to work with Azure Files, a feature that’s enabled for all new Azure storage accounts, so that you can easily share files between virtual machines (VMs), or between VMs in the cloud and local devices on your on premise network.
This isn’t the first time I’ve written about Azure Files on the Petri IT Knowledgebase, a service that’s still in preview that unlike Azure blob storage, provides access to files using SMB file sharing. As I looked over the original article, Create and Configure a File Share using Azure Files, I was mulling over why I hadn’t used Azure Files in the year since the article was published, and I came to the conclusion that although I could have frequently benefited from transferring files using SMB, Azure Files is not only too difficult to set up each time, but it’s also too difficult to remember how to use it.
And the key reason is the need to use more than one tool to create and connect to file shares, and a lack of visibility into existing shares, which can only be viewed using the new Azure management portal, which I avoid because to be quite frank, it sucks badly.
When I say more than one tool is required, by that I mean in the original instructions I’d devised, it was necessary to search for the storage account’s primary key in the GUI to authorize the creation of shares or connect to them using SMB. So in this article, I’m going to show you how to do everything from start to finish in PowerShell, including generating a net use command to quickly map drives to Azure Files shares.
Create a New Azure Files Share
Before starting, I encourage you to read Create and Configure a File Share using Azure Files on the Petri IT Knowledgebase, as it contains all the background information you should understand about the Azure Files service. And for more information on setting up PowerShell tools for Azure, see Setup Windows Azure PowerShell Management on Petri.
If you don’t have a storage account that’s been created in the last year or so, you’ll need to create one before continuing:
New-AzureStorageAccount -StorageAccountName contosolab -Label ContosoLab -Location ‘West Europe’
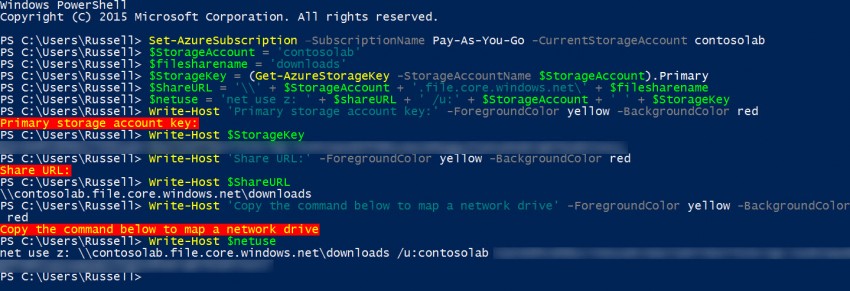
Now I’m going to set the Azure subscription and storage account that I want to work with:
Set-AzureSubscription –SubscriptionName Pay-As-You-Go -CurrentStorageAccount contosolab
To make the rest of the task a little easier, I’m going to define several variables, including the storage account name (contosolab) and the name of the share I want to create in the contosolab storage account (downloads). I’ll also create the URL that will be needed to connect to the SMB share, along with a net use command to quickly map a drive, if necessary. Finally, I’ll grab the primary key for the contosolab storage account using the Get-AzureStorageKey cmdlet:
$StorageAccount = 'contosolab' $filesharename = 'downloads' $StorageKey = (Get-AzureStorageKey -StorageAccountName $StorageAccount).Primary $ShareURL = '\\' + $StorageAccount + '.file.core.windows.net\' + $filesharename $netuse = 'net use z: ' + $shareURL + ' /u:' + $StorageAccount + ' ' + $StorageKey
All that’s required now is to establish the storage context using the storage account name and primary key, and then create a share using the New-AzureStorageShare cmdlet:
$ctx = New-AzureStorageContext -StorageAccountName $StorageAccount -StorageAccountKey $StorageKey $share = New-AzureStorageShare $filesharename -Context $ctx
Finally, I’ll write all the information I might need to work with the share to the console:
Write-Host 'Primary storage account key:' -ForegroundColor yellow -BackgroundColor red Write-Host $StorageKey Write-Host 'Share URL:' -ForegroundColor yellow -BackgroundColor red Write-Host $ShareURL Write-Host 'Copy the command below to map a network drive' -ForegroundColor yellow -BackgroundColor red Write-Host $netuse
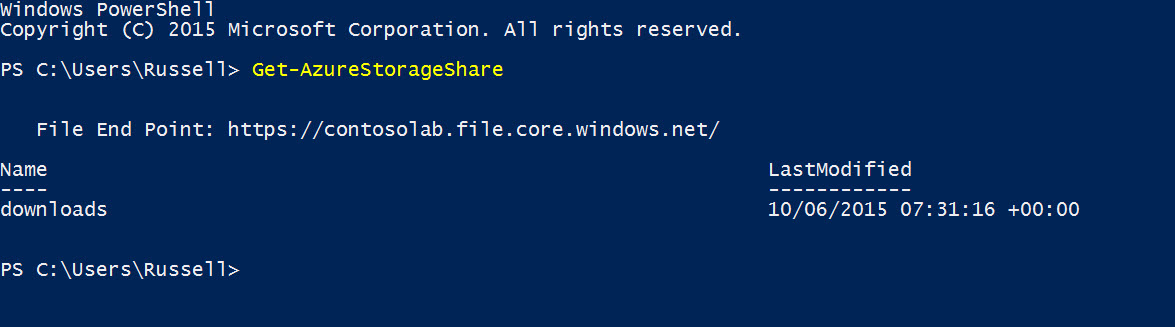
Enumerate Existing Shares
If you come back to the storage account after some time, you might be forgiven for forgetting the names of any configured shares. This is where the Get-AzureStorageShare cmdlet comes to the rescue, listing all the shares configured for the current storage account.