Protect Users Against Malicious Websites Using Windows 10 Application Guard
In today’s Ask the Admin, I’ll show you how Windows Defender Application Guard can protect enterprise users against malicious websites.
Windows Defender Application Guard (WDAG) uses Hyper-V containers to virtualize Edge browser sessions, helping to protect the operating system in the case of a browser security breach. WDAG is currently only available to customers with Windows 10 Enterprise and Education licenses. But Microsoft has promised to make WDAG available to Windows 10 Professional customers in the spring 2018 update.
WDAG requires a device with a 64-bit CPU, Second Level Address Translation (SLAT), and VT-x (Intel) or AMD-V. And because of the performance overhead of WDAG, Microsoft recommends 8GB of RAM, although it will work with less. Another recommendation is VT-d (IOMMU) support, which is a hardware virtualization technology designed to isolate and restrict device access to the owner of the managing partition. If your hardware supports VT-d, you’ll probably need to manually enable it in the BIOS. Most modern hardware should support the basic system requirements for WDAG.
WDAG has two operational modes: standalone and enterprise-managed. In standalone mode, users can start Edge in Application Guard and browse untrusted sites. Enterprise-managed mode uses a list of sites, defined in policy, that when opened force Edge to run in Application Guard.
Install Windows Defender Application Guard
Both modes require that WDAG is installed on the device. The easiest way to do that is in PowerShell. The following command should be run in a PowerShell prompt with local administrator privileges:
Enable-WindowsOptionalFeature -online -FeatureName Windows-Defender-ApplicationGuard
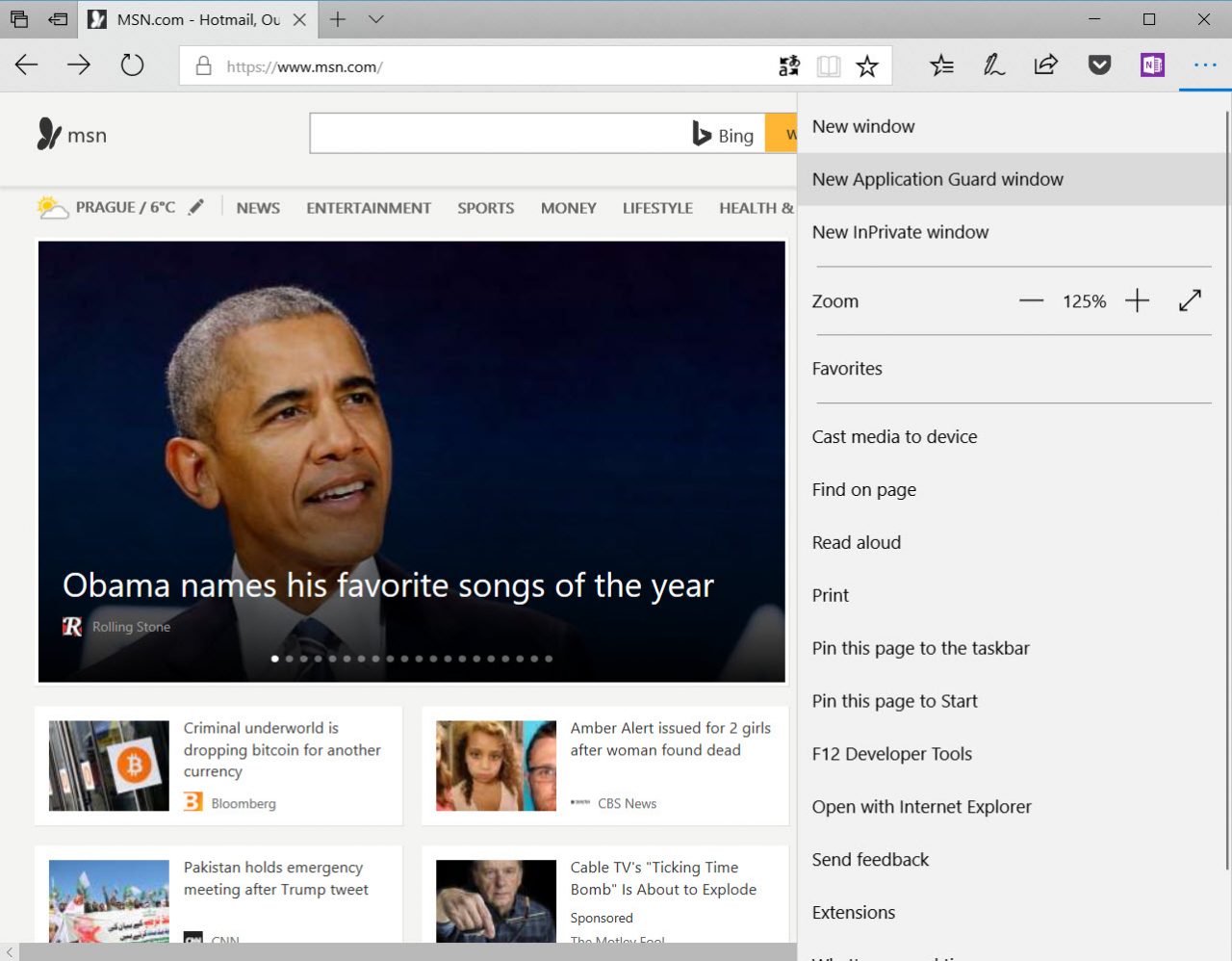
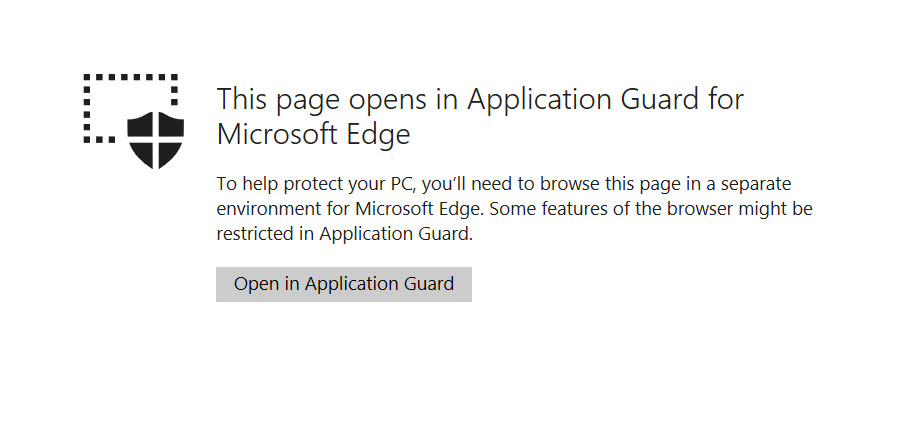
You’ll need to restart the computer to complete the installation. Once you’ve restarted the device, open Edge and there will be an option in the menu to open a New Application Guard window. When you open a new Application Guard window for the first time, you’ll see a splash screen saying that WDAG will take a few minutes to prepare.
When it’s done, Edge will open a second window that you can identify in the taskbar by the small shield icon. This version of Edge is running in a Hyper-V container, protecting the operating system and other applications, including non-WDAG Edge, from sites that manage to compromise the browser in Application Guard. It’s worth noting that users can open more than one isolated window, helping to protect one set of sites from another.
Enterprise-Managed Mode
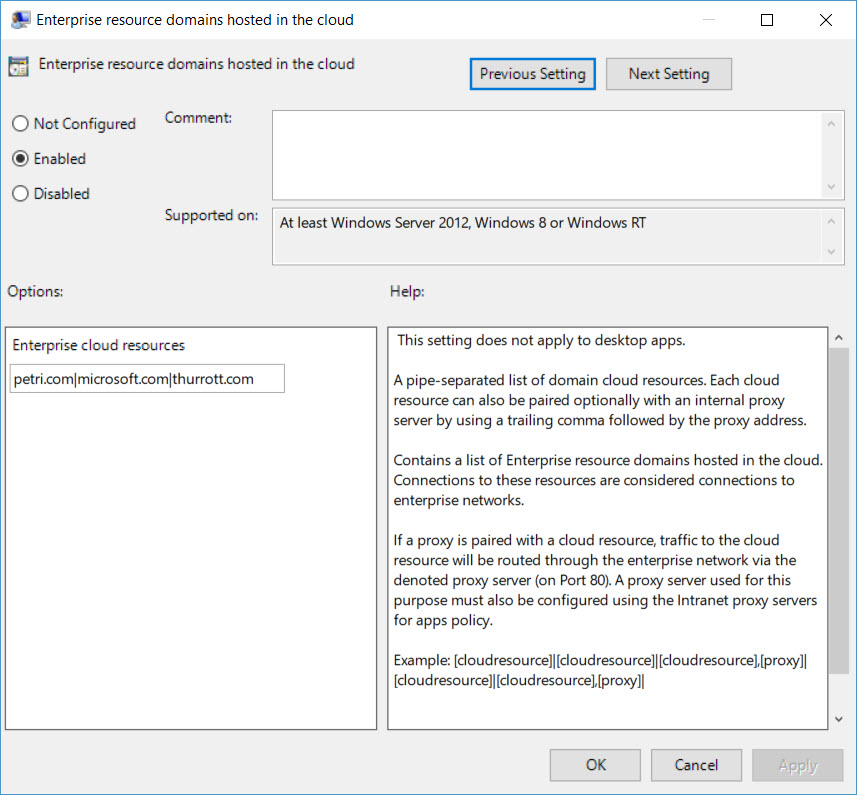
Enterprise-managed mode can be set up using Group Policy or Mobile Device Management (MDM) policies. In Group Policy, you should define enterprise-trusted sites in the Enterprise resource domains hosted in the cloud setting under Administrative Templates > Network > Network Isolation. Domains should be listed as a pipe-separated list: petri.com|microsoft.com|thurrott.com. These domains will be opened in Edge and not in an Application Guard window.

To complete the process, enable Turn on Windows Defender Application Guard in Enterprise Mode under Administrative Templates > Windows Components > Windows Defender Application Guard. There are also several other settings that allow you to configure WDAG behavior, such as data persistence and whether users can use the clipboard in Application Guard sessions. For more detailed information about each setting, see Microsoft’s website here.
Should You Enable Application Guard?
In practice the Application Guard end-user experience is a little clunky. Sometimes it takes a few seconds for Application Guard sessions to start and performance is slower than vanilla Edge, although nothing that most users would complain about. Internet Explorer also supports Application Guard. If a site should be opened in Application Guard because it has been flagged in policy, Internet Explorer will open the site in Edge.
I couldn’t connect to public WIFI hotspots with Application Guard enabled. That wouldn’t be an issue in standalone mode but in enterprise-managed mode that’s going to be a problem for notebook users. As is often the case, getting the enterprise-managed Group Policy settings to ‘take’ was an issue, so I don’t have much confidence that settings would be properly enforced.
Google recently announced an experimental feature in Chrome that guarantees sites run in their own process to block cross-site scripting attacks. While Google’s site isolation doesn’t protect the operating system if the render process is compromised, defenses like those provided by WDAG for Edge are promised in a future Chrome update.
At this time, I can only recommend that you look at educating users how to work with Application Guard in standalone mode. The hardware-based virtualization behind WDAG would likely protect the OS and other running apps if the containerized browser was completely compromised. So, if your users have a habit of visiting parts of the web that they really ought to avoid, giving them the option to use Application Guard could help prevent security breaches.



