Is PRISM Damaging Cloud Computing?
“No, sir. It does not. Not wittingly. There are cases where they could inadvertently perhaps collect, but not wittingly.”
– U.S. Director of National Intelligence James Clapper, when asked during a March 12, 2013, Senate hearing about spying on U.S. citizens.
In June 2013, the Guardian broke the news about a program called PRISM that is run by the United States National Security Agency (NSA) to spy on Internet users with the alleged cooperation of the tech giants in cloud computing. Surely this intrusion on privacy infringes on privacy, company security, and the competitiveness of American-owned cloud computing companies?
PRISM and Providers
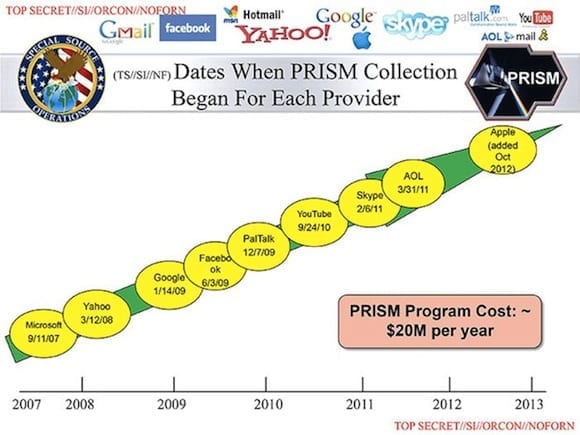
In June and July, former analyst – and now tourist-on-the-run whistle blower – Edward Snowden leaked a set of slides and shared knowledge of the NSA’s spying program with the Guardian. The leaked slide deck in question stated that the NSA had direct access to the servers owned by the following companies:
- Microsoft
- Yahoo
- PalTalk
- YouTube
- Skype
- AOL
- Apple
When asked by the media, companies such as Microsoft and Google refuted claims that they provide the NSA with direct access to their servers. You’ll notice in the original slide (shown above) that it refers to when data “collection” started, not when they obtained access. That is a subtle difference.
The Real Source of Power
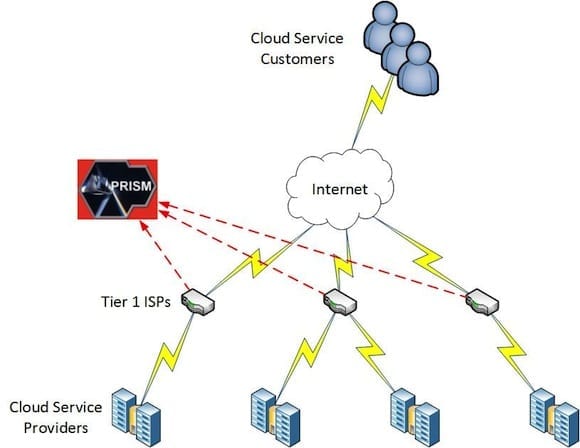
On the Security Now podcast (episode 408), security expert Steve Gibson (Gibson Research Corporation) proposed a theory backed by many other people. He has suggested that the leaked NSA slide deck misuses the term “server.” Just as many non-technical people misuse the word, in this case, Gibson argued, a “server” was used to describe anything behind the black curtain of the Internet. Gibson reminded us that the real power of the Internet isn’t the servers – it’s the routers that provide the interconnectivity, and these are the sweet spots for those who want to spy.
Service providers such as Microsoft and Amazon have vociferously protested against any intrusion by U.S. government agencies that can harm their international competitiveness in cloud computing. Therefore, Gibson’s theory makes sense: He believes that the NSA has actually spliced the network connections of the tier 1 Internet service providers (ISPs). This is where all data must flow, and this is where all the service provider and tier 2 ISPs are interconnected.
With relatively little amount of pressure or legal/legislative action, the NSA PRISM program could tap into almost every conversation on the Internet.
Prior to this scandal we were wondering why the NSA was building a data center in Utah that will be capable of storing 5 zetabytes of data. That is over 5 billion terabytes of information! Every time you tweet, every time you Skype, every embarrassing Facebook photo post – it’s all captured and stored for trend analysis and historic reference by the NSA.
Disclosing Data Without Your Consent
What does this mean to cloud computing? The emergence of the public cloud created a lot of hype from marketing people, and exciting opportunities for IT architects and solutions designers. Amidst all the noise, a few quietly voiced their concerns. Previous legislation by the U.S. government and programs by US security services have caused great discussion about the suitability of U.S.-owned services. The Patriot Act gives security services almost unfettered on-demand (rather than a regular copy) access to data stored in US-owned data centers, no matter where those data centers are located.
On June 23, 2013, ZDNet reporter Zack Whittaker wrote on the impact of the Patriot Act on non-USA residents who were using US-owned cloud services. In the article, Whittaker points out a recent Microsoft whitepaper, “How We Use Your Data,” in which the company states, “Microsoft may need to disclose data without your prior consent.”
Google also confirmed compliance with the Patriot Act in the European Union. In my own experience, Amazon was quite evasive, and dare I say dishonest, on the subject of compliance with the Patriot Act. All of this encroachment on privacy by the U.S. government does not help U.S. companies like Amazon, Google, or Microsoft that are trying to compete in a global cloud computing market. They have invested billions in building globally located data centers and marketing their services to the world, only to be handcuffed by U.S. legislation and secret siphoning of data.
“If you’re doing nothing wrong, you have nothing to hide”
Now we in Europe wonder if Safe Harbour is a treaty without meaning. There are even those who are debating if those companies that have complied with the NSA’s alleged demands may face lawsuits in the European Union for breaching local data protection laws. The PRISM scandal has confirmed every fear of the tinfoil hat-wearing brigade: that the U.S. government will do whatever it can to gain access to data. This isn’t just a fear about personal monitoring; the original drafts of the bipartisan Cybersecurity Act were scandalous:
“The Secretary of Commerce— shall have access to all relevant data concerning (critical infrastructure) networks without regard to any provision of law, regulation, rule, or policy restricting such access…”
Is the PRISM activity illegal? Apparently not, though there is an argument that PRISM contravenes the Fourth Amendment to the U.S. Constitution (entailing no search and seizure of citizens without a warrant– something that is common in most democracies). It appears that the only crime in this entire scandal is the alleged perjury by Director James Clapper when asked during a Senate Hearing of the US intelligence services were spying on US citizens.
“If you’re doing nothing wrong, you have nothing to hide from the giant surveillance apparatus the government’s been hiding.” – Stephen Colbert (@StephenAtHome)
PRISM is just the latest in the data-gathering scandal. It is also reported that the NSA is gathering call-log information on every phone call made in the United States. This information is useful, they say, because it allows them to perform trend analysis. Once they associate a phone with you, they know where you travel (your phone frequently pings a cell tower), who you are talking to, and for how long. You can change your phone, but analysis can re-identify you once you begin your routine again.
“Power tends to corrupt, and absolute power corrupts absolutely. Great men are almost always bad men.” – John Emerich Edward Dalberg Acton
Post-9/11 Americans have been molded into believing that necessary sacrifices must be made to defend against terrorism, including those very freedoms and rights that are being attacked. Americans are pretty evenly divided by the NSA scandal, with many believing that either you don’t need secrets if you have nothing to hide, or this government-sanctioned spying will stop terrorism.
The latter is questionable. The former is dangerous. We have plenty of evidence to show how total information = total power and total power = total corruption. Those with access to this data have easy temptation to misuse it. You may think that data access is controlled under court order. Not so, according to Snowden, who said that analysts would routinely tap into people without supervision. Human nature is to corrupt.
Maybe this all seems like a part of a far-fetched movie plot? Unfortunately, there are concerns with this unfettered access. Just ask certain U.S. political organizations about their recent IRS audits. If presidential spying on a couple of journalists in the 1970s was enough to cause impeachment, then surely unwarranted, if questionably legal, spying on an entire nation is enough to cause concern? And even if this dragnet spying doesn’t anger you, surely the placement of a data center in a hot desert in Utah should cause some anger when the private sector is deliberately picking temperate locations to reduce air conditioning costs?
Echelon, Tempora, and the “Federal Trojan”
Is the scandal causing issues for American-owned cloud computing now? Interest in services such as Office 365 continues to grow. Sales are rising. There are rumblings of legal action, but I don’t think it will lead to anything. That’s because nations outside of the U.S. spy on their own citizens just as much as the NSA does, if not more (and no, I am not talking about North Korea). Citizens of the UK are the most spied-upon people in the world. It is nearly impossible to walk a square foot of London without being watched and recorded by CCTV cameras. Government Communication Headquarters (GCHQ, the UK colleague of the NSA) has participated in a program called Echelon for decades (along with nations such as Australia, New Zealand, Canada, and the United States). Echeleon was rumored to be quite similar to PRISM, tapping into Internet connections that passed through UK territory to gather data.
Since the PRISM scandal broke, it was reported that GCHQ has been operating a surveillance program called Tempora that is even bigger than PRISM, gathering 20 petabytes of data a day from 46 transatlantic cables for the last 18 months. Germany, where data protection is considered sacrosanct, has reacted angrily. This is pretty laughable since they have been said to operate state-sponsored spyware that is referred to as the Bundestrojaner, or “Federal Trojan.” Although it is said to be court controlled, such malware can be missed by investigators. These scandals are just a tip of the iceberg. It is conceivable that the police and intelligence services of every state do this sort of spying or want to do it.
A Safe Middle Ground
I am upset at the level of spying that is being done, both in the United States by the NSA and elsewhere. I object to censorship and warrant-free dragnet data tapping. I’m not one of those people who sleeps in a Faraday cage or who tracks satellite movement. I’m an ordinary citizen that believes in democracy and oversight. I acknowledge the need for policing and security, but I recognize the weaknesses of human nature. Those who become accustomed to access or power become numb to the privileges that they have and the rights of others. They can reason anything and misuse legislation to create situations that benefit them.
I believe that companies such as Microsoft, Amazon, and Google understand this. They obviously want a world where cloud computing is able to operate without spying. These companies have a responsibility to cooperate with local police and intelligence services when warrants are served to facilitate genuine criminal or terrorism investigations. I know this is already done – I worked for a hosting company when police required access to data and all possible cooperation was given. There is a safe middle ground.
Warrantless searching was made illegal by the Fourth Amendment for a reason. Secrecy is necessary, but oversight is even more important. When a program requires secrecy and lies, then one must wonder why the program exists and what rights it infringes upon. Companies such as Google and Microsoft have spoken out as much as they are allowed to (yes, they are gagged on how much they can reveal). I believe these companies are acting as responsibly as they can. Should the scandal affect cloud computing? Yes. Has it? No.
Clarification: I work for a Microsoft cloud distributor in Ireland, I am a customer of Office 365, and I use social media services from Facebook, Twitter, and Google. And I don’t own a tinfoil hat.