Microsoft Pulls Faulty Windows Patches
Just a few days after the release of the August “Patch Tuesday” patches via Windows Update, Microsoft has withdrawn several of the updates that caused 0x5 stop errors (aka “blue screen of death”), affecting every version of Windows since Vista.
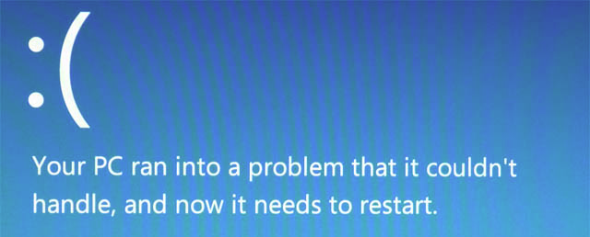
A “Blue Screen of Death” on Windows 8 or Windows Server 2012. (Image: Aidan Finn)
The Problem: “Blue Screen of Death” After Patch Tuesday
Microsoft reports the problem in the Known Issues section of the update description in KB2982791 (aka MS14-045). Known Issue 3 is:
“Microsoft is investigating behavior in which systems may crash with a 0x50 Stop error message (bugcheck) after any of the following updates are installed.”
The affected updates and operating systems are:
- 2982791: MS14-045 – Description of the security update for kernel-mode drivers: August 12, 2014. This affects every version of Windows for PCs, RT, and Server since Windows Vista.
- 2970228: Update to support the new currency symbol for the Russian ruble in Windows. Every version of Windows for PCs, RT, and Server are affected since Windows 7.
- 2975719: August 2014 update rollup for Windows RT 8.1, Windows 8.1, and Windows Server 2012 R2
- 2975331: August 2014 update rollup for Windows RT, Windows 8, and Windows Server 2012
Microsoft goes on to say that:
“This condition may be persistent and may prevent the system from starting correctly.”
Microsoft has disabled downloads of these updates until the issue is resolved. In the meantime, if you have installed these updates and are experiencing the issue, I’m sorry to say that the fix is not pretty.
Does Microsoft have a quality control problem?
I’m one of a number of Microsoft MVPs that have been critical of updates coming out of the Microsoft Server & Tools — now Cloud and Enterprise — group for several years. Initially we privately expressed our displeasure with Microsoft. Then last year, the predictable failures caused by poorly tested update rollups (or whatever Windows and System Center decide to call them that week) caused us to take our criticism public, whereupon the major media outlets picked up the story. We saw quotes from Microsoft saying that changes were being made to the process. I chuckled when I read that; I’d been hearing the same line for at least a year and I knew what little value where was in the statement.
One of my concerns with the promotion of Satya Nadella was that the poor quality of testing that blossomed under his watch in the Server and Tools group would spread to the rest of Microsoft. There was a time when major updates were tested heavily. That included automated testing tools, internal human testing, and external testing via Technical Adoption Programs (TAPs), and public beta/release candidate testing. Windows 7/Windows Server 2008 R2 was one of the best releases ever by Microsoft, thanks largely to huge testing programs after the colossal failure of Vista. Those days are long over; see Windows 8 as evidence.
- Related: Microsoft Botches Six Windows Patches (August 2013)
Recently Microsoft announced that 18,000 employees would be made redundant. 12,500 of those were predictably from the just acquired Nokia. One might think that superfluous staff such as Xbox Entertainment Studios and the never-profitable Surface would make up the majority of those layoffs. Mary Jo Foley reported that:
“Under the new structure, a number of Windows engineers, primarily dedicated testers, will no longer be needed.”
That quote was from a memo from Microsoft’s unified Operating System Group, under Executive Vice President Terry Myerson, to his staff in the client OS group. While that is not evidence of a larger Microsoft action, it sure suggests a mentality to me that human testing is no longer valued in Redmond. While I see some value in automated testing for stress testing and verifying that predictable things should happen, I am a strong believer that humans cannot be replaced for edge case testing and simple curiosity (what happens if …?) If Microsoft is culling the numbers of testers to replace them with “dumb robots” then there is a predictable outcome.
Those of us who have seen, helped troubleshoot, or covered the issues of the past 2 years of update rollups coming out of the Server & Tools group understand what this might mean for a greater Microsoft: products will be of a poor quality. Maybe Satya Nadella should ask Detroit what that did for the US car industry when they let quality drop after the Japanese auto industry moved in the opposite direction. Feedback has made no impression on Microsoft; maybe sales need to drop or legal action (a major customer or a class action suit) will be the only way to get the attention of the plethora of corporate vice presidents that run the show.