Manage Windows Features with PowerShell
- Blog
- PowerShell
- Post
Configuring and managing servers these days can be a time consuming process, unless you work more efficiently and smarter. For example, suppose you need to add a new server feature. Are you going to go to the server, open up server manager, scroll around to find where to add a feature or role and then click through the wizard? Or would you prefer to type a few commands and go to lunch?
With the increasing role of Server Core machines, GUIs aren’t even an option. Sure, you could use the Server Manager console from RSAT, but that still takes time to get going. What if you need to manage a feature on 10 servers?
Today I’ll show you what Windows features and roles were installed on a Windows Server 2008 R2 system using Windows PowerShell and the ServerManager module. In part two, I’ll add a feature or role to Windows features with PowerShell.
Manage Windows Server 2008 R2 with PowerShell
Your answer lies with Windows PowerShell – what else! I’m also talking about managing servers running Windows Server 2008 R2, ideally from a Windows 7 desktop. What makes this all possible is the ServerManager module. Unfortunately, this module only resides on server operating systems. I’ve never been able to find a way to load it on Windows 7, but that’s ok. Because the server is also running PowerShell 2.0 with remoting enabled, I can do everything from a remote PowerShell session.
If you need to automate the process across a number of servers, you can use the following as part of a script or scriptblock that you could execute with Invoke-Command. For now I’m going to deal with a single server.
petri.com/wp-adminPS C:\> enter-pssession CHI-FP01 -Credential globomantics\administrator
[chi-fp01]: PS C:\Users\administrator.GLOBOMANTICS\Documents> cd \
[chi-fp01]: PS C:\> dir
I now have a remote session using alternate credentials. The next step is to load the necessary module.
petri.com/wp-admin[chi-fp01]: PS C:\> import-module ServerManager
There are only 3 commands we have to work with, but that is plenty.
petri.com/wp-admin[chi-fp01]: PS C:\> get-command -Module ServerManager | Select Name
Name
—-
Add-WindowsFeature
Get-WindowsFeature
Remove-WindowsFeature
The cmdlet names should be self-explanatory. First, let’s see what features are already installed using Get-WindowsFeature.
petri.com/wp-admin[chi-fp01]: PS C:\> Get-WindowsFeature
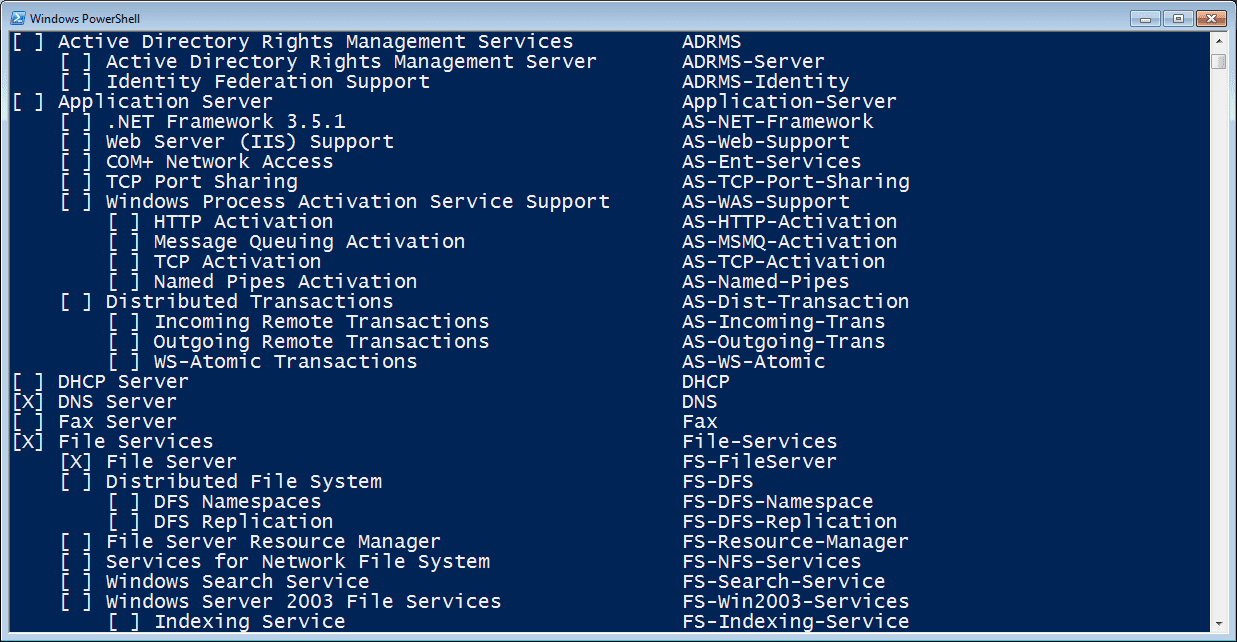
You’ll see a nicely formatted listing of all features with an X indicating those that are installed. See Figure 1:
Figure 1 Get-WindowsFeature OutputBut don’t let the output fool you: we’re still dealing with objects.
petri.com/wp-admin[chi-fp01]: PS C:\> get-windowsfeature dns | select *
DisplayName : DNS Server
Name : DNS
Installed : True
FeatureType : Role
Path : DNS Server
Depth : 1
DependsOn : {}
Parent :
SubFeatures : {}
SystemService : {dns*}
Notification : {}
BestPracticesModelId : Microsoft/Windows/DNSServer
AdditionalInfo : {HelpLink, FeedbackLink, TechCenterLink, NumericId…}
Knowing the property names, I can modify the command to only find installed features.
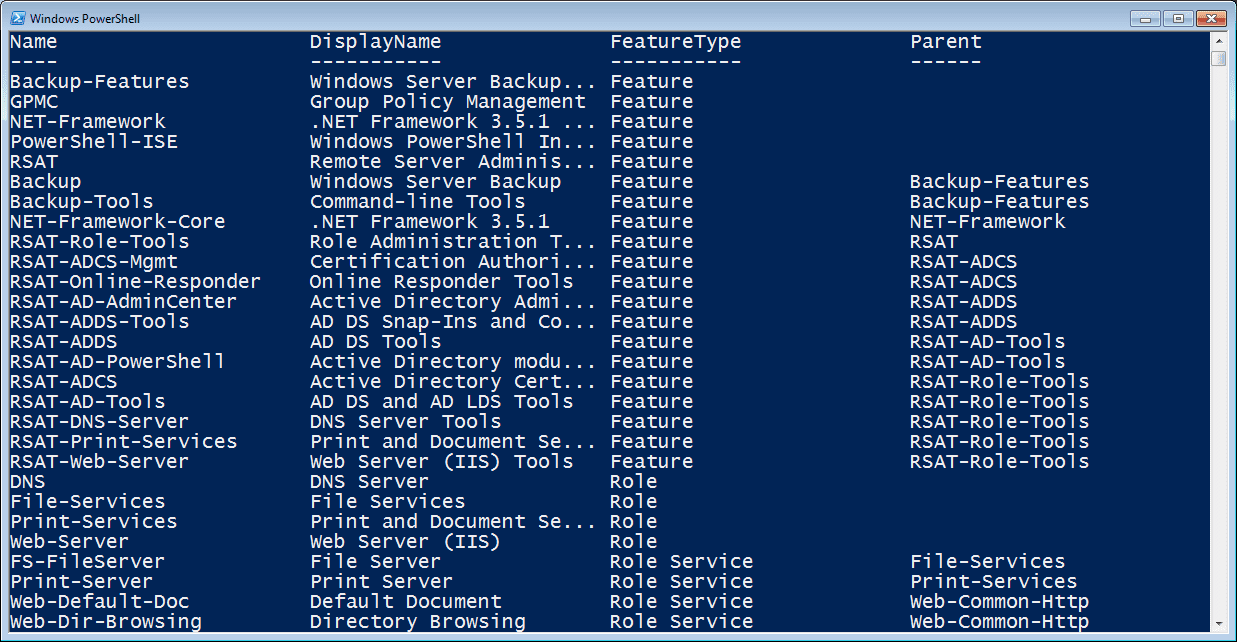
petri.com/wp-admin[chi-fp01]: PS C:\> get-windowsfeature | Where {$_.Installed} | Sort FeatureType,Parent,Name | Select Name,Displayname,FeatureType,Parent
This one line command finds all installed features, sorted by a few properties in order and then displays a subset of object properties. Figure 2 shows the result:
Figure 2 Installed FeaturesThinking of building an audit trail? It isn’t much more work to export results to a CSV, XML or plain text file.
Or you might want to drill down to a specific feature or role.
petri.com/wp-admin[chi-fp01]: PS C:\> $fs=get-Windowsfeature File-Service
[chi-fp01]: PS C:\> $fs | select *
DisplayName : File Services
Name : File-Services
Installed : True
FeatureType : Role
Path : File Services
Depth : 1
DependsOn : {}
Parent :
SubFeatures : {FS-FileServer, FS-DFS, FS-Resource-Manager, FS-NFS-Services…}
SystemService : {}
Notification : {}
BestPracticesModelId :
AdditionalInfo : {HelpLink, FeedbackLink, TechCenterLink, NumericId…}
Some of these properties are going to be nested objects. For example, SubFeatures will provide a list of additional features.
petri.com/wp-admin[chi-fp01]: PS C:\> $fs.SubFeatures
FS-FileServer
FS-DFS
FS-Resource-Manager
FS-NFS-Services
FS-Search-Service
FS-Win2003-Services
FS-BranchCache
But these are simply names, which means I can pipe them to Get-WindowsFeature to see if any of them are installed.
petri.com/wp-admin[chi-fp01]: PS C:\> $fs.SubFeatures | Get-WindowsFeature
Display Name Name
———— —-
[X] File Server FS-FileServer
[ ] Distributed File System FS-DFS
[ ] File Server Resource Manager FS-Resource-Manager
[ ] Services for Network File System FS-NFS-Services
[ ] Windows Search Service FS-Search-Service
[ ] Windows Server 2003 File Services FS-Win2003-Services
[ ] BranchCache for network files FS-BranchCache
Now I can see what needs to be installed.
Configuring and managing servers is a task made easier by using Windows PowerShell. In the next article, we’ll look at adding and removing features.