Manage Network Adapters with PowerShell: Troubleshooting
- Blog
- Networking
- Post
Over the last few articles I’ve been exploring and demonstrating PowerShell tools for managing network adapters and configuring network adapters in Windows Server 2012. If you missed either of those articles, you should read them first. In this article we’ll look at some cmdlets that might come in handy when troubleshooting a networking issue, and all of these commands can be run remotely. Everything I’m going to show you requires PowerShell 3 and Windows Server 2012. These commands will also work with Windows 8, but that’s a bonus.
Get Protocols
The first item you might want to check is protocol configuration. There are IP version specific cmdlets that will return useful information.
PS C:\> Get-NetIPv4Protocol -cimsession chi-app01 DefaultHopLimit : 128 NeighborCacheLimit(Entries) : 1024 RouteCacheLimit(Entries) : 128 ReassemblyLimit(Bytes) : 8384928 IcmpRedirects : Disabled SourceRoutingBehavior : DontForward DhcpMediaSense : Disabled MediaSenseEventLog : Disabled IGMPLevel : All IGMPVersion : Version3 MulticastForwarding : Disabled GroupForwardedFragments : Disabled RandomizeIdentifiers : Enabled AddressMaskReply : Disabled PSComputerName : chi-app01
To query a remote computer you can use a computer name, IP address, or an existing CIMSession. Although if you need to specify alternate credentials you will need to create a CIMSession.
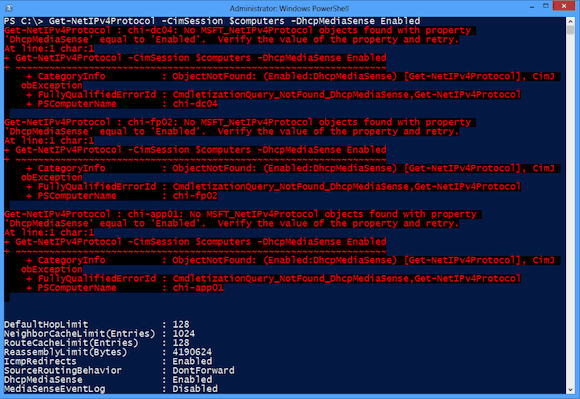
A useful feature of this cmdlet is that you can filter in place by a number of protocol settings. This is very helpful when you want to query multiple computers. For example, I need to see which of my servers are still configured for the protocol stack to pay attention to DHCP.
PS C:\> $computers = "chi-dc04","chi-fp02","chi-app01","chi-dev01" PS C:\> Get-NetIPv4Protocol -CimSession $computers -DhcpMediaSense Enabled
Unfortunately, as you can see below in Figure 1, the cmdlet throws an exception for computers that do not have the specified setting.
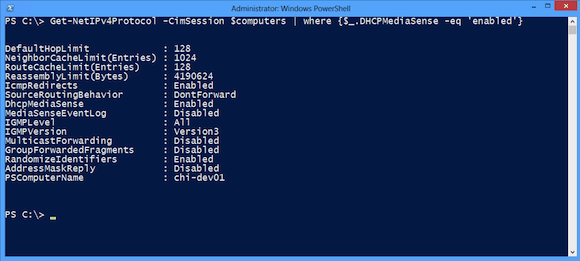
I could run the command suppressing errors, but that might mask other problems. Or I can simply filter all the results with Where-Object.
PS C:\> Get-NetIPv4Protocol -CimSession $computers | where {$_.DHCPMediaSense -eq 'enabled'}
As you can see in Figure 2, this is a bit nicer.
I can get similar results for the IPv6 stack.
PS C:\> Get-NetIPv6Protocol -CimSession CHI-Dev01 DefaultHopLimit : 128 NeighborCacheLimit(Entries) : 1024 RouteCacheLimit(Entries) : 128 ReassemblyLimit(Bytes) : 4190624 IcmpRedirects : Enabled SourceRoutingBehavior : DontForward DhcpMediaSense : Enabled MediaSenseEventLog : Disabled MldLevel : All MldVersion : Version2 MulticastForwarding : Disabled GroupForwardedFragments : Disabled RandomizeIdentifiers : Enabled AddressMaskReply : Disabled UseTemporaryAddresses : Disabled MaxDadAttempts : 5 MaxValidLifetime : 7.00:00:00 MaxPreferredLifetime : 1.00:00:00 RegenerateTime : 00:00:05 MaxRandomTime : 00:10:00 PSComputerName : CHI-Dev01
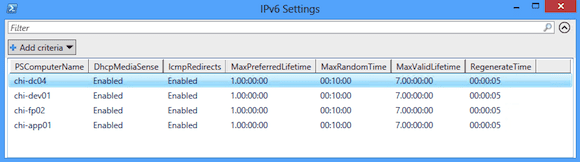
If you want to see several properties across multiple computers, I recommend using Out-Gridview.
PS C:\> Get-NetIPv6Protocol -cim $computers | Select PSComputername,DHCP*,ICMP*,*Time | Out-Gridview -title "IPv6 Settings"
As you can see above in Figure 3, I haven’t done much with IPv6, but you could use a similar technique with the IPv4 cmdlet.
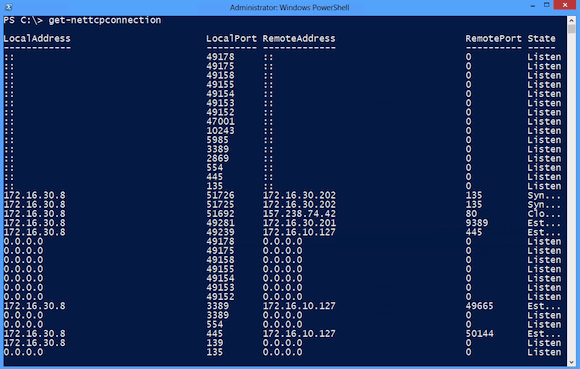
Get-NetTCPConnection
In the “old days,” IT pros used command line tools like NETSTAT.EXE to examine what ports were in use and what connections a server might have. But it was a command line tool, and you had to run it on the server. Today we can get the same information through PowerShell using Get-NetTCPConnection.
More than likely, you will want to limit the display to make it more “netstat-like.”
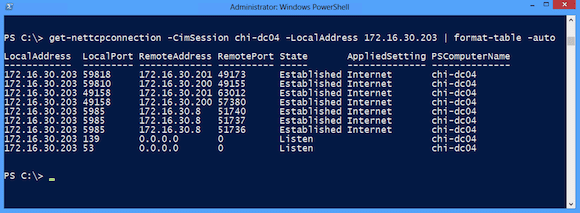
PS C:\> get-nettcpconnection -CimSession chi-dc04 -LocalAddress 172.16.30.203 | format-table -auto
I formatted the output to make it a little easier to read in Figure 5 (as shown below).
The LocalAddress is the IP address of the remote server. We can also query the remote address as well.
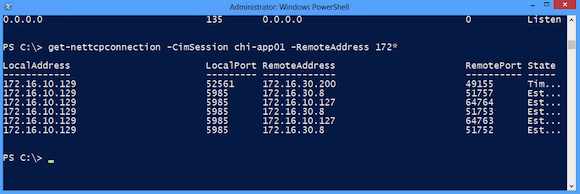
PS C:\> get-nettcpconnection -CimSession chi-app01 -RemoteAddress 172*
Figure 6 shows all the connections from CHI-APP01 to any address that starts with 172.
Or if I just want the remote IP address, I can get a unique list.
PS C:\> get-nettcpconnection -CimSession chi-app01 -RemoteAddress 172* | select RemoteAddress -unique RemoteAddress ------------- 172.16.10.127 172.16.30.200 172.16.30.8
And because we have objects, there are some interesting ways we can use this.
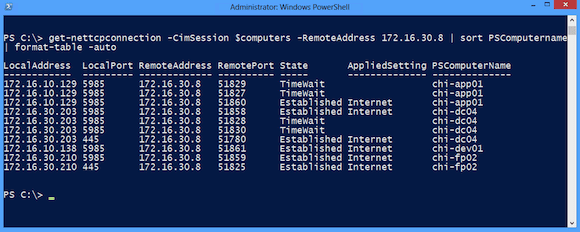
PS C:\> get-nettcpconnection -CimSession $computers -RemoteAddress 172.16.30.8 | sort PSComputername| format-table –auto
Figure 7 (above) shows all the remote computers that have a remote connection to 172.16.30.8. I can do the same thing with ports.
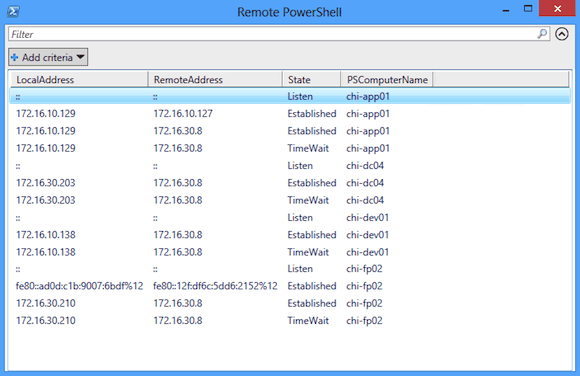
PS C:\> get-nettcpconnection -CimSession $computers -localPort 5985 | sort PSComputername,State| Select LocalAddress,RemoteAddress,State,PSComputername -unique | out-Gridview -title "Remote PowerShell"
Now I’ve searched all my Windows Server 2012 computers for those that have a remote PowerShell session open on the default port, 5985.
Get-NetRoute
The last cmdlet that might come in handy is Get-NetRoute. This is PowerShell equivalent to the legacy Route.exe utility. But this works remotely!
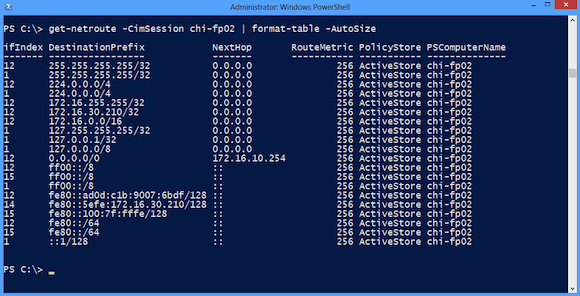
PS C:\> get-netroute -CimSession chi-fp02 | format-table –AutoSize
You can see my result below in Figure 9.
The ifIndex property is the Interface Index number which we looked at in earlier article. In fact, we can get a net adapter and then discover its associated routes.
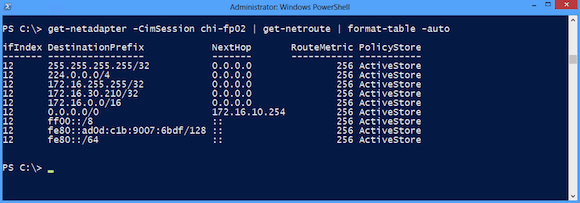
PS C:\> get-netadapter -CimSession chi-fp02 | get-netroute | format-table –auto
Even though the output in Figure 10 (shown below) doesn’t explicitly show it, this is the route table for CHI-FP02, which only has a single adapter.
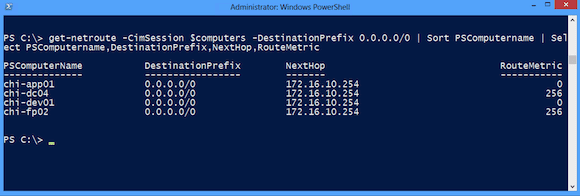
Or perhaps I want to verify that all my servers have the correct default gateway. Here’s a one line command:
PS C:\> get-netroute -CimSession $computers -DestinationPrefix 0.0.0.0/0 | Sort PSComputername | Select PSComputername,DestinationPrefix,NextHop,RouteMetric
Based on what I see in Figure 11, everything looks good.
If you have a more complex environment with multi-homed servers, this cmdlet could be a lifesaver in tracking down a network configuration problem.
As I’ve been reminding you in each article, please take the time to read complete help and examples for all the cmdlets I’ve been demonstrating. Now that we’ve seen all the information we can gather, we need to explore what it takes to set and configure. We’ll start that discovery next time.